Cybercriminals are probably known to work and operate on the dark side of the web. But that doesn't mean they cannot be where people usually hang out.
With more sophisticated strategies that develop as technology evolves, those cybercriminals have found just another way to spread their malware: uploading their cryptocurrency mining code to GitHub, according to security researchers at security company Avast in March 2018.
Here, the cybercriminals use GitHub's 'fork' feature to make copy of someone else's project to build their own, to then hide those malicious executables inside directory structures of these new projects, said the researchers.
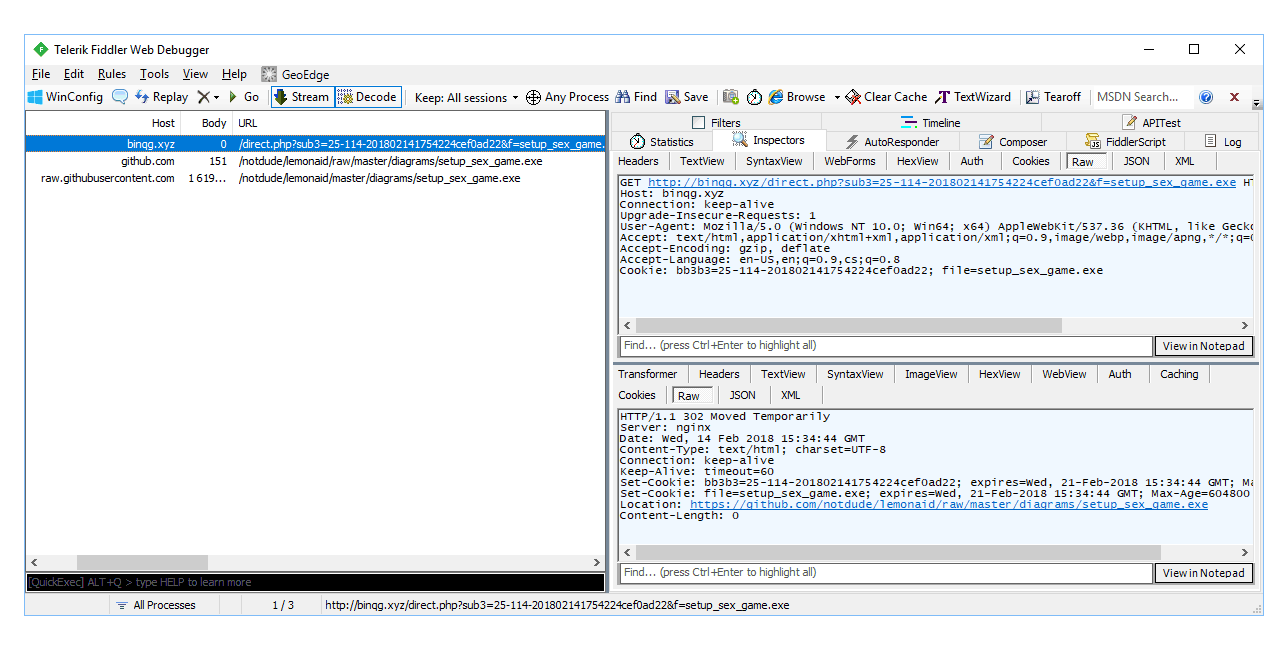
To spread the malware, the criminals don't have to make people download the executables from GitHub. Instead, the malware can spread through phishing campaigns the criminals are doing.
The strategy goes like this: when visitors of a site see the phishing ads and clicks on one, the executable loads and does it work by telling the visitors to update their Flash Player.
Here, the visitors will be directed to a fake update, and if downloaded, will infect them with the crypto-malware.
In a study by academics from Universidad Carlos III de Madrid and King’s College London on January 3rd, 2019, it was discovered that GitHub becomes the most popular platform for hosting such malware:
Usually, the nature of cryptocurrency malware is to get the most out of an victims' CPU resources to extensively mine cryptocurrencies. But this would make their victims aware as they will see a massive decrease in CPU performance, uncloaking the attackers' stealth attack.
Acknowledging this, the cyberciminals have opted to modify how the malware works, by making it to use a maximum of half of infected computers' CPU resources. This way, the malware can remain undetected for a longer period of time.
The researchers also found that the mining malware are hosted as torrents, attachments in Discord channels, as well as obfuscated through various URL-shortener services.
In addition to this, the malware also installs a malicious Chrome extension which can inject a command to automatically click on ads in the background, allowing the attackers to get even more money from their cryptojacking campaign.
Michal Salat, the director of threat intelligence at Avast, said that:
"By using less CPU power, the cybercriminals keep a low profile and maximize their profit by going unnoticed and thus prolonging the time they are able to exploit the infected hardware for more money."
The malware itself is primarily designed for mining Monero, which is somehow popular among cryptocurrency criminals.
While it's unusual for cybercriminals to put their malware codes on GitHub, the popular place for programmers and coders to hang out, cybercriminals that do put their codes on GitHub, are benefiting from GitHub's unlimited bandwidth.
While GitHub has been actively working with Avast to remove malicious forked projects, the actors are persistent as they repeatedly upload their forks to the repository.
This makes it difficult for GitHub, which said that it doesn't actively moderate contents people share on its platform, and only investigate contents that may be in violation of its Terms of Service only after receiving reports.
"GitHub has been taking down the malware as they discover it and we are working with them to provide them with the latest malicious repositories to ensure take down before any one is able to download the malicious code," continued Salat.
Avast recommends GitHub users to avoid suspicious forked repositories, and use only the official ones or trusted forks as they are less likely to be compromised.
Besides GitHub and others shown above, the researchers also found that the criminals are also using other legitimate services like Dropbox, Bitbucket or 4sync, and even Google.
Further reading: GitHub Announces Unlimited Free Private Repositories And A Unified Enterprise Offering
