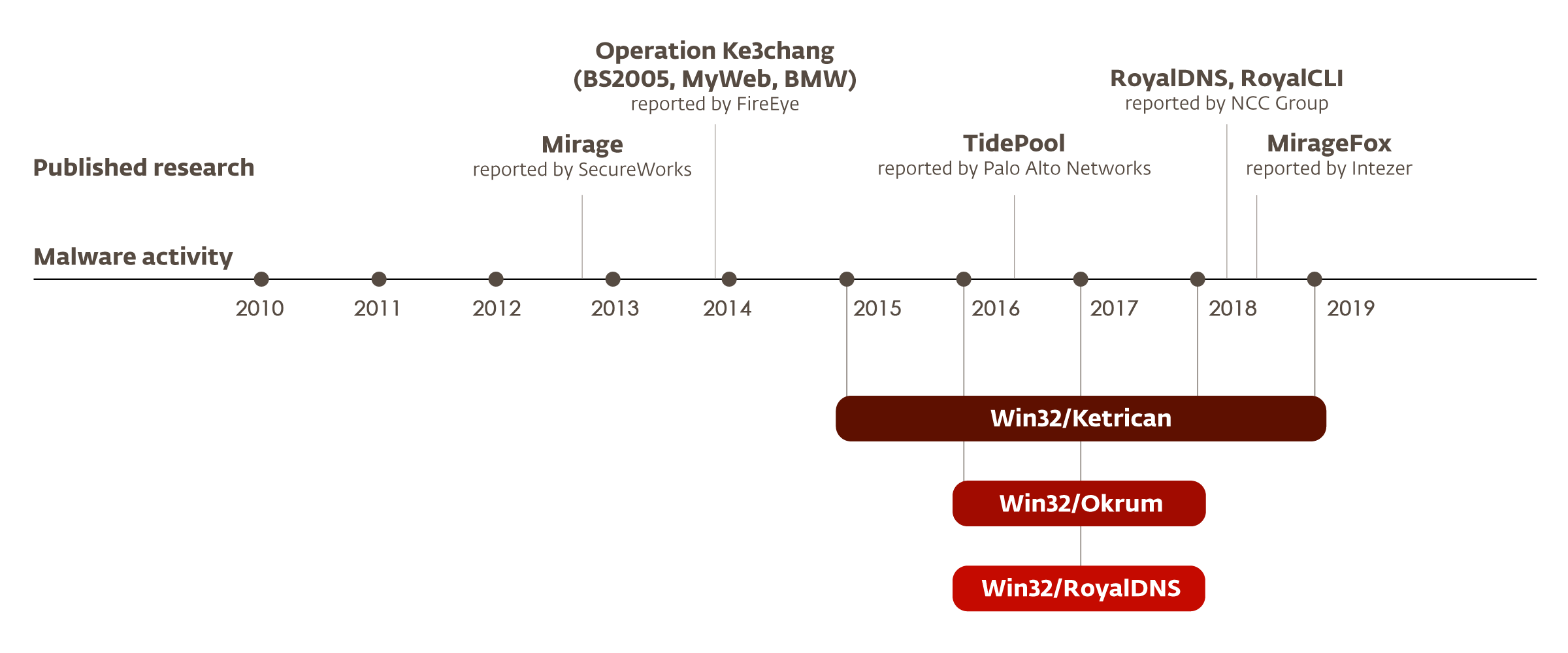
The 'Ke3chang', shadowy malware group believed to operate out of China also known as APT 15, has conducted cyber-espionage campaigns using remote access trojans and other malware since at least 2010.
And here, it was found that it has also target diplomats in in European and Central and South America using previously undocumented backdoor.
Slovakia appears to be a primary target for Ke3chang, but campaigns have also targeted Belgium, Croatia, Czech Republic in Europe, as well as Brazil, Chile and Guatemala in the Americas.
ESET researchers were able to link previous malware attributed to the group, with a backdoor called 'Okrum'. Analyzing the malware used in these attacks, the researchers found that it's a newer versions 'Ketrican'.
The company added that it had seen "detection evasion techniques" in the Okrum malware, as recently as March 2019.
"Besides the shared targets, Okrum has a similar modus operandi as previously documented Ke3chang malware. For example, Okrum is only equipped with basic backdoor commands and relies on manually typing shell commands and executing external tools for most of its malicious activity, which is a standard modus operandi of the Ke3chang group across its previously investigated campaigns," said ESET in a statement.
"The attacker's main goal is most likely cyberespionage, that's why they selected these targets."
What makes the malware unique is that, the "payload starts only after the left (physical) mouse button has been pressed at least three times."
This is to make sure that the target is real and functioning machines being used by the target.
Once deployed, Okrum can provide itself will full administrator privileges and collects information about the infected machine. This includes the computer name, username, host IP address and what operating system is installed.
The malware is also capable of issuing commands like downloading and uploading files, making hackers capable of stealthily stealing files, as well as executing shell commands and issuing updates.
Researchers have also spotted Okrum deploying additional tools like 'Mimikatz' which can act as as a keylogger and password stealer.
"Our analysis of the links between previously documented Ke3chang malware and the newly discovered Okrum backdoor lets us claim with high confidence that Okrum is operated by the Ke3chang group,” researchers wrote. “Having documented Ke3chang group activity from 2015 to 2019, we conclude that the group continues to be active and works on improving its code over time.”
The Okrum malware was found to have many commands similar to Ketrican, including sharing the same codes.
Researchers also found that because both malware target the same victims, they suggest a strong link between the two, even though some of the attacks were years apart.
"On top of that, we found that some diplomatic entities that were affected by the Okrum malware and the 2015 Ketrican backdoors were also affected by 2017 Ketrican backdoors," the researchers added.
With the campaign being active for almost a decade, it seems that the hackers are still evolving the tactics and methods of attacks.
Besides the Ketrican and Okrum, the researchers have also linked the 'RoyalDNS' backdoors to the threat group.
All three backdoors target the same type of organizations