IKEA is a Swedish-origin Dutch-headquartered multinational conglomerate that designs and sells ready-to-assemble furniture, kitchen appliances and home accessories, among other goods and home services.
While most transactions occur throughout its stores, which can be found in multiple places around the world, one of its main sources of communication methods is via email.
And this time, the company that was founded in 1943, is struggling to contain a massive reply-chain email attack that target its employees through phishing campaigns.
Reply-chain email attacks occur when a threat actor takes over a legitimate email account and sends an email impersonating that person in an email thread.
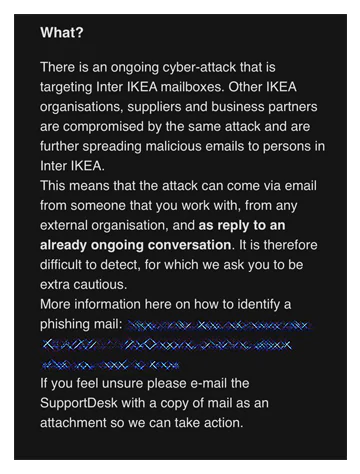
In this case, employees of IKEA receive emails from internal mailboxes, as well as from "other compromised IKEA organizations and business partners."
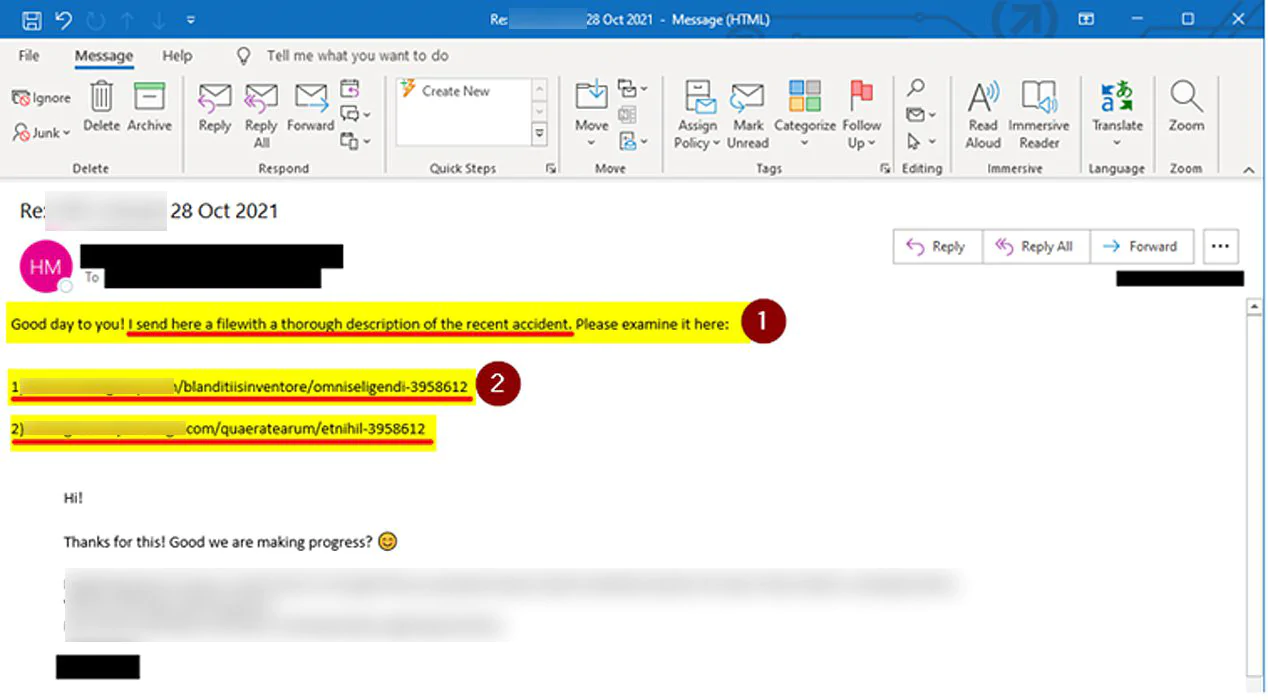
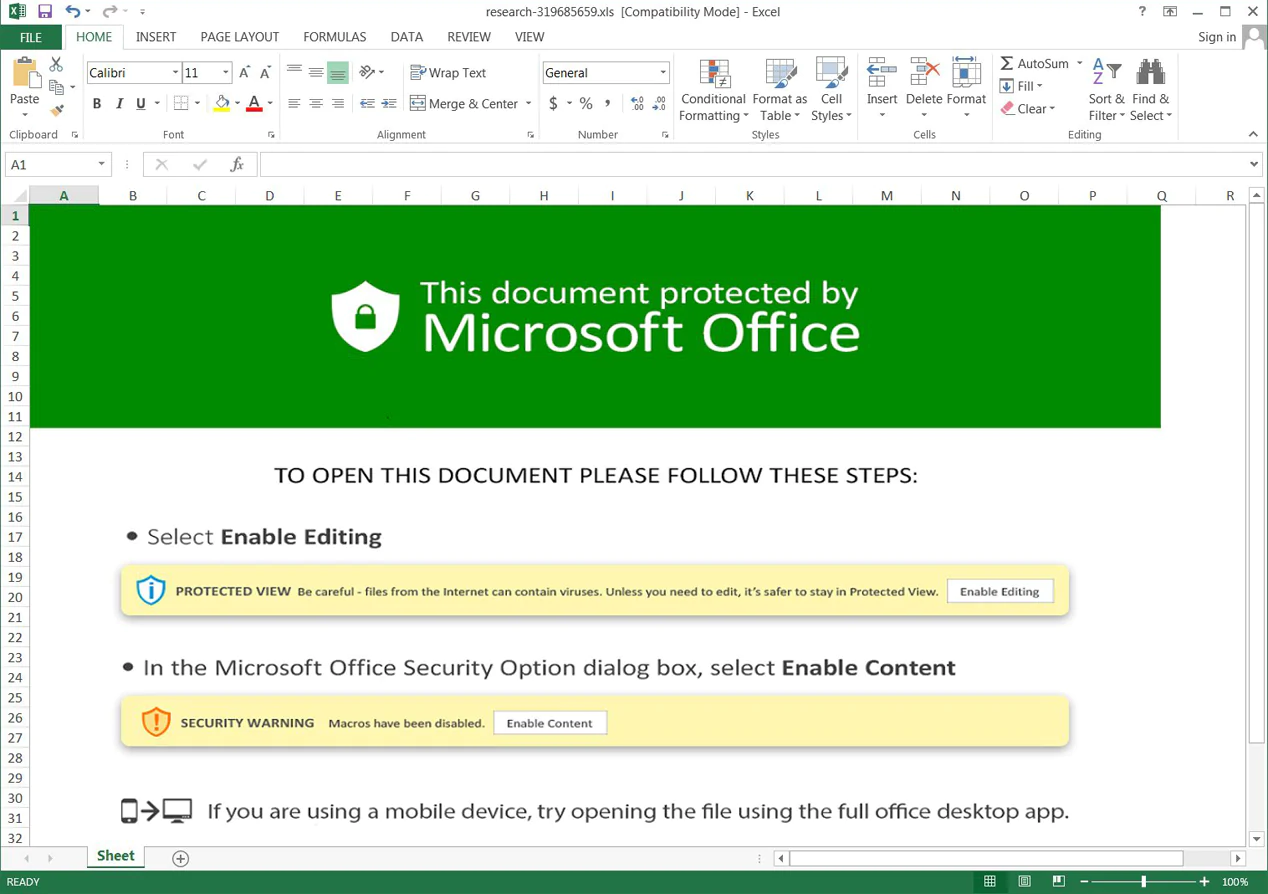
The carefully-crafted emails contain files or links to files that have malware embedded in them.
The attackers try to lure and trick IKEA's employees to execute the files within the emails, or follow the links so the attackers can continue and have access to IKEA's internal digital infrastructure.
It is said that the attackers managed to launch the phishing attacks by utilizing the ProxyShell and ProxyLogin vulnerabilities to access internal Microsoft Exchange servers.
The cybercriminals use ProxyShell to act as an absolute administrator account, in which they have access to remote code execution, giving them the ability to run any commands and choose any programs.
After that, the cyberattackers use ProxyLogin to remotely execute code on the target server from anywhere in the globe with an internet connection.
After acquiring access to a server, they utilize internal Microsoft Exchange servers to launch reply-chain attacks against IKEA employees using stolen company emails.
IKEA's IT team that was dispatched, realized that all the malicious emails within the cyberattack have one thing in common: the links inside the emails contain seven-digit numbers at the end.
But still, the IT team asked employees to refrain from opening any emails, even when they came from their close friends at work or their bosses.
In order to stop the threat, employees have to report all of the emails that they are receiving from their internal emails to the IT team.
But unfortunately for IKEA, the phishing campaign is not only targeting the Swedish company's workforce.
The Swedish firm disclosed that "other IKEA organizations, suppliers, and business partners are compromised by the same attack."
The IT team realized this when they found that other IKEA-related organizations, as well as their partners in business, have also received malicious emails in their inboxes.
In an email sent to IKEA employees regarding the matter, as seen by BleepingComputer:
"This means that the attack can come via email from someone that you work with, from any external organisation, and as a reply to an already ongoing conversations. It is therefore difficult to detect, for which we ask you to be extra cautious."
The IT team at IKEA said that the company's existing email spamming filters could help stop some of the malicious emails and quarantine them to prevent further spreading.
But as a precaution, the team has also disabled the ability for some of its employees from replying to emails.
However, the cyberattackers know this too well.
In order to pass the spam filters, the emails were also sent using internal emails within IKEA itself.
Because emails sent internally have a higher chance of passing the filtering process, the attackers may have delivered their payloads already.
What's more, since the campaign uses Microsoft Exchange servers as its entry point, IKEA is considering this security issue as a severe cyberattack,
This is why the company's IT team is said to be on high alert.
