
Many Android phones are already plagued with bloatware apps. Apparently, many of these apps aren't only useless, as they also pose security risks.
According to some users discussing their problems in a Reddit's /r/Androiddev subreddit, many Android phones can apparently show unwanted notifications, show ads inside stock apps, show full-screen ads even on the home screen and the lock screen.
Essentially, the apps look like any other app listings from the Play Store, but when they are showing ads and users try to close it, the app continues to run in the background.
These apps are bad for obvious reasons. And having the ability to show ads outside their own sandbox to interact with the rest of the phone, is certainly a security issue.
Making things worse, the apps can also install other apps without user intervention.
This poses the biggest security risk, as the bloatware apps can bypass Google Play Store's privacy measures, as well as other security features included inside Android.
It was later realized that the apps use Digital Turbine’s demand-side platform (DSP).
The DSP here means that advertisers can purchase advertising with the help of automation.
On Android, the only apps that can install apps without asking users' permission are system-level apps. This is possible because the apps are allowed to access Android's package manager without intervention.
Typically, the only apps that are granted such privilege, include OEMs and the Google Play Store.
And here, it was realized that Digital Turbine’s software can also be installed on a system level.
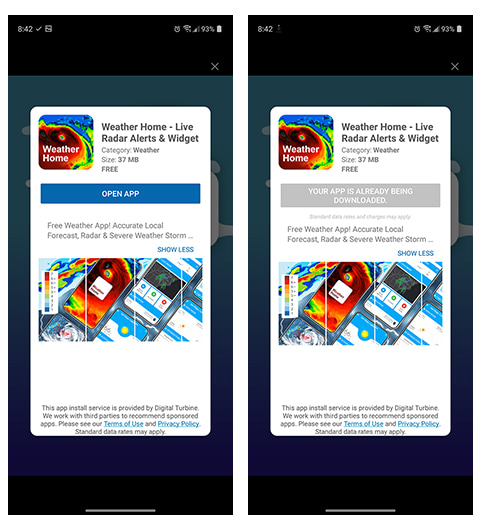
In one of the examples, a weather app called Weather Home tries to detect whether or not Digital Turbine’s software is installed. If it is installed, the app will leverage DT Ignite to circumvents the Google Play Store, and bypass Android's manual APK-install dialog.
The app in question has the ability to replace app launchers, runs intrusive ads, and consumes lots of battery because of its extensive load in the background.
DT Ignite is pre-loaded as a system app on many Android phones using carriers such as AT&T, Verizon, Claro, and Singtel.
The apps that leverage DT Ignite can serve ads or promote other apps, by connecting directly to Digital Turbine’s servers. This behavior can essentially be seen as malware. Digital Turbine as the company behind it, even owns a patent for this functionality.
Reddit user /u/omniuni who helped and explained on the subdreddit, said that he contacted Digital Turbine to clarify.
According to Digital Turbine, the Ignite app should never be able to install an app without user interaction. The Reddit user was told that Digital Turbine's own documents stated that clicking an “x” or dismissing a dialogue should not install anything. Secondly, Digital Turbine maintains that apps distributed through Ignite have ads that are verified both before and after being installed.
These ads are registered with Google Play, and are delivered over a secure connection.
What's more, Digital Turbine said that it double-checks all the apps it promotes before and after the installation.
Following the revelation, the company reportedly also told the Reddit user that it is working on a more official response.
This is because for whatever reasons, no app should ever be installed on an Android device without users' consent.
Such ability is not only unethical, as it's also been issues with malicious apps.
It should be noted that DT Ignite has been around for years, and has been making rounds since at least 2014. Back then, Digital Turbine would allow carriers and phone manufacturers to silently install bloatware and apps on people's phones.
On its website, it offers services, like "one-click to install ad units" through its DSP services, Direct to Device, which allow advertisers to "place your app directly on new devices at the time of activation," and to "present your app to new users during device set up when they're actively engaged," and lots more.
