
It was first discovered that an Internet Explorer (IE) zero-day vulnerability could enable hackers to steal limited data from users using computers running Windows 7, 10 and Server 2012.
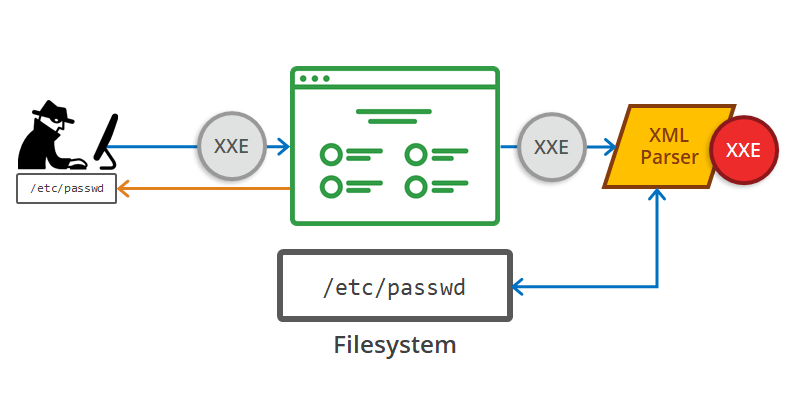
The flaw comes from IE's XML eXternal Entity vulnerability (sometimes called an XXE injection attack), discovered by security researcher John Page.
The research concluded that the Microsoft web browser's vulnerability could also be "exploited even if you never intentionally use Internet Explorer."
But things can go more than that, as the flaw enables hackers to infiltrate computers in such a way that they are only required to do a couple of clicks to execute their attacks on victims.
In Page’s demonstration, he opened a malicious MHL file with a file manager. IE then automatically uploaded several files to a remote server. Page then showed that when the downloaded file is opened through IE, the information was not sent to the remote server.
However, when Page downloaded the file through Microsoft Edge and opened it through IE, the exploit worked as it was intended.
This vulnerability was also tested and verified by Mitja Kolsek the CEO of ACROS Security.
The flaw happened to resides inside Windows 10 feature which is meant to boost security of such saved file against malicious code being able to execute within the Edge sandbox.
This feature however, appears to effectively disable another security feature, known as 'mark-of-the-Web', which is used by IE to flag untrusted files downloaded from the internet.
Here, IE creates a single MIME HTML (MHT) file to save a complete web page to a local drive, one that contains all images, CSS, JavaScript and internal links. The problem is, IE added the “mark-of-the-Web”, but Microsoft Edge did not.
"We have found that the malicious MHT file doesn't have to be downloaded and manually opened by the user, just opening it directly from Edge can be made to work as well," Kolsek explained.
What's more, Kolsek said that the exploit can also be enhanced to make it operate with more stealth and "extract many local files using a single MHT file."
Kolsek also disclosed that the original proof-of-concept exploit could be "improved" to steal far more files and with the malicious file being opened directly from Edge.
Here, Kolsek revealed that Windows 10 users are at far more risk if they use Microsoft Edge web browser.
The reason for this is because IE appears to be confused by Edge’s added entries. IE was unable to read the malicious MHT’s data stream, therefore assuming that it did not include a mark-of-the-web.
Kolsek noted that “An undocumented security feature used by Edge neutralized an existing, undoubtedly much more important feature (mark-of-the-web) in Internet Explorer.”
According to James Forshaw of Google’s Project Zero vulnerability team, Edge instead “capability and group SIDs for the Microsoft.MicrosoftEdge_8wekyb3d8bbwe package." Once Forshaw deleted one of Edge’s added entries, the vulnerability disappeared.
Page and other researchers contacted Microsoft, but the company replied that it does not intend to fix the bug any time soon.
Spoiler, the secret is the capability and group SIDs for the "Microsoft.MicrosoftEdge_8wekyb3d8bbwe" package :-) This seems par for the course with Edge, adding backdoors all over the place. Wonder if this approach will apply to Edgium? /cc @ericlaw https://t.co/lu78M7N0qO
— James Forshaw (@tiraniddo) April 17, 2019
The company said that:
"The technique described relies on social engineering and requires a user to download and open a malicious MHT file. We encourage customers to practice safe computing habits online, including exercising caution when clicking on links, opening unknown files, or accepting file transfers."
While it was initially believed that the vulnerability affected the latest version of Internet Explorer on Windows 7, Windows 10, and Windows Server 2012 operating systems, it appears that it is only a threat to Windows 10 users.
It's encouraged that users always practice caution when downloading and opening files.
Kolsek said that only Edge users are at risk, so not using the Microsoft browser should be the best solution, especially since Microsoft declined to quickly fix the issue.
"No other leading web browsers and email clients we've tested are using the undocumented security flag on the downloaded files, which effectively blocks the exploit," according to Kolsek, who seems sure that Microsoft will revisit the issue and develop a patch.
