Apple's App Store is seen to have better security than Google Play Store. But there are still chances that things can get through the cracks.
In a report, security researchers from Wandera discovered 14 games that all communicated with the command-and-control servers known to have been used by the Golduck malware for Android.
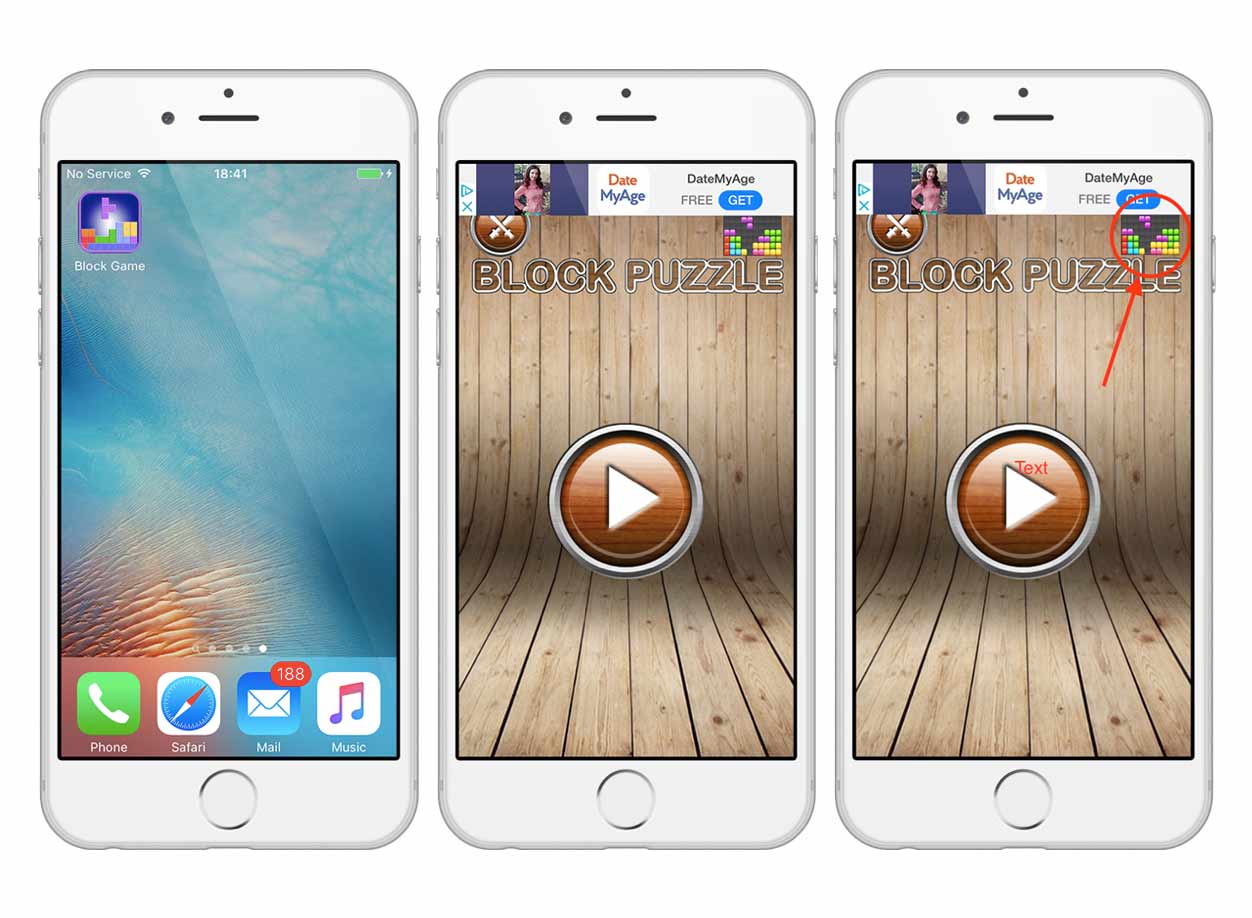
While the apps themselves appeared harmless, they all have ads which can be used to trick users into granting permission for malware installed outside of the App Store.
First discovered by Appthority, the loader was found in multiple apps distributed through the Google Play store at the end of 2017. It was used by its developers as an adware distribution platform, where it can be made to display ads that aren't powered by AdMob but instead from the malicious server.
The iOS apps found by Wandera to have this malware, have aggressive ads which are pushed through a small ad boxes that are easy to click by mistake.
With the malware, it is possible for the developers to compromise users' device, in which they can build botnet networks for later usage. It can be also used to create custom multi-stage infection chains as the loader can drop second-stage payloads.
Although this type of loader only acts as a dropper for other malware strains and doesn't come with their own data stealing or data corruption features, it can still be used to create backdoors.
The 14 risky apps include:
- Commando Metal: Classic Contra.
- Super Pentron Adventure: Super Hard.
- Classic Tank vs Super Bomber.
- Super Adventure of Maritron.
- Roy Adventure Troll Game.
- Trap Dungeons: Super Adventure.
- Bounce Classic Legend.
- Block Game.
- Classic Bomber: Super Legend.
- Brain It On: Stickman Physics.
- Bomber Game: Classic Bomberman.
- Classic Brick – Retro Block.
- The Climber Brick.
- Chicken Shoot Galaxy Invaders.
And since the loader on the above 14 apps can also connects itself to its command-and-control server, the developers can use it to collect user information, such as device type, app version, IP address of the device, and in some cases, even location data.
These potentially sensitive data can then be sold to other bad actors as part of Malware-as-a-service (MaaS) schemes.
"The [Golduck] domain was on a watchlist we established due to its use in distributing a specific strain of Android malware in the past," said Michael Covington, Wandera’s VP of product. "When we started seeing communication between iOS devices and the known malware domain, we investigated further."
Apple has always been especially proud of its App Store app review process, as it is more strict and thorough than Google's. But still, the popularity and the number of apps it has to police somehow opens some holes to be exploited.
The 14 apps has made their way to the App Store, in which according to Sensor Tower, they have been downloaded by nearly 1 million users.
That number is huge and should pose potential infections, even if only a fraction of that group taps on the links to the actual malware.
It's relatively easy for Apple to address this kind of incident, as it can simply remove those apps from its App Store. But as of the discovery, Apple has not issued any official statement nor a warning to users, as this could constitute negative publicity for its claims on the App Store’s "ultimate security".
This is again another warning for users to only download apps they know they can trust, and to never jailbreak their iPhones no matter how tempting it is.
No app store is perfect, and users should not trust everything on the App Store.
Wandera pointed out that users should do some researches before downloading apps they want, such as looking for the available developer information, the official websites and some others to critically judge the apps' advertising practices.
