In films and games, hackers can hack without having to even touch their target's device. While facts and fictions are two different worlds, they can corelate.
Most hacks in real life require hackers to first plant a malware to the target's device in order to exploit existing bugs or open backdoors. Usually, this involves methods like sending phishing emails, male targets download a malware-ridden app and some others.
But not in this case.
Google Project Zero security researcher Ian Beer said that a variety of Apple iPhones and other iOS devices were vulnerable to an exploit that could have allowed hackers to read target's emails and other messages, see and download photos and videos, and even turn on the target device's sensors to potentially watch and listen through their iPhone’s camera and microphone.
And not just that, as the bug could also have allowed hackers to monitor their victims in real time, remotely reboot the target's device and even control their devices from a distance.
In other words, hackers could have complete access to a person's iPhone, without having the victims to even click on any suspicious links or download malware.
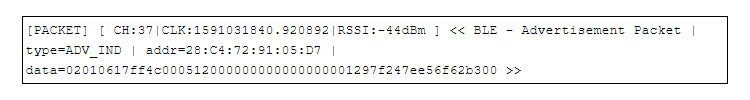
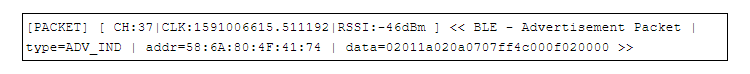
According to Beer, the vulnerability was caused by a bug on Apple Wireless Direct Link (AWDL). This is a protocol Apple uses to create mesh networks to support AirDrop and some other features.
Making things worse, Beer also found a way to force AWDL to turn on, even when users have it turned off.
This kind of security issue is big.
Fortunately, hackers should be in the target's AWDL range. What's more, Beer said that he has “no evidence that these issues were exploited in the wild”, and admitted that it took him six months to exploit the flaw, verify it, and demonstrate the exploit.
What this means, exploiting the AWDL bug wasn't easy.
Another good thing is that, Apple has patched the flaw in May 2020.
But still, Beer suggested iOS users to not take this lightly.
In a lengthy blog post, Beer said that:
"Instead, it should be: one person, working alone in their bedroom, was able to build a capability which would allow them to seriously compromise iPhone users they’d come into close contact with."
Beer has also uploaded another video on YouTube, showing how iPhones were vulnerable to "AWDL Broadcast Denial Of Service."
As for Apple, the Cupertino-based company didn't dispute that the exploit existed.
Apple even cited Beer in the iOS 12.4.7 security changelogs on its May 2020 updates that are linked to the CVE-2020-3843 vulnerability.
However, the company noted that just like in previous times, most of its users are quick in updating their devices' iOS versions.
Apple also pointed out that most of its iOS users are already using newer versions of the operating system that have been patched.
Read The Wi-Fi 'Evil Twin Attack', And Why Devices Shouldn't Connect Automatically To Public Hotspots
