
A powerful new hacking tool has reportedly been unleashed, putting potentially hundreds of millions of iPhones at risk.
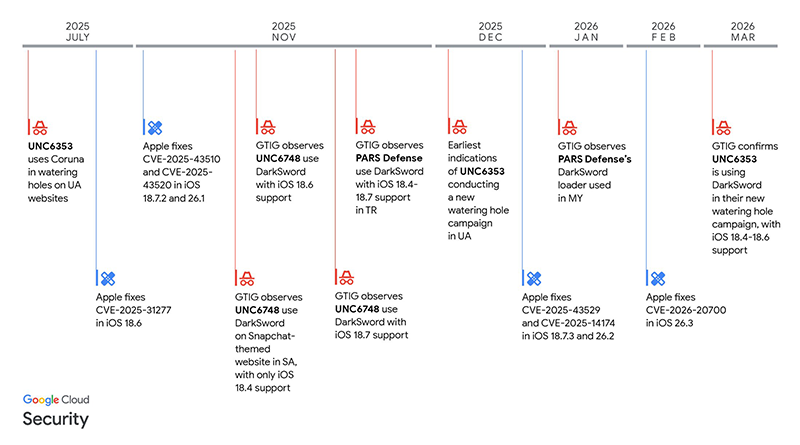
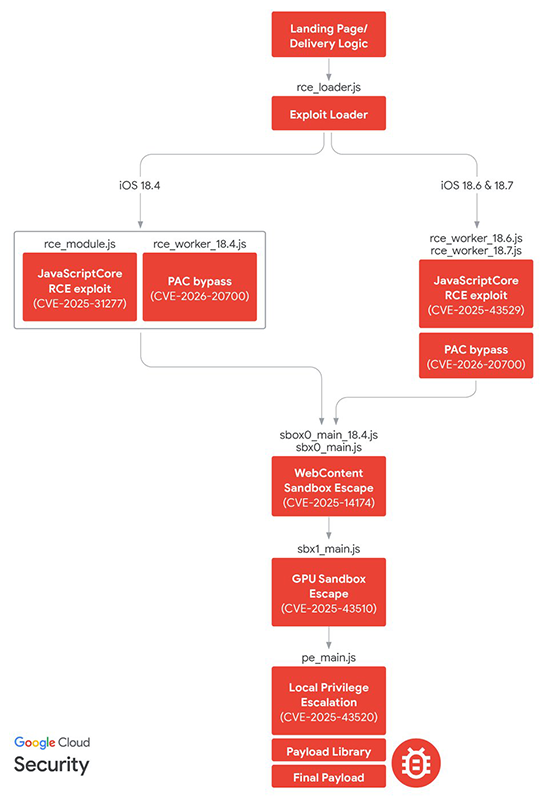
Dubbed 'DarkSword,' the tool has quickly emerged as a major global threat after researchers discovered it can silently compromise devices through something as simple as visiting a malicious website. Identified in March 2026 by cybersecurity firm iVerify, mobile security company Lookout, and Google's Threat Intelligence Group (GTIG), DarkSword is an advanced exploit kit that chains together six vulnerabilities, including several zero-days, to achieve a full device takeover.
Alarmingly, it requires no user interaction beyond loading a compromised page.
The discovery has sent shockwaves through the cybersecurity community due to the tool’s rare combination of sophistication and accessibility.
Unlike many previous iOS attacks that depended on physical access or highly targeted delivery methods, DarkSword operates through a web-based vector.
This means that simply opening a malicious or hijacked site in Safari or another browser could be enough to compromise a device.
This is making it significantly more dangerous and far-reaching than typical threats.
The tool operates as a "hit-and-run" attack, often described as fileless malware.
It hijacks legitimate iOS processes, steals a wide range of sensitive data in minutes, including passwords from the keychain, iMessage, WhatsApp, and Telegram logs, browser history, contacts, call logs, Health app data, Notes, Calendar entries, and even cryptocurrency wallet credentials, before then exfiltrating everything to a remote server before erasing most traces to avoid detection.
Unlike persistent spyware such as the notorious and the infamous Israeli's Pegasus, DarkSword does not linger after a device reboot, making it stealthier in some ways but focused on quick data grabs.
DarkSword specifically targets iPhones and iPads running iOS 18, particularly versions 18.4 through 18.7, which were released in 2025.
As of early 2026, roughly a quarter of active iPhones.
What this means, potentially over 200-300 million devices remained on these older versions, leaving a massive pool of potential victims.
The exploit has been embedded in legitimate-looking websites, including news outlets and government sites in Ukraine, as part of watering-hole attacks.
It has been linked to Russian state-sponsored groups like UNC6353 for espionage against Ukrainian targets, as well as commercial surveillance vendors such as Turkey's PARS Defense, which deployed it against users in Saudi Arabia, Turkey, and Malaysia. Malware payloads delivered via DarkSword include families like GHOSTBLADE, GHOSTKNIFE, and GHOSTSABER.
Compounding the danger, a newer version of the DarkSword kit was publicly leaked on GitHub around March 23, 2026.
The code, which consists of only simple HTML and JavaScript files with English comments and clear instructions, was left unobscured, allowing even low-skill hackers to copy, host, and deploy it on their own servers in minutes.
Experts described it as "way too easy" to repurpose, warning that nation-state-grade iOS exploitation is now accessible on the open black market, shifting from targeted operations to potentially indiscriminate attacks against everyday users, not just high-profile targets like journalists or activists.
Apple has responded swiftly to the revelations.
The company patched the underlying vulnerabilities in iOS 26 (released last fall) and subsequent updates, including emergency security patches issued around March 11, 2026, for older devices unable to run the newest iOS versions. Users on iOS 15 and later are generally protected, while those on even older systems (like iOS 13 or 14) receive critical alerts to update.
Apple emphasized that enabling Lockdown Mode blocks these exploits entirely, and features like Safari's Safe Browsing help block known malicious URLs. In statements, Apple stressed that keeping software up to date remains the most effective defense, with a spokesperson noting the company's ongoing efforts to protect users.
