
In the era of biometrics, the old and traditional method of entering login credentials with passwords is still irreplaceable.
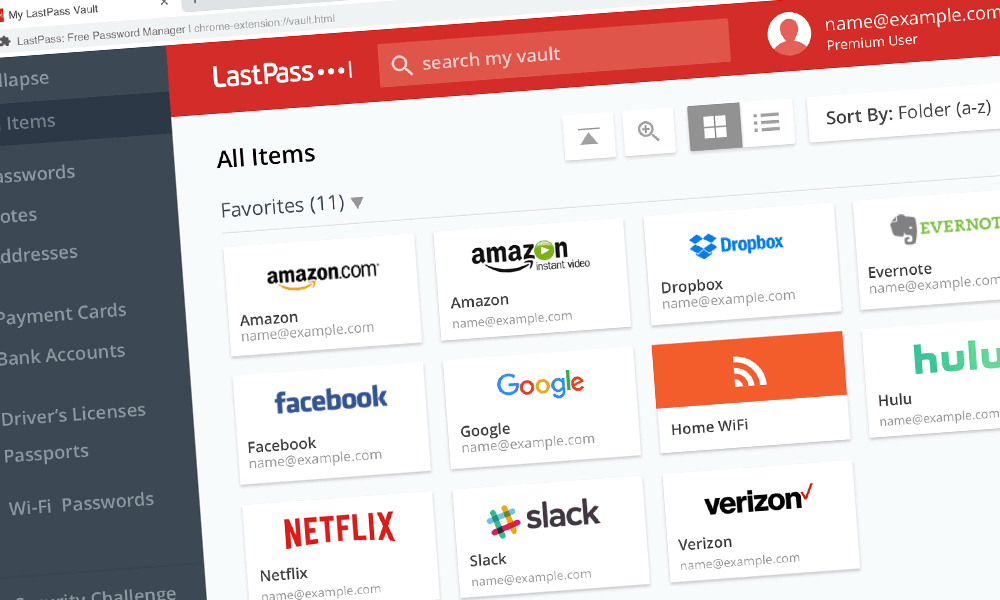
With the many passwords people are expected to use and memorize, password managers are the best way to go. These software should help many in managing their login credentials on multiple online services and platforms. One of the most popular, is LastPass.
Ironically, LastPass had a serious flaw, which potentially allowed malicious websites to access the last password entered by users' browser extension.
This method used is called 'clickjacking', in which can be described when users are tricked into clicking something that’s disguised as a different element, thus accidentally revealing confidential information, or even take control.
This LastPass bug was discovered by Google Project Zero researcher Tavis Ormandy on August 30th.
LastPass could leak the last used credentials due to a cache not being updated. This was because you can bypass the tab credential cache being populated by including the login form in an unexpected way! https://t.co/bfLdDzSWS5
— Tavis Ormandy (@taviso) September 16, 2019
According to LastPass in its statement
In details of the flaw - which have been made public by Ormandy after LastPass fixed it - reveals that it could’ve been exploited by executing a malicious JavaScript code which could be embedded on any website masked behind a Google Translate URL.
The attacker could then trick users into visiting the link, and subsequently extract credentials from a previously visited site, because the extension somehow failed to clear its cache.
LastPass noted that the issue was specific to Chrome and Opera. But as a precaution, the company said that it has pushed the fix to all browser, just in case.
Ormandy labeled the bug as high severity, but LastPass tried to minimize its scope, saying that the flaw "revealed a limited set of circumstances on specific browser extensions that could potentially allow an attacker to create a clickjacking scenario."
But nevertheless, the bug has been fixed after LastPass quickly worked to develop an update, and verified the solution was comprehensive with Ormandy
This particular bug showed that even the tools used to protect, can still be flawed, exposing security risks with huge potential damage.
Other password managers can have their own flaws yet to be discovered. But that doesn’t mean password managers are bad for security. In reality, password managers are handy tools, and are considered a much more secure alternative to storing passwords rather than in browsers or on notes, or on written paper, from where credentials can easily fall to the wrong hands.
As a reminder, LastPass recommends people to follow the general best practices for added online security:
- Beware of phishing attacks, and never click on links from unknown people, or that seem out of character.
- Always enable multi-factor authentication whenever possible.
- Never reuse master password, and never disclose it to anyone.
- Use different, unique passwords for every online account.
- Keep computers malware-free by running antivirus with the latest detection patterns and keeping software up-to-date.
