Chrome is Google's web browser, and it's the most popular. This fact makes it a prime target by malicious actors who wish to spy on internet users.
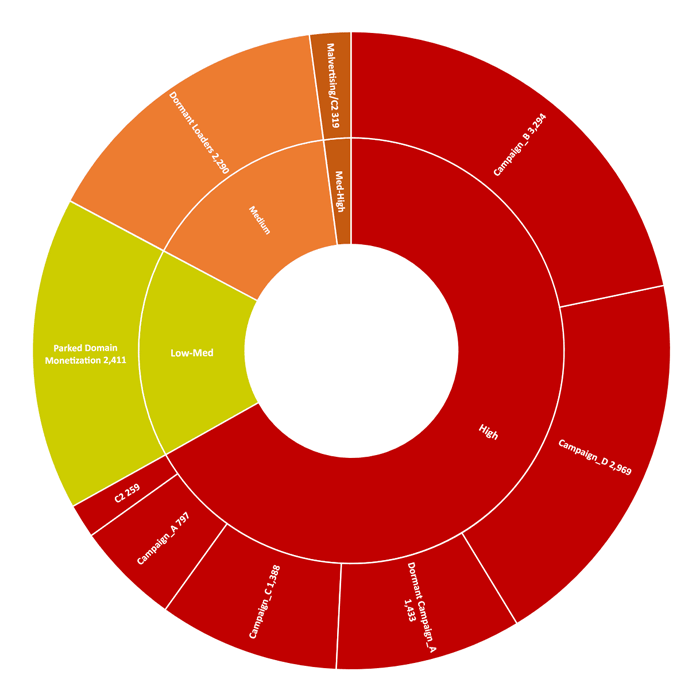
As reported by researchers at Awake Security, 111 malicious or fake Chrome extensions were found on Chrome Web Store in the past three months alone.
In total, the malicious Chrome extensions have been downloaded by nearly 33 million times.
Gary Golomb, co-founder and chief scientist at Awake Security, said that the malicious extensions were meant to warn users about questionable websites, or to convert files from one format to another.
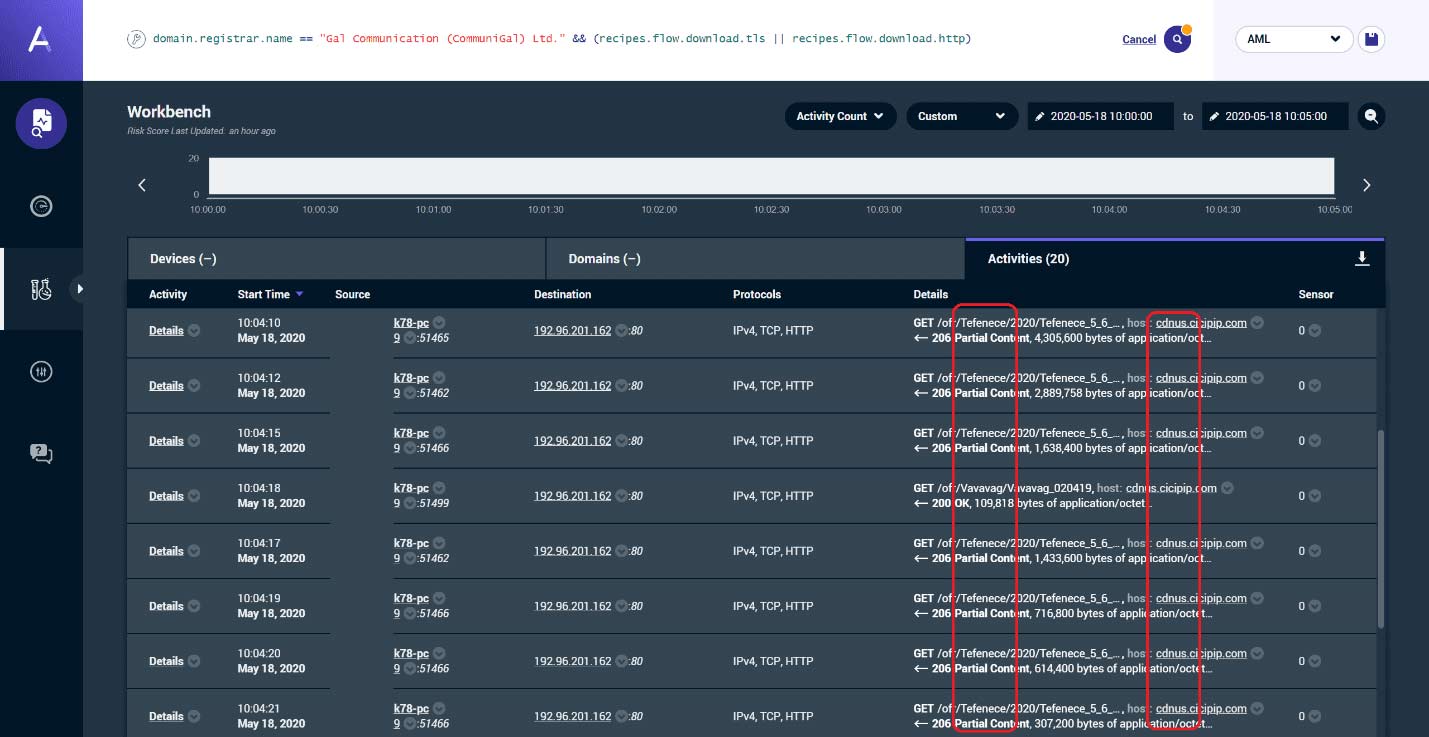
But instead of doing what they're advertised to do, they siphoned off browsing history and data that provided credentials for access to internal business tools, take screenshots, read the clipboard, harvest credential tokens stored in cookies and grab users keystrokes, including passwords.
Golomb said that the attackers hid behind thousands of malicious domains housed at GalComm (CommuniGal Communication Ltd), a registrar based in Israel. Out of the 26,079 reachable domains registered through GalComm, 15,160 domains (nearly 60%) were linked with each other, and were either malicious or suspicious.
At the time of finding, Golomb could not report any specific financial damages caused by the malicious extensions. However, he did say that the malicious extensions do expose an “unintended consequence” of cloud computing.
According to Golomb, the malicious actors managed to bypass the cloud-based reputation services or virus scans used by most researchers and enterprise security teams, so the extensions could get through.
"The attackers took away the ability of security teams to make a case. They also showed that in bypassing all the cloud-based tools used by security researchers, they could circumvent normal detection. What’s to stop a group from setting up their own registry and launching yet another campaign?"
For its part, GalComm publicly denied any wrongdoing.
"Galcomm is not involved, and not in complicity with any malicious activity whatsoever," said the registrar owner Moshe Fogel. "You can say exactly the opposite, we cooperate with law enforcement and security bodies to prevent as much as we can."
But Golomb was skeptical because he didn’t think anything this kind of campaign could be done without the registrar’s knowledge. Golomb said that in the worse case scenario, GalComm was involved, but there is also a chance that GalComm could have just “looked the other way.”
ICANN, the major international domain registry organization which oversees registrars, said that it had received few complaints about Galcomm over the years, and none about malware.
And according to Golomb, ICANN does “very little” to police these kinds of activities.
In a statement, Google spokesman Scott Westover said that:
"All extensions go through an automated review process, and the majority also undergo manual reviews by our team. We use a combination of automated and manual review, based on a variety of signals for a particular extension."
"The Chrome Web Store uses a number of methods to detect policy violations and enforce against them, including manual and automated reviews both proactively and responsively. Enforcement action can include removal from the Chrome Web Store or developer account termination. In addition to disabling the accounts of developers that violate our policies, we also flag certain malicious patterns we detect in order to prevent extensions from returning. Additionally, we’ve announced technical changes that will further strengthen the privacy of Chrome extensions and new policies that improve user privacy."
Based on the number of downloads, this case is considered the most far-reaching malicious Chrome store campaign to date.
Alphabet Inc's Google said that it has removed the malicious extension from its official Chrome Web Store, shortly after being alerted by the researchers in May.
While Google has taken steps to prevent the malicious extensions from doing any more harm to new users, the tech giant declined to discuss how this case is compared to prior campaigns, the breadth of the damage, or why Google did not detect and remove the bad extensions on its own despite past promises to improve security.
It is also unclear who was behind the malicious extensions, because the developers simply supplied fake contact information when they submitted the extensions to Google.
While much of the news were focused on the malicious Chrome extensions, security experts were more confused over how the attackers managed to bypass cloud-based security tools.
These cloud-based tools have been the things many researchers and analyst rely on for years. And attackers capable of circumventing the security measure could translate to catastrophe in the foreseeable future.
