Hackers are not only considered a crime, as many people have started considering it as a career. Some however, work as hackers, without their consent.
In the underground world where hackers lurk, there are times when manpower is just not enough for certain campaign. To recruit more people of the same kind, the financially motivated FIN7 cybercrime gang has founded a fictitious cybersecurity company called "Bastion Secure," in order to recruit unwitting software engineers under the guise of penetration testing.
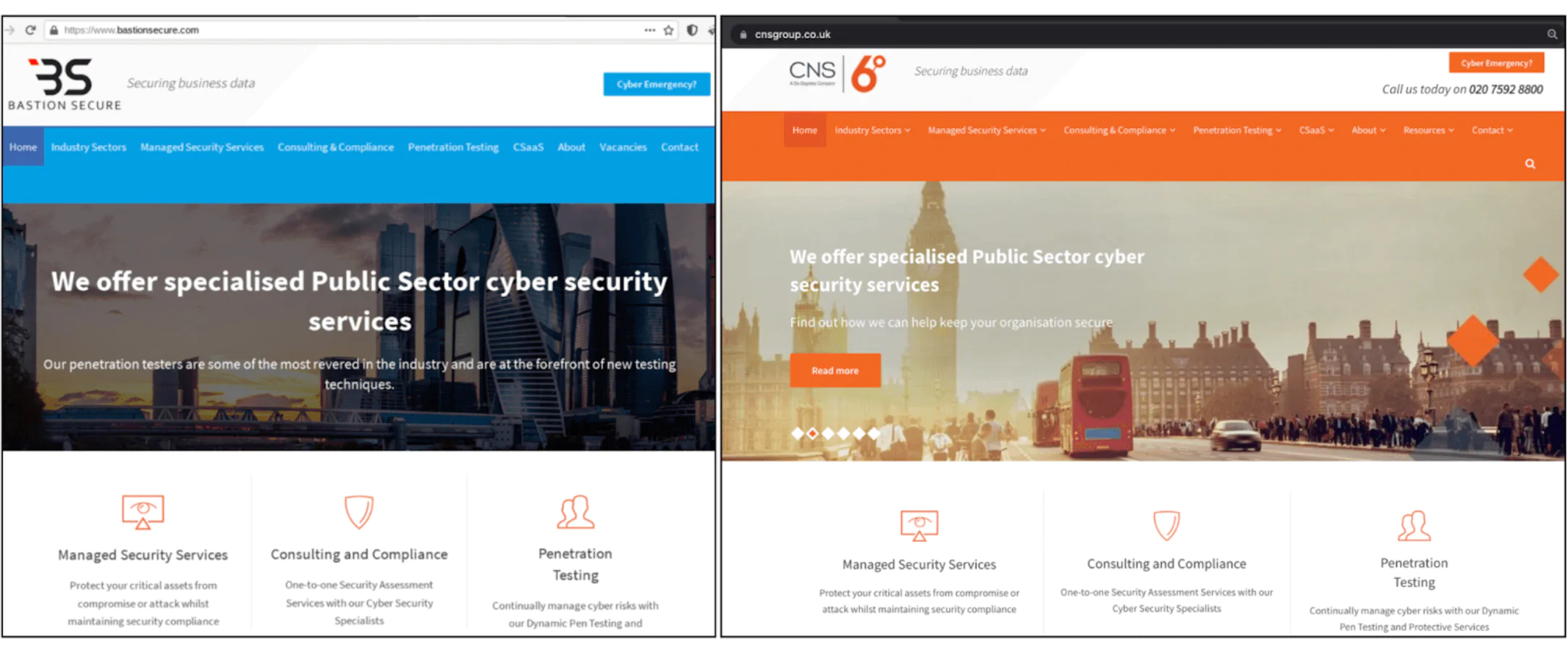
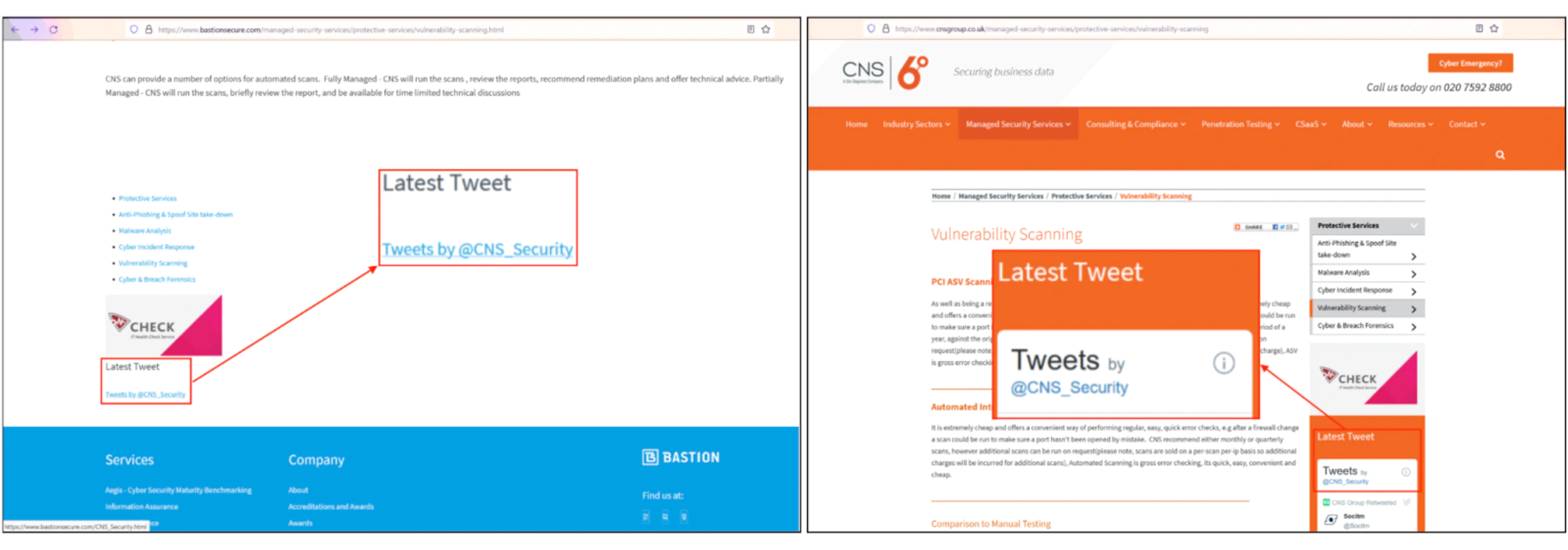
For authenticity, the hackers registered the company under the addresses of the a defunct UK-based company called Bastion Security (North) Limited. And for the content of the website, the hackers copied much from the website of Convergent Network Solutions Ltd., a legitimate cybersecurity company.
According to a report from Recorded Future's Gemini Advisory unit:
"FIN7 is adopting disinformation tactics so that if a potential hire or interested party were to fact check Bastion Secure, then a cursory search on Google would return 'true' information for companies with a similar name or industry to FIN7's Bastion Secure."
FIN7, also known as Carbanak, Carbon Spider, and Anunak, is no stranger to creating companies.
The gang is notorious, and has a strong track record of hacking, restaurants, gambling venues, and hospitality industries in the U.S. by infecting their point-of-sale (POS) systems with malware designed to harvest credit and debit card numbers.
The stolen data are then used, and sold for profit on underground marketplaces.
But this time, the gang created a website by compiling data from other legitimate cybersecurity firms.
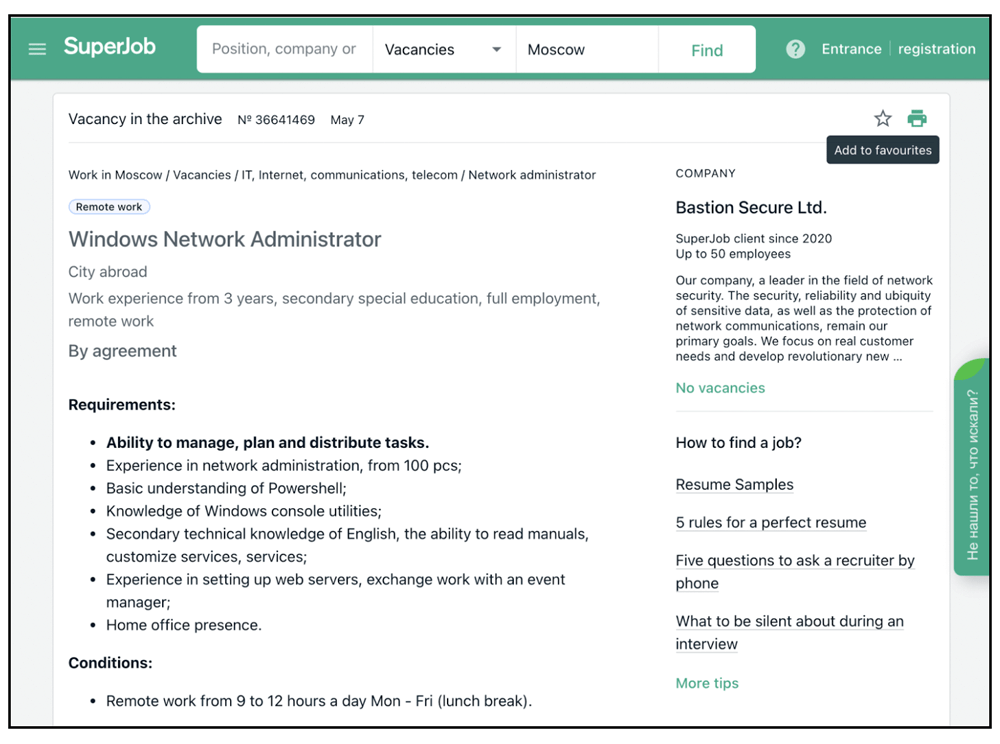
And the job being advertised, include software engineering with knowledge on C++, PHP, and Python programmers, and experience on becoming system administrators, and reverse-engineers on popular job boards.
It is said that FIN7 wants to trick unwilling and unsuspecting people into applying for the job.
At first, the researchers were suspicious as the job listing included tools needed for practice assignments during the interview process.
Digging things further, the researchers found that the tools are components of the post-exploitation toolkits Carbanak and Lizar/Tirion, both of which have been previously attributed to the group and can be leveraged to compromise POS systems and deploy ransomware.
At first, the hackers conceal pretty much of the job description, in order to not look too suspicious.
But when someone passes the first test, the next stage of the hiring process is more apparent.
It is said that Bastion Secure needs representatives providing access to a so-called client company's network and asking prospective candidates to gather information on domain administrators, file systems, and backups.
This suggests that what Bastion Secure is searching for someone to conduct ransomware attacks.
"Bastion Secure's job offers for IT specialist positions ranged between $800 and $1,200 USD a month, which is a viable starting salary for this type of position in post-Soviet states," the researchers said. "However, this 'salary' would be a small fraction of a cybercriminal's portion of the criminal profits from a successful ransomware extortion or large-scale payment card-stealing operation."
By paying "unwitting 'employees' far less than it would have to pay informed criminal accomplices for its ransomware schemes, the Bostion Secure scheme enables the hackers at FIN7 to obtain the talent they need to carry out its criminal activities, while simultaneously retaining a larger share of the profits.
And all that by playing things safe.
"Although cybercriminals looking for unwitting accomplices on legitimate job sites is nothing new, the sheer scale and blatancy with which FIN7 operates continue to surpass the behavior shown by other cybercriminal groups," the researchers said, adding that the group is "attempting to obfuscate its true identity as a prolific cybercriminal and ransomware group by creating a fabricated web presence through a largely legitimate-appearing website, professional job postings, and company info pages on Russian-language business development sites."