The process of signing in has never been easier.
With username/email and password combination, the process can differentiate an unwanted hacker from the CEO of the company, for instance. This is why the process has long been sought as the best way to protect information and privacy.
But as technology evolves, that simple signing in process should be made harder for hackers, but still as easy as possible for legitimate users.
This is where two-factor authentication comes in.
With it, users need to have a second device to authenticate their first signing in process. While it's easy to use, it's annoying because people can feel flustered with the extra process. It's like the peak first-world problems, and many people are disliking it.
But considering privacy, if users have any doubt whether the extra process is worth their time, Google answered that keeping people safe by trading off conveniences is priceless.
Google said in a blog post:
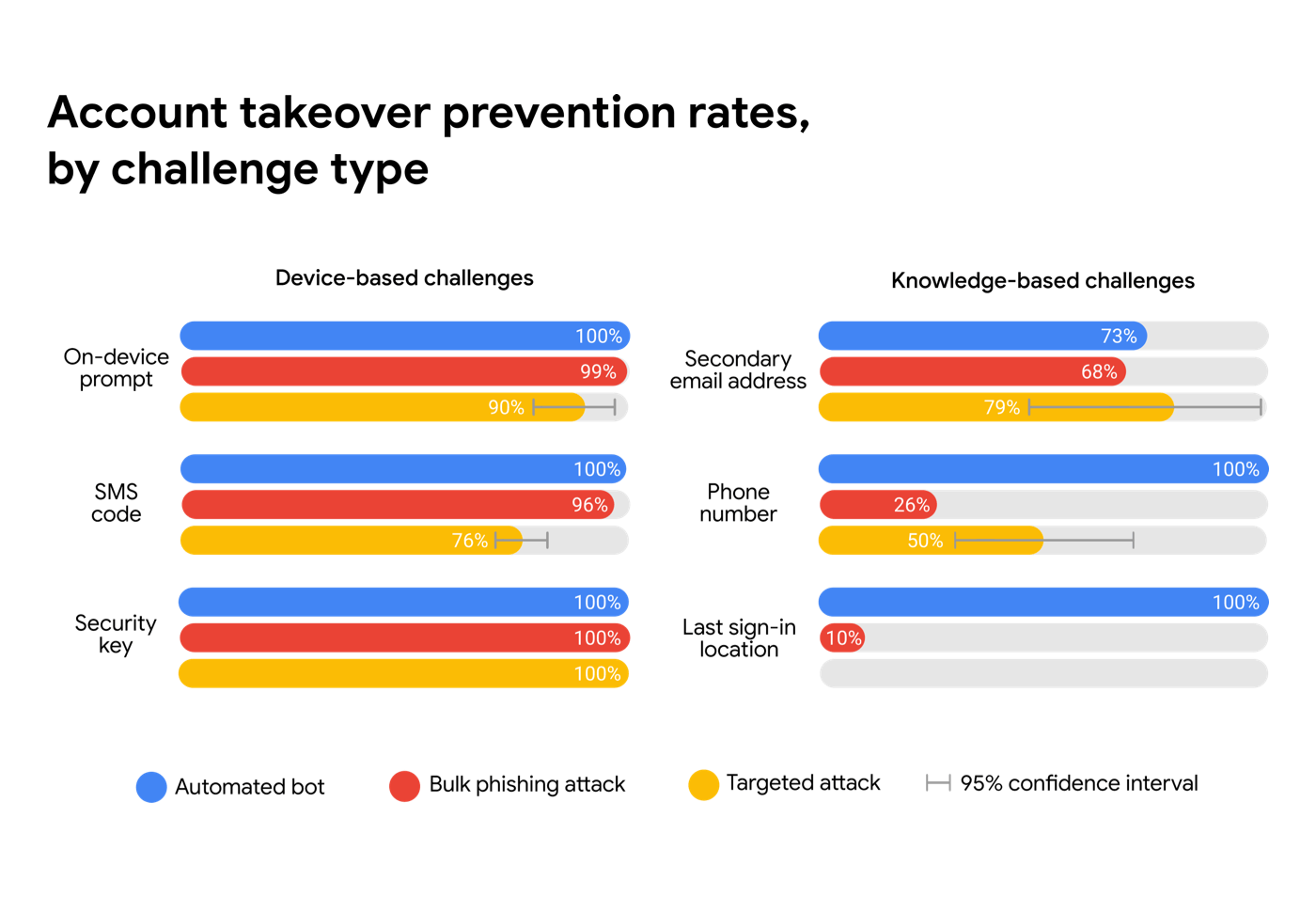
"We teamed up with researchers from New York University and the University of California, San Diego to find out just how effective basic account hygiene is at preventing hijacking."
"Our research shows that simply adding a recovery phone number to your Google Account can block up to 100% of automated bots, 99% of bulk phishing attacks, and 66% of targeted attacks that occurred during our investigation."
Google manages this using automation.
When it detects a suspicious sign-in attempt (like from new location or device), Google can ask for additional proof that the user is really who what they say they are. This can be done by confirming that they have access to a trusted phone, or answering a question where only the user knows the correct answer.
Google continued by saying that:
How about when users didn't register their recovery phone number? If so, Google may fall back to the weaker knowledge-based challenges, like recalling the person's last sign-in location. To prevent bot logins, this can still be effective, but for phishing, the protection rate can drop to as low as 10%.
This is because phishing pages and targeted attackers can trick users into revealing any additional identifying information Google might ask them for.
Google suggest five tips for users to properly protect their Google account:
- Set up a recovery phone number or email address, and keep it updated.
- Use unique passwords for your accounts.
- Keep your software up to date.
- Go a step further by setting up two-factor authentication.
- Take the Google Security Checkup.
