When companies compete, they need to bring forward advantages. What this means, even when they compete for the same market, there are differences.
And those differences also include weaknesses. According to a research by cyber threat data provider WhoisXML API, it was suggested that not all VPN solutions are particularly trustworthy.
The researchers analyzed 1,540 IP ranges connected to known VPN data centers and service providers, and run them all through various blacklists: the Passive Spam Blocklist and the Feodo Tracker Botnet C2 IP Blocklists.
This was when the researchers found that 89 of them had previously been cited for malicious activity and were already blacklisted as a result.
And out of the 89 malicious IP addresses found by WhoisXML API, 29 of them were owned by DigitalOcean, a U.S.-based cloud infrastructure provider headquartered in New York City with data centers worldwide.
The fact that a single vendor was found to be in connection with the majority of the suspicious IP addresses, suggest that the policies on its VPN services may need to be reinforced.
In addition to that, the researchers at WhoisXML API also investigated the logs of a small private server from 9-13 August 2020.
The small server used a dynamic IP address that the team obtained from a home Internet Service Provider (ISP) and a free domain from a dynamic Domain Name System (DNS) service provider. It provides a web service and a Secure Shell (SSH) service on a non-standard port for interactive access.
After five days of tracking, the team found 904 IP addresses from which apparently malicious and unwanted SSH login attempts were made.
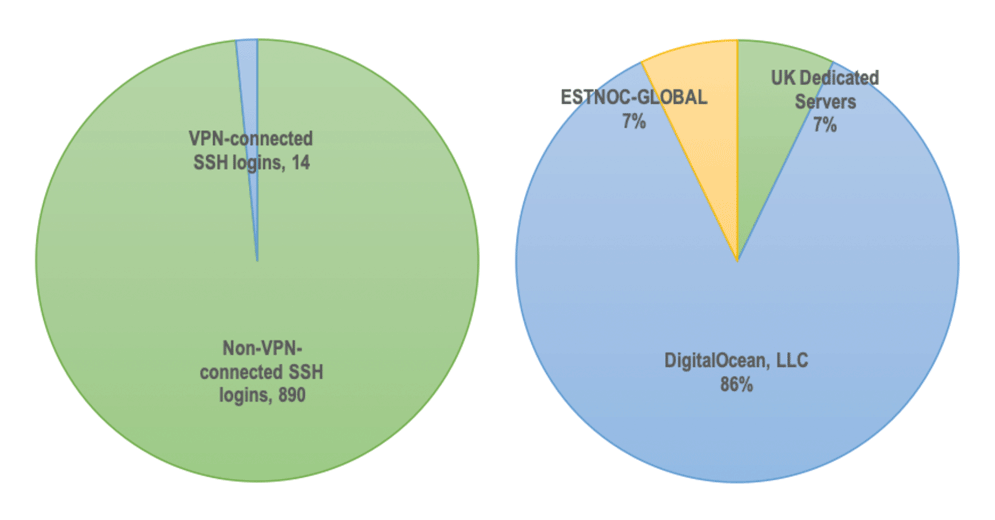
And out of the 904 SSH login attempts recorded on WhoisXML API's server log, 14 of them were from VPN-connected malicious IP addresses.
Breaking them down even further, out of the 14 IP addresses responsible for SSH login attempts, 12 of them owned by DigitalOcean.
"While the number is admittedly small, it remains a cause of concern, especially for companies who may be sharing a cloud server with a malicious user," the team said.
Only one IP address each belonged to UK Dedicated Servers and ESTNOC-GLOBAL, both of which are European cloud service providers.
Fortunately, none of the IP addresses recorded for SSH login attempts appeared on the team's blocklists.
However, this is not a guarantee that they are non-malicious.
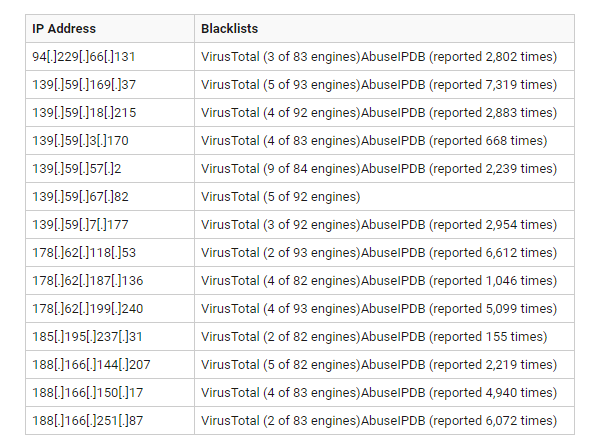
This is why the team ran each of the IP address that tried to login to the server via SSH to WhoisXML API's Threat Intelligence Platform, and further checked their status on VirusTotal and AbuseIPDB.
The result is that, again they found that more malicious IP addresses.
In fact, all 14 of them were dubbed malicious.
In conclusion, the team said that several VPN-connected IP addresses are already causing concerns.
And through the research, the team puts a higher emphasis on the IP addresses issued by DigitalOcean, as it owns a majority of the suspicious or even malicious IP addresses.
"The vendor may not have strict policies in place for its VPN service offering. Users can, in fact, access a tutorial at https[:]//anonymster.com/setup-openvpn-server-digitalocean/ to set up their own OpenVPN on a virtual machine (VM) that they can also purchase on the site for as little as US$5. Registering for the service doesn't even require users to dole out too many personal details, or go through a stringent verification process," the team said.
And if hackers set up an OpenVPN server and connects to it from a local device, they can avoid storing malicious code on the vendor's host, meaning that they can get away with data theft crime or other malicious activity.
With this fact, it's no wonder that hackers are utilizing poor security practices on some VPN providers to conduct illegal activities. And OpenVPN servers here, are easily abused.
