When a dangerous flaw happened to be found, people should scramble for a fix, even if that fix is only worthwhile.
The same goes following the announcement of speculative execution exploits called the Microarchitectural Data Sampling (MDS) that apply to desktop and notebook computers with Intel CPUs, including all modern Mac computers.
Knowing that its devices are at risk, Apple posted a document on its website to explain how customers with computers that are "at heightened risk" of attack can enable full mitigation.
This full mitigation is not enabled by default for a good reason: it has a severe performance penalty.
In its own tests, Apple recorded up to 40 percent performance drop with full mitigation is activated. This happens because enabling MDS protection involves Apple in disabling the hyper-threading functionality.
This essentially makes a computer a 'dumber' when its processor switches context.
This is why full mitigation mode may be of interest to ordinary customers who just don't work/have anything particularly sensitive on their computer, as the performance drop isn't just worth their effort.
But for those who are particularly at risk, like members of government or high-ranking business executives, this full mitigation should give them at least a bit of relief.
But either way, most users may not need to worry about enabling full mitigation. This is because since mac OS 10.14.5, Apple has included some relevant patches, including one that prevents JavaScript exploit through Safari web browser. Apple has rolled these critical fixes to all customers as the performance penalty was small (around 3 percent).
To activate full mitigation, Apple users using macOS Mojave, High Sierra, and Sierra after installing security updates, can follow these steps:
- Restart the Mac computer and hold the Command key and the R key to enter macOS Recovery mode.
- Open the Terminal from the Utilities menu.
- Enter the command
nvram boot-args="cwae=2"and press Return. - Enter the command
nvram SMTDisable=%01and press Return. - Restart the Mac.
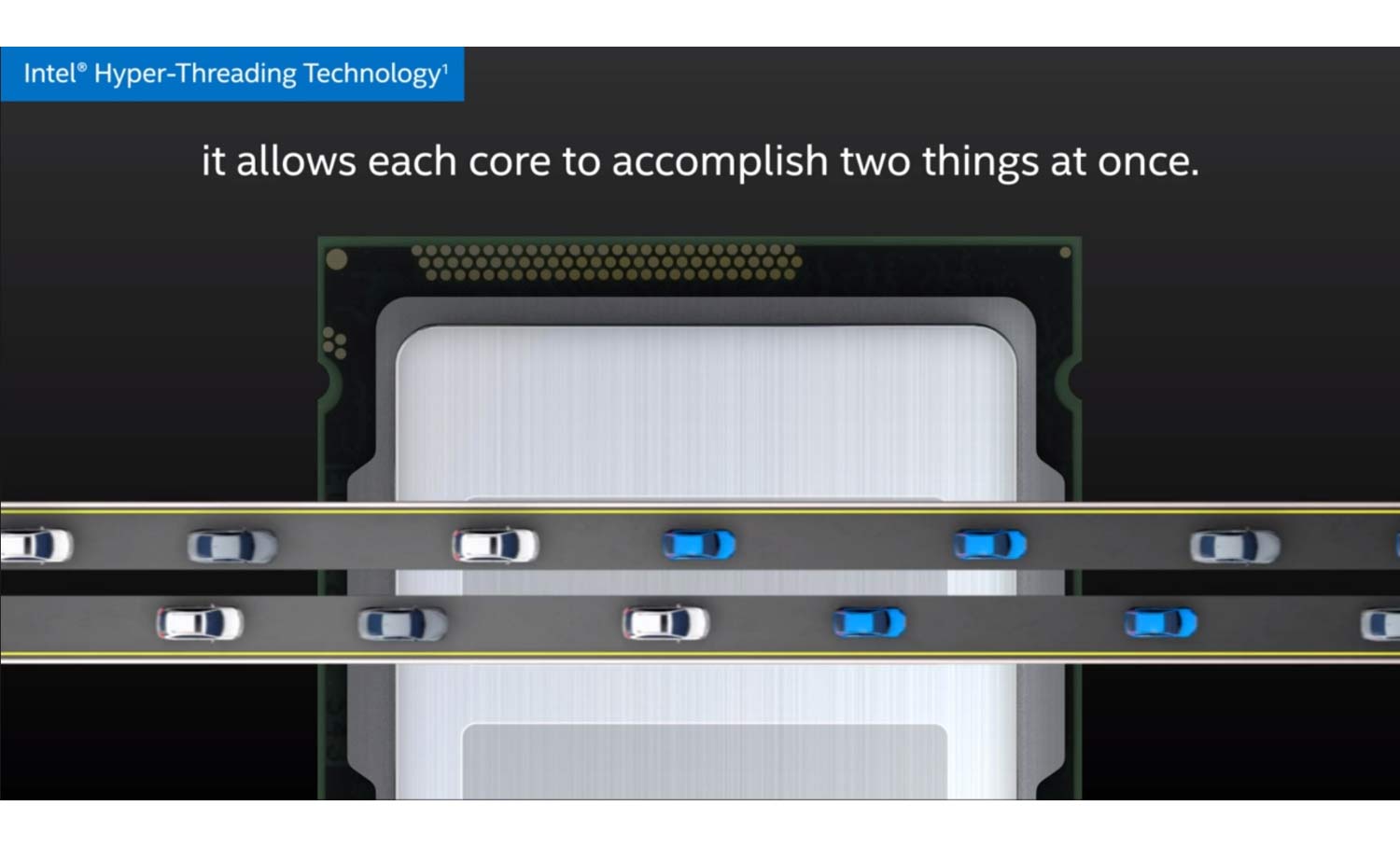
To revert the mitigation and re-enable hyper-threading processor technology, users can reset the NVRAM and restart their Mac. To do this, users are required to:
- Shut down the Mac computer, then turn it on again.
- Immediately press and hold these four keys together: Option, Command, P, and R. Users can release the keys after about 20 seconds, during which the Mac might appear to restart.
- If the Mac uses firmware password, users need to first turn off the firmware password to reset the NVRAM.
And if users have previously set custom boot-args, they have to again add those boot-args to the NVRAM command.
To check whether the hyper-threading is enabled or disabled, users can go to the System Information app, by choosing the Apple menu > About This Mac, to then click the System Report button, and select Hardware in the sidebar.
If the processor in the Mac supports hyper-threading, the 'Hyper-Threading Technology' is shown as either Enabled or Disabled.
It should also be noted that full mitigation is not enabled while using Boot Camp to run Windows on a Mac. What's more, these speculative execution exploits specifically affecting Intel CPU architecture, meaning that the flaws won't affect iPhones and iPads that use ARM chips.
