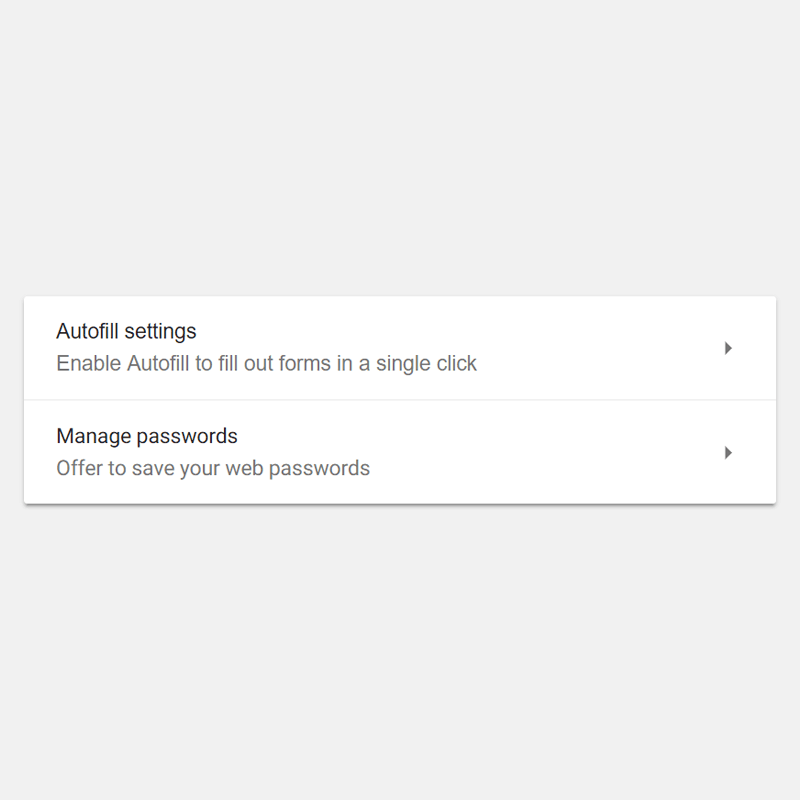
All major web browsers have built-in login managers that automatically fill in username and password to make login experience more seamless.
But those lightweight password managers have a long-known vulnerability.
According to research from Princeton's Center for Information Technology Policy, those tools can be exploited, in which can be abused by third-party scripts for tracking users from site to site.
The researchers examined two different scripts (AdThink and OnAudience) that are designed to get identifiable information out of browser-based password managers. The two use scripts that inject invisible login forms in the background of the webpage which gather whatever information the browsers' autofill feature shows.
The gathered information are then hashed and sent to third-party servers, where persistent IDs can be created to track users from page to page, creating the potential means for target users with advertising.
While the scripts focus on usernames, according to the researchers, there is no technical measure to stop those scripts from running and collecting passwords. The only robust way, is to change how the password managers work, like for example: requiring more approval permissions before submitting information.
:It won't be easy to fix, but it's worth doing," said Arvind Narayanan, a Princeton computer science professor who worked on the project.

"The hash of an email address can be used to connect the pieces of an online profile scattered across different browsers, devices, and mobile apps. It can also serve as a link between browsing history profiles before and after cookie clears."
For Narayanan, it's not the scripts that worried him the most. He put the most blame to websites who choose to run those kind of scripts, often without realizing how invasive they can be to users.
And what make things worse is that the scripts were present on 1110 of the Alexa top 1 million sites.
"We'd like to see publishers exercise better control over third parties on their sites," said Narayanan. "These problems arise partly because website operators have been lax in allowing third-party scripts on their sites without understanding the implications."
While much of the past discussion has focused on password exfiltration by malicious scripts through cross-site scripting (XSS). fortunately, the researchers have yet to find any password theft on the 50,000 sites they have analyzed. But instead, they found those tracking scripts that extract user credentials for building tracking identifiers.
