PDF stands for 'Portable Document Format', which can be traced back to the 1990s by Adobe, as a way to share computer documents, text formatting and inline images.
Fast forward, the format has become the de facto document technology, as it has advantages of being independent from application software, hardware, and operating systems.
And here, researchers have discovered a flaw in the technology, that allows attackers to extract sensitive contents from a password-protected or encrypted PDF file.
The bug is called 'PDFex'' which exploits security weaknesses in the standard encryption protection built into PDF.
In a paper titled “Practical Decryption exFiltration: Breaking PDF Encryption”, German academics from Ruhr-University Bochum and Münster University of Applied Sciences disclosed two different variations of the attack.
As a result, 27/27 PDF viewers were vulnerable (14 without user interaction, 13 with user interaction). #PDFex 7/n pic.twitter.com/520wQ4bRt5
— Sebastian Schinzel (@seecurity) September 30, 2019
The bug doesn't need hackers to crack the password-protected and encrypted PDF.
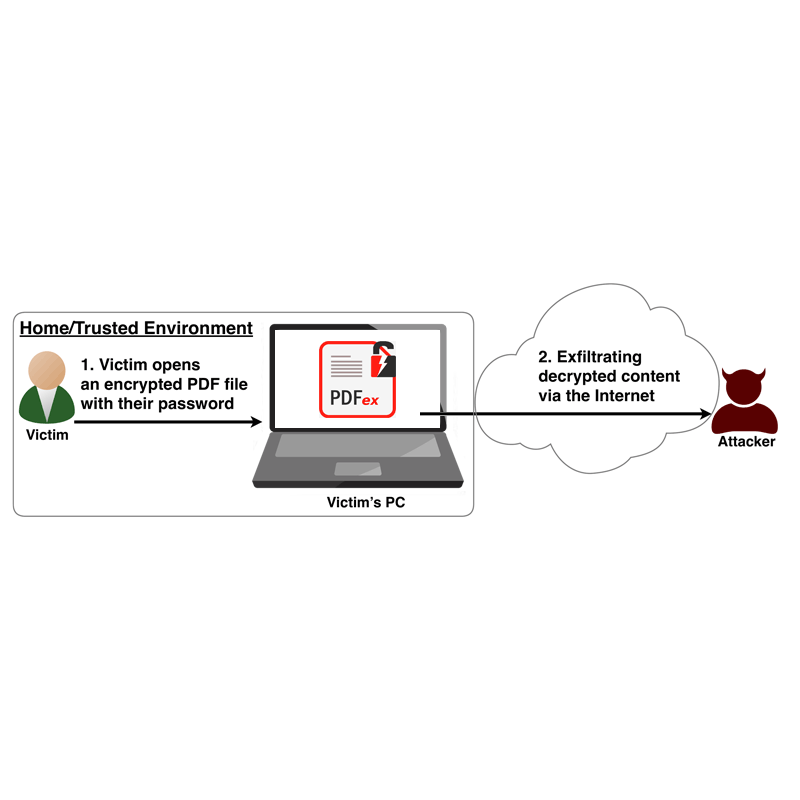
Instead, in the first method, the researchers said that hackers can leverage a method which takes advantage of the partial encryption supported natively by the PDF specification, to remotely exfiltrate content once a user opens that document.
The method is called 'Direct Exfiltration'
Another way of explaining it: hackers can modify a password-protected PDF file in such a way that when it’s opened with the right password, a copy of the decrypted content is automatically transmitted to a remote server controlled by the attacker via a PDF form, URL, or JavaScript code.
This can be achieved by tampering the unencrypted plaintext data through PDF forms. It doesn’t even require any sort of user interaction.
According to the researchers in a blog post:

The second variation of the attack is similar.
But unlike the first, the flaw only exploits the encrypted bits of the PDF file. Leveraging this flaw, hackers can make use of Cipher Block Chaining (CBC) mode of encrypting blocks of plaintext to transform a piece of ciphertext into another ciphertext, a property in cryptography called malleability.
The CBC mode employs a chaining mechanism to encrypt data, which means that encryption of each plaintext block depends on the immediately preceding ciphertext block.
In other words, it is necessary for the hackers to know the “plaintext segment” in order to directly manipulate an encrypted object, the researchers noted. This is fortunate.
The researchers call the second method the 'CBC Gadgets' attack.
The academics have disclosed their findings to all affected vendors, and also released proof-of-concept exploits for PDFex attacks to the public, by disclosing the technical details of the attacks to the PDF Insecurity website.
To mitigate the attack, the researchers suggest vendors to drop support for partially encrypted PDF files, or to enforce a policy where unencrypted objects should not be allowed to access encrypted content.
"Many data formats allow to encrypt only parts of the content (e.g., XML, S/MIME, PDF),” the researchers said. “This encryption flexibility is difficult to handle and allows an attacker to include their own content, which can lead to exfiltration channels."
“In the long term, the PDF 2.x specification should drop support for mixed content altogether."
