ClusterFuzz from Google has long been used internally by Google for "fuzzing" and automatically detecting bugs on its products.
Fuzzing is an automated method for detecting bugs in software that works by feeding a lot of unexpected inputs to a program to see how it reacts.
According to Google, the method is effective at finding memory corruption bugs, which often have serious security implications.
Developers attempting to find this kind of issues can be both time consuming and difficult. With the many lines of codes a product has, some bugs can slip through despite vigorous attempts by developers in finding them.
"For software projects written in an unsafe language such as C or C++, fuzzing is a crucial part of ensuring their security and stability," said Google.
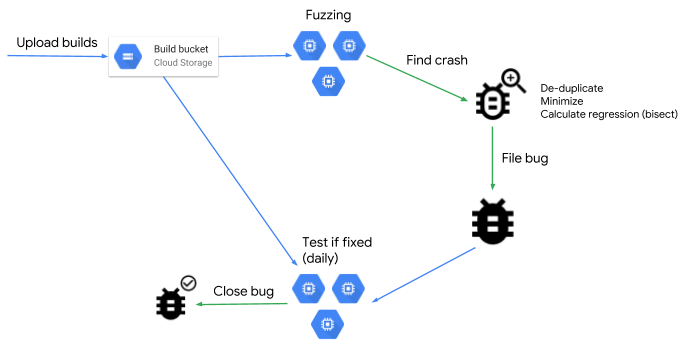
With ClusterFuzz, developers can automate the complex process of finding bugs and security flaws, down to the reporting and retesting fixes.
The tool itself also uses open-source libraries like libFuzzer fuzzing engine and AFL fuzzer to power some of the core fuzzing features that generate the test cases for the tool.
According to Google:
ClusterFuzz for Google, has been an integral part of the development process of Chrome and many other open source projects, as it can detect bugs hours after they are introduced and verify the fix within a day.
Having used the tool internally, Google said that the fuzzing tool has helped it find more than 16,000 bugs in Chrome, and more than 11,000 bugs in more than 160 open source projects integrated with OSS-Fuzz.
And here, Google has made ClusterFuzz an open source project, and available for anyone to use.
ClusterFuzz has the following feature:
- Highly scalable. Google’s internal instance runs on over 25,000 machines.
- Accurate deduplication of crashes.
- Fully automatic bug filing and closing for issue trackers.
- Testcase minimization.
- Regression finding through bisection.
- Statistics for analyzing fuzzer performance, and crash rates.
- Easy to use web interface for management and viewing crashes.
- Support for coverage guided fuzzing (e.g. libFuzzer and AFL) and blackbox fuzzing.
ClusterFuzz depends on some key Google Cloud Platform services, but developers can still use the tool on their own compute cluster.
"We welcome your contributions and look forward to any suggestions to help improve and extend this infrastructure," said Google.
"Through open sourcing ClusterFuzz, we hope to encourage all software developers to integrate fuzzing into their workflows."
