In the modern days of tech, drones are like the marvel of civil aviation. They took hobbies and tech together, and even created jobs and sports out of it.
When it comes to privacy and security however, drones are already a concern. Drones themselves can be equipped with a variety of sensors, including a camera and microphone. That alone is seen as invasive, especially when drones are flying in privately properties.
And not just that, as the app is also flawed.
The Android version of DJI Go 4, an app that allows users to control drones made by China-based DJI, the world's biggest maker of commercial drones, allows users to control and collect near real-time data, including video footage and flight information. The app was found to also secretly collecting sensitive user data.
What's more, the app can also execute code the developers want.
The concern was highlighted by two separate reports that question the security and trustworthiness of the three-and-a-half stars out of a possible total of five app with more than 1 million Google Play downloads.
It started when researchers from security firm Synactive reverse-engineered the app.
On their report, they said that there are security concerns on the DJI GO 4 app, especially given the lack of transparency around the app's capabilities.
Then, a security researcher from Grimm published their own report, based on Synactive findings. Here, the researcher found that the app has secretly collected a wide array of sensitive user data and sent it to servers located in mainland China.
A worst-case scenario is that the developers of the app can abuse the data to spy on users.
According to the reports, the suspicious behaviors include:
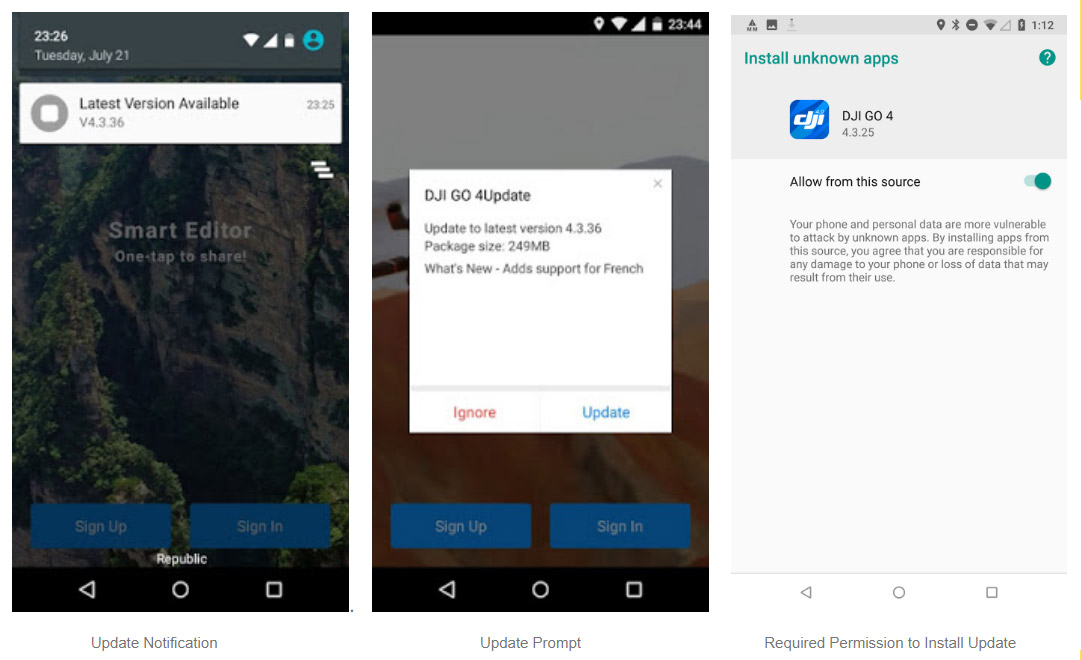
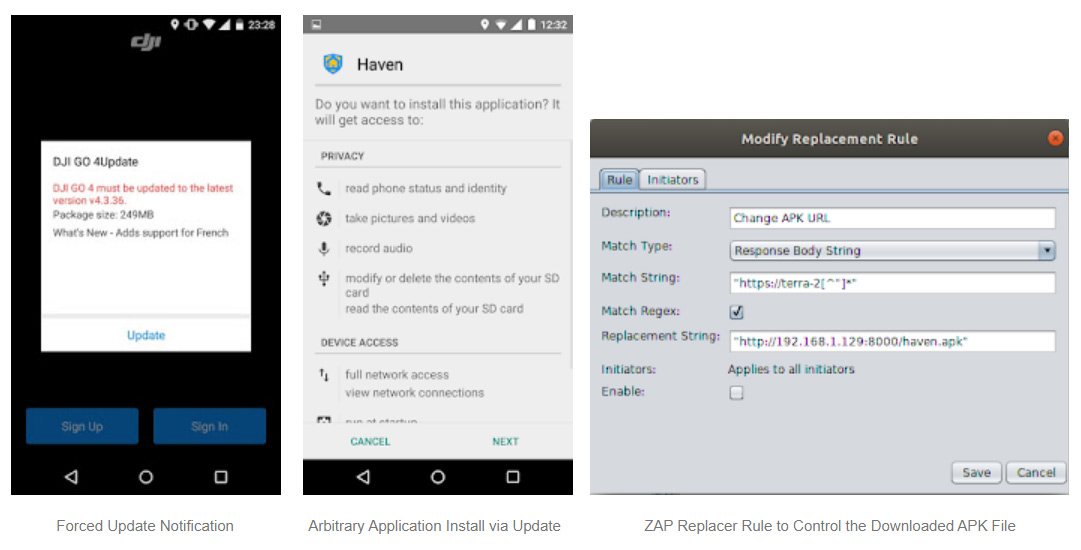
- The ability to download and install any app the developers wants through either the app's self-update feature or through a dedicated installer provided by China-based social media platform Weibo.
- Once having a component capable of collecting phone data that include IMEI, IMSI, carrier name, SIM serial Number, SD card information, OS language, kernel version, screen size and brightness, wireless network name, address and MAC, and Bluetooth addresses.
- An automatic restart in the background feature when users swiped the app tp close it.
- Advanced obfuscation techniques to make it difficult for third-party to analyze the app.
In its defense, DJI wrote an extensive explanation on its website, saying that the researchers found “hypothetical vulnerabilities” and that neither report provided any evidence that they were ever exploited.
They said that all the features and components detailed in the reports were either meant to serve legitimate purposes or were unilaterally removed and weren’t used maliciously.
“We design our systems so DJI customers have full control over how or whether to share their photos, videos and flight logs, and we support the creation of industry standards for drone data security that will provide protection and confidence for all drone users,” the company said in a statement.
Whatever the truth is, the two researches and the DJI's response again highlight the problems inside Google's ecosystem that isn't capable of effectively vetting apps.
While newer Android versions are definitely getting better in preserving users' privacy, older versions of Android lack the permission granularity. What's more, the openness of Android makes it easy for bad actors to publish malicious apps to Google's Play Store.
Android's weaknesses also make it easy for security features to mistake legitimate functions for malicious ones.
This report by the researchers came about three years after the U.S. Army started banning the use of DJI drones for reasons that remain classified. In January 2020, the Interior Department started forbidding drones from DJI and other Chinese companies fearing that they can send data back to China.
