
A security researcher from Google has discovered a severe vulnerability in Blizzard games that could allow hackers to run malicious code on the gamers’ computers.
The games include World of Warcraft, Overwatch, Diablo III, Hearthstone and Starcraft II. The popular online games created by Blizzard Entertainment are played by more than half a billion users around the world.
The flaw happens to be on the game client application, called 'Blizzard Update Agent''.
To play Blizzard's games online using web browsers, users need to install the game client application into their systems that run JSON-RPC server over HTTP protocol on port 1120, and "accepts commands to install, uninstall, change settings, update and other maintenance related options."
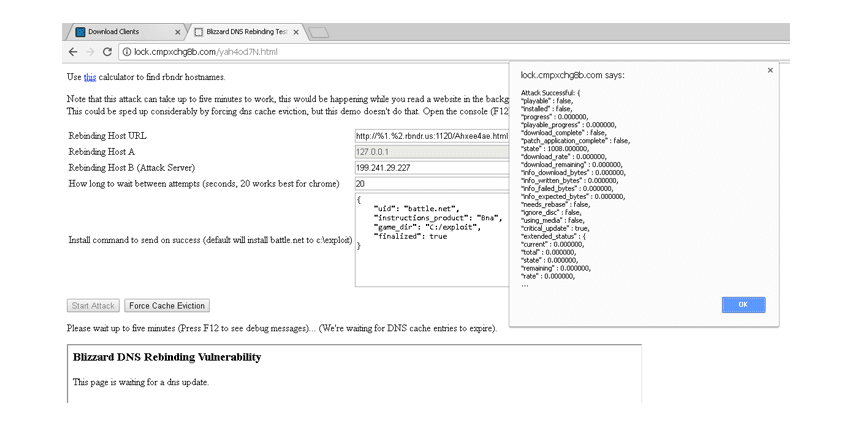
Here, Google's Project Zero team researcher Tavis Ormandy discovered that the Blizzard Update Agent is vulnerable to DNS Rebinding, which is a hacking technique that allows any website to act as a bridge between the external server and the gamers' localhost.
All Blizzard games (World of Warcraft, Overwatch, Diablo III, Starcraft II, etc.) were vulnerable to DNS rebinding vulnerability allowing any website to run arbitrary code. https://t.co/ssKyxfkuZo
— Tavis Ormandy (@taviso) January 22, 2018
Normally, a random website running in a web browser cannot make requests to a hostname other than its own, but the local Blizzard updater service does not validate what hostname the client was requesting, making it respond to such those requests.
Before Blizzard responded with a patch, all Blizzard games were vulnerable to this kind of attack.
Ormandy has published a proof-of-concept exploit that executes the DNS rebinding attack against Blizzard clients and could be modified to allow exploitation using network drives, or setting destination to "downloads" and making the browser install malicious things.
He reported the issue to Blizzard to get it patched before hackers could take advantage of it.
"Blizzard was replying to emails but stopped communicating on December 22nd. Blizzard is no longer replying to any enquiries, and it looks like in version 5996 the Agent now has been silently patched with a bizarre solution," said Ormandy.
"Their solution appears to be to query the client command line, get the 32-bit FNV-1a string hash of the exename and then check if it's in a blacklist. I proposed they whitelist Hostnames, but apparently, that solution was too elegant and simple. I'm not pleased that Blizzard pushed this patch without notifying me, or consulted me on this."
But after Ormandy's report went public, Blizzard contacted and informed him that a more robust Host header whitelist fix is being developed to address the issue.
Previously, Ormandy has also revealed a similar vulnerability in the Transmission BitTorrent app that could allow hackers to remotely execute malicious code on BitTorrent users' computers and take control of them. He is also actively checking other video game developer with a user base of over 100 million to see if the problem can be replicated.
