Attackers are profiting from mass-exploiting a fixed vulnerability in the Drupal content management system that allows them to take complete control of their servers.
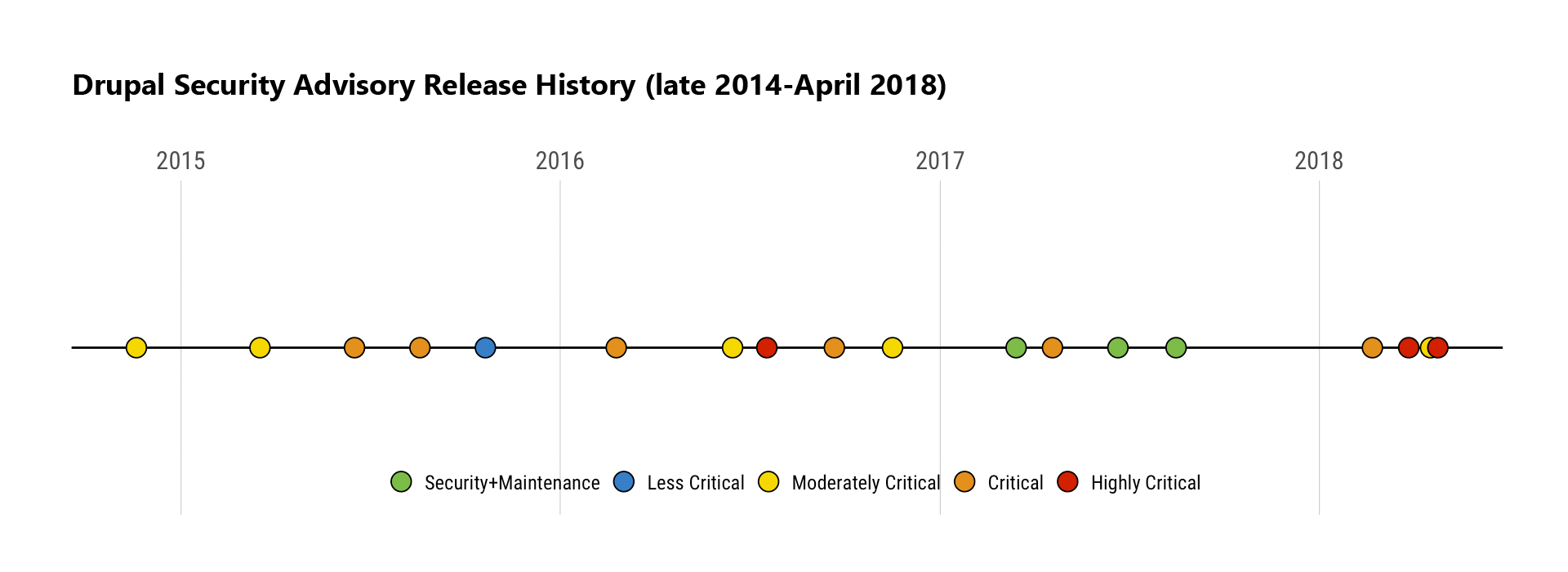
It started out on March 28, 2018, when a patch for a highly critical vulnerability, which facilitates remote code execution against the Drupal CMS was released. The vulnerability was first identified by Jasper Mattson of Druid. It was patched using SA-2018-002 and CVE-2018-7600.
But the problem is because prior to the release of the patch, Drupal had given advanced notice of its impending release and potential consequences tied to the ease of the vulnerability’s exploitation.
In a post, the Drupal team said:
"Sites not patched by Wednesday, 2018-04-11 may be compromised. This is the date when evidence emerged of automated attack attempts. It is possible targeted attacks occurred before that."
Called "Drupalgeddon2," it allows hackers to take complete control of vulnerable servers simply by accessing a URL and injecting publicly available exploit code. For example, they can install multiple malicious payloads, including cryptocurrency miners and software for performing distributed denial-of-service attacks (DDoS) on other domains.
The exploits allows hackers to run the codes of their choice, even without having an account of any type on a vulnerable website.
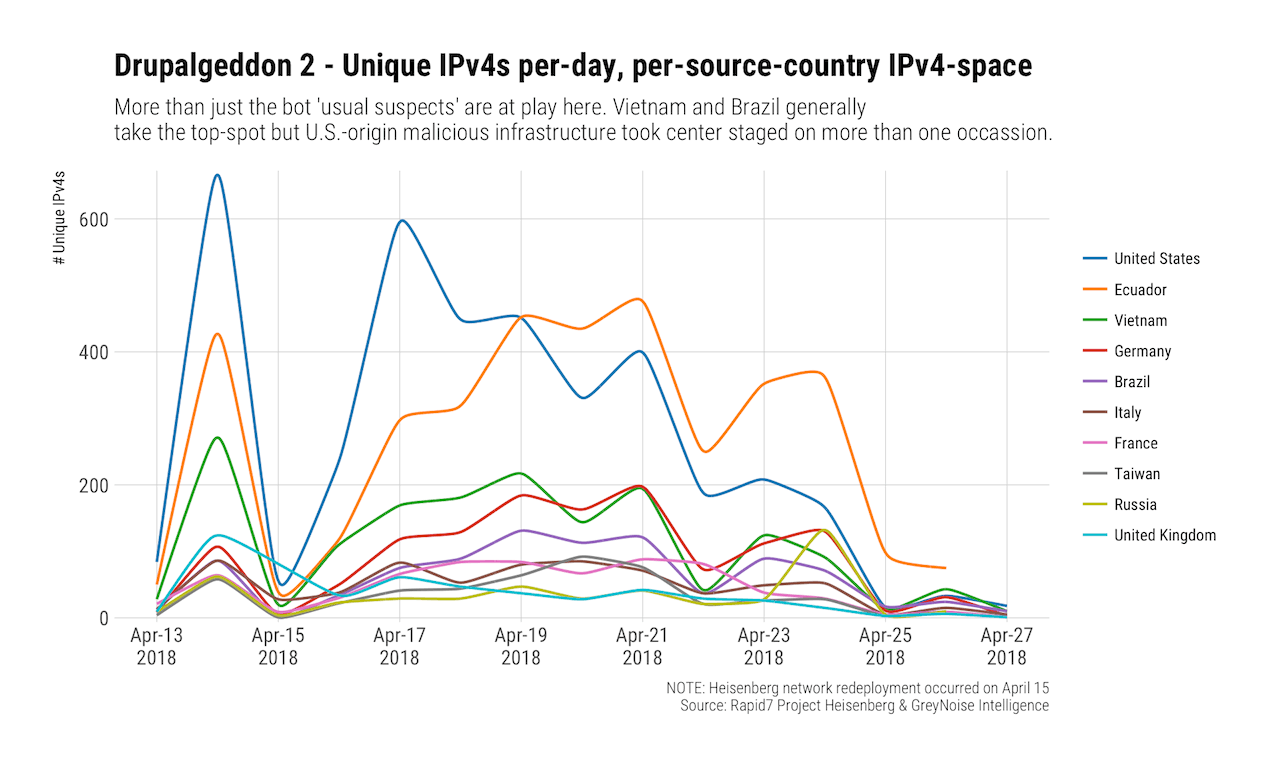
It was on April 13, 2018, that the public exploit code for the vulnerability was made widely available.
Following this, large scale scanning and exploitation happened as more hackers started to hack their ways into Drupal-powered websites. They're constantly probed from multiple IP addresses. Working at a massive scale, hackers tried to hack as many Drupal sites as they can.
it's predicted that most if not all Drupal websites that weren't patched are already hacked.
The remote-code vulnerability on Drupal content management system can be traced back to a October 2014 Drupal vulnerability that was widely exploited by advanced persistent threat (APT) actors and criminals.
The big difference between Drupalgeddon which happened in 2014 and this Drupalgeddon 2, is the money involved.
With cryptocurrencies becoming the hype, many people are trying to mine or exploit or even steal those coins whenever possible. Drupalgeddon2 involves more hackers in illicitly instaling cryptocurrency miners on systems at record rates to generate hundreds of thousands of dollars , with the possibility to go up to even millions if webmasters don't patch the flaw.
