No matter how smart a person is, or how knowledgeable and experienced he/she is, phishing scam is always a problem.
Because there is no guarantee that people will be able to spot and avoid the schemes, phishing won't disappear anytime soon. And here, Facebook wants to help people in avoiding them, by introducing a tool that should lower these concerns.
The company announced a service for domain owners or concerned users, allowing them to watch for sketchy versions of web addresses that might indicate a phishing attempt.
The tool is called 'Certificate Transparency Monitoring'. The Facebook-hosted application allows anyone to signup for free for this service using their Facebook account, and submit domains they'd like to monitor.
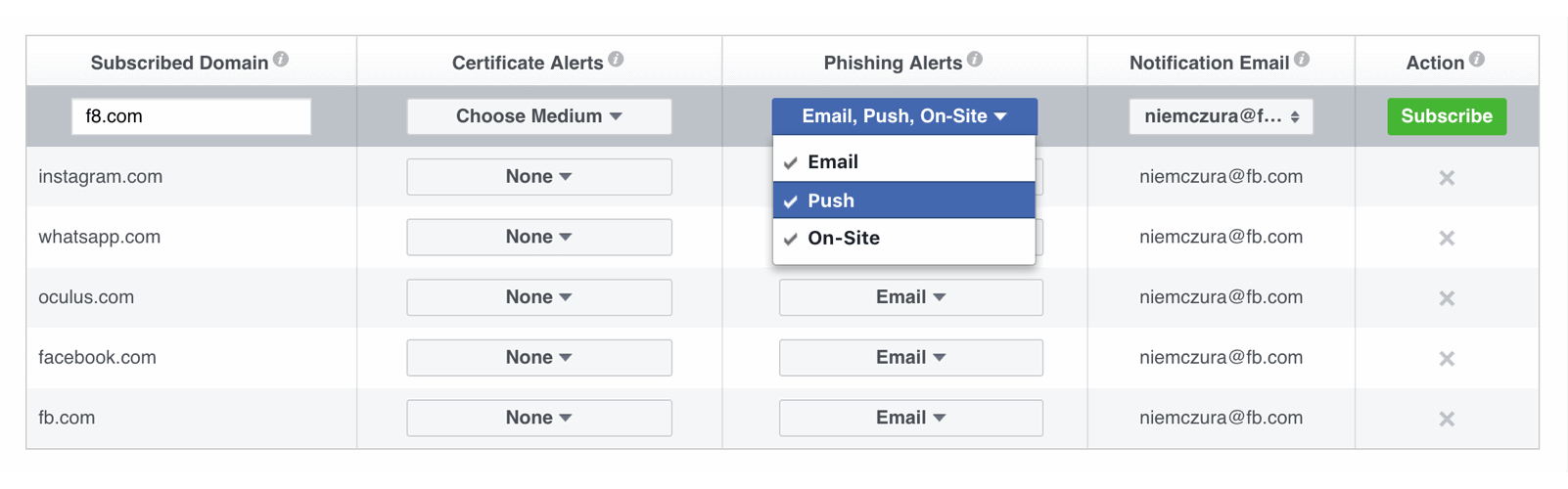
After users entered the domains they want, Facebook will then continuously scan public Certificate Transparency (CT) logs, which hold information about new domains that recently obtained an SSL certificate. The tool will then warn website owners about new sites found in these CT logs that use a similar name to theirs.
This way, developers can check whether the domain name in question is indeed a scam, or a false positive.
And it's indeed a scam, they can contact the certificate authority that issued it to have it revoked, contact browser vendors to blacklist the domain, reach out to domain registrars to suspend it, and alert staff or users about possible incoming attacks.
This phishing detection from Facebook was first developed in 2016 on the premise that if someone gets an SSL certificate for a site with a domain very similar to another, they are most likely to be malicious.
Users need to specify the domain name to Facebook's tool, and it will do the rest, explained Facebook security engineer David Huang. "For example, if you subscribe to phishing alerts for a legitimate domain ‘facebook.com,’ we’ll alert you when we detect a potential phishing domain like facebook.com.evil.com and other malicious variations as we see them."
Scammers that want to do phishing schemes on people can also host their site on domains that are subtler. For example, helpdesk-facebook.com, and send their phishing attacks from there. They also use common misspellings, like faecbook.com, or those who nest multiple subdomains to hide the real domain offscreen, like facebook.com.on-a-long.subdomain-that-will-not-be-fully-shown-on-mobile-devices.com.
The tool also looks for "IDN homograph attack", which is a practice of registering domains with internationalized Unicode characters in its name.
This should make it able to spot a 2016 case where a Russian website owner used ɢoogle.com, with the "G" letter using Unicode.
Facebook's tool looks for all these variations in domains it encounters by watching the stream of certificates being issued to new domains.
"We have been using these logs to monitor certificates issued for domains owned by Facebook and have created tools to help developers take advantage of the same approach," reads the Facebook blog post.
