
Google's App Engine wasn't originally designed for developers to evade government censors. However, it has offered one, and it's called "domain fronting."
What domain fronting does, is wrapping communications to a service with a request to an otherwise innocuous domain or UP address range. In Google's case, it uses Google's. Over the years, developers have been able to conceal requests to domains that are otherwise blocked by the government, corporate or ISP.
Domain fronting has been used by many, for both good and bad uses.
Like for example, it has been used by encrypted messaging apps such as Telegram and Signal, anti-Chinese censorship services, the Tor network, some VPNs, state-funded malware campaigns and even data theft affiliation by hackers.
And Google is having enough of them.
It began on April 13th, when Tor users noticed that domain fronting has been disabled. When the issue was traced, it was found that Google made changes to how its network architecture work.
A Google representative said that domain fronting had never been officially supported by Google, saying that:
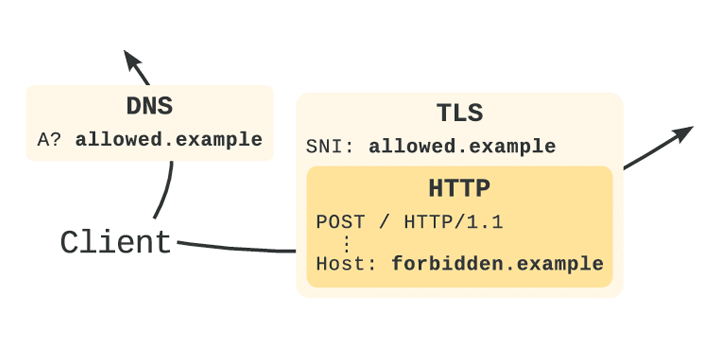
How domain fronting works, is by manipulating secure HTTP protocol (HTTPS) and the Transport Layer Security (TLS) standard. This enables it to fool deep packet inspection systems and firewall rules about the intended destination of a web request, and exploits the functionality of content delivery networks (CDNs).
When requesting something on the web, domain names only show up three times:
First, as part of a DNS query for the IP address of the site; second, in the Server Name Indication (SNI) extension of TLS that tells a server with multiple websites which domain the request is for; and third, in the HTTP 'host' header of the web request.
For HTTP traffic, all three of those domain names are visible to censors. But when using HTTPS, the HTTP header is encrypted.
In domain fronting, the DNS request and SNI extension use the domain name and IP of an unblocked host. In this case, it's Google's. Here, the HTTPS header contains the actual destination, which the request is then forwarded to, as long as it's part of the same CDN (usually a proxy server, VPN, Tor).
As a result, anyone in between the client and the CDN (from the government, ISP, corporate or others), the traffic appears to be going to a harmless site, but it is in fact, a traffic that got re-routed to its intended location.
Google in supporting domain fronting isn't what it was intending in the first place. This practice has the potential to hard its business, as Google too, can suffer from a ban if its domains and IPs are blocked. Domain fronting can also give a major impact to Google's other services and paying customers.
And as it doesn't support domain fronting anymore, Google is met with criticisms, including from Edward Snowden.
This is because previously, Google has long claimed to support internet freedom around the world. Domain fronting has meant that Google allowed potentially millions of people to experience a freer internet and enjoy their human rights.
And disabling it means that Google is killing an absolutely critical protection for people in places like Iran, China, and Russia trying to reach uncensored news and chat.
Previously, Telegram was ordered to be blocked by Roskomnadzor, Russia's telecommunications authority. But Russia experienced difficulties in banning the app because it uses domain fronting. Banning multiple domain addresses and IPs resulted in Russia in blocking services that use Google and Amazon Web Services addresses. As a result, this crippled the internet in the country.
Following Google, Amazon also made technical changes to stop the practice of domain fronting.
