Discovered exploits in most modern processors could make computers, mobile devices, servers and others vulnerable to attacks.
Several researchers from member of Google's Project Zero team, Cyberus Technology, Graz University of Technology, University of Pennsylvania, University of Maryland, University of Adelaide and Data61, have found that a design technique used in chips from Intel, Arm and others could allow hackers to access data that are temporarily stored inside the memory of devices.
This includes, and not limited to: passwords, encryption keys or sensitive information open in applications.
The problem impacts processors going back for decades.
The flaws are known by the names of 'Meltdown' and 'Spectre'. What makes the flaws devastating is because they aren't unique to one particular chipmaker or device: they impact everything from phones to PCs and servers.
"It's not really one vendor's problem," Steve Smith, head of Intel's data center engineering operations, said during a conference call Wednesday. "It's not an issue with our product. It's not an issue with someone else's product." It's a general design issue that impacts most modern chips, he said.
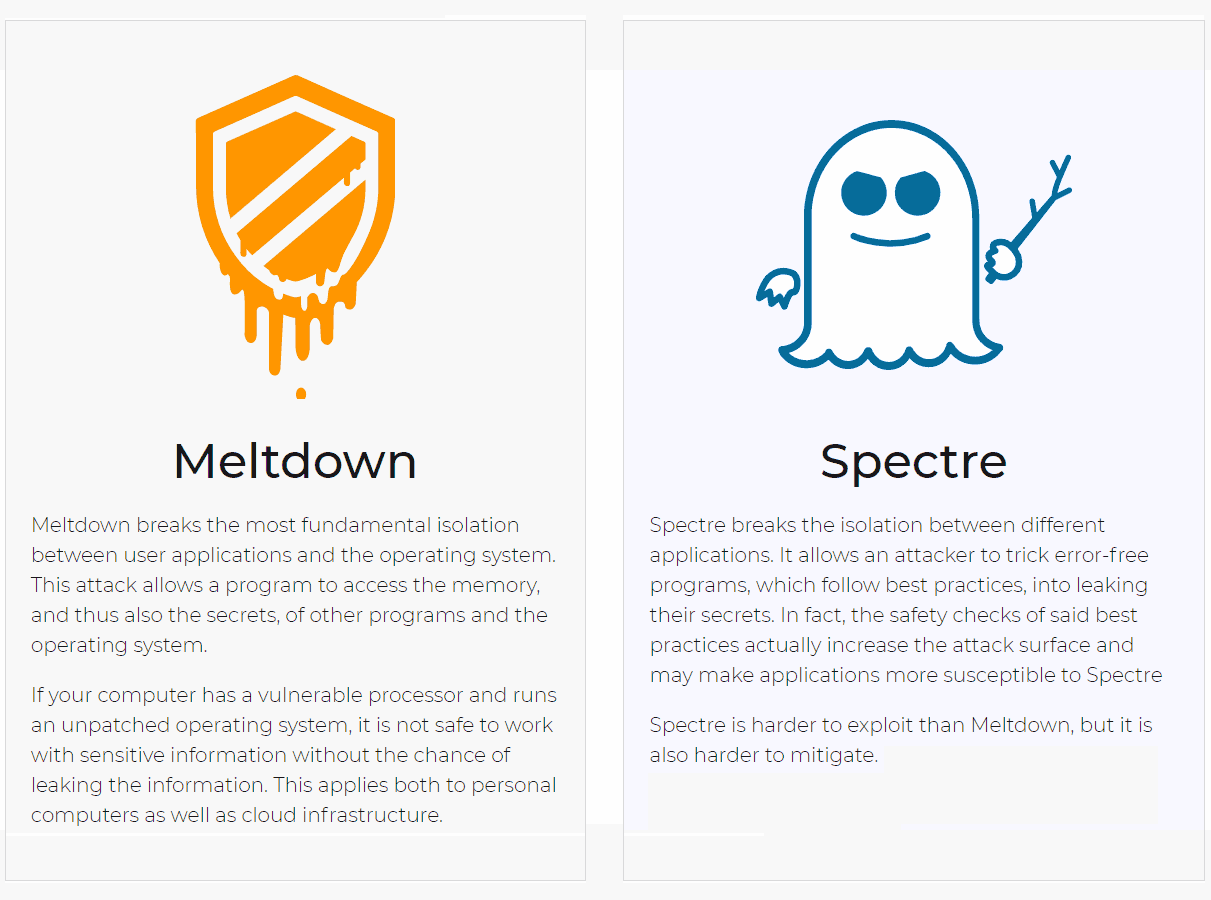
Meltdown
Meltdown flaw breaks the most fundamental isolation between user applications and the operating system. This allows a program access the device's memory, and obtaining information stored in it, including those from other programs and the operating system itself.
If the device has a vulnerable processor and runs an unpatched operating system, it is not safe to work with sensitive information without the chance of leaking the information. This applies both to personal computers as well as cloud infrastructure.
Spectre
Spectre breaks the isolation between different applications, allowing attackers to trick error-free programs, which follow best practices, makes it leak their secrets.
This exploit is more difficult, and also harder to mitigate.
According to reports, both Meltdown and Spectre aren't physical problems with the CPUs themselves, or a plain software bug. They are in between, present at the level of the processors’ architectures which have millions of transistors and logic units working together to carry out instructions.
In modern processors; architectures, there are places where data passes through in raw, unencrypted form, such as inside the kernel or in system memory that is carefully set aside from other applications. This data has powerful protections to prevent it from being interfered with or even observed by other processes and applications.
However, Meltdown and Spectre can circumvent those protections, exposing nearly any data the computer processes.
Meltdown and Spectre work differently. One can break through the barrier that prevents applications from accessing arbitrary locations in kernel memory, and the other affects pretty much anything with a chip in it.
Because of this reason, Meltdown and Spectre that are flaws at the architecture level, can affect any computer or device running Windows, OS X, Android, or something else. All software platforms are equally vulnerable. They can also be inside the clouds.
The flaws were initially discovered in the middle of 2017, but haven't been made public. But where the flaws happened to be reported, this caused Intel and others, including security researchers to publish their findings sooner than planned, even before the fixes are made available.
