
OnlyFans has evolved beyond its original plan, and that apparently translates to business.
But that business also translates to the benefits of many other people. Not only that the platform provides a place for content creators to earn money, because it also provides a venue for hackers to steal information from unsuspecting adult content seekers.
It's realized that a malware campaign is using fake OnlyFans adult contents to lure people into installing a remote access trojan known as 'DcRAT,'
Upon installing this malware, the threat actors behind the campaign can steal data and credentials.
And worse, because the hackers can also used it to deploy ransomware on infected devices.
OnlyFans is a content subscription service where paid subscribers can access private photos, videos, and posts from its content creators.
OnlyFans is extremely popular amongst adult models and celebrities, as well as social media personalities. For this reason, OnlyFans is a widely-used platform, and has a highly recognizable brand.
The hackers know this, and this is why it uses it as a bait to lure people who are looking to access paid content for free.
The malware, DcRAT, is a modified version of AsyncRAT that is already freely available on GitHub, but has been abandoned by its author after several abuse cases surfaced online.
What DcRAT is capable of, is performing keylogging, webcam monitoring, file manipulation, and remote access. And because it's an information stealer, it can also steal credentials and cookies from web browsers, or snatch Discord tokens.
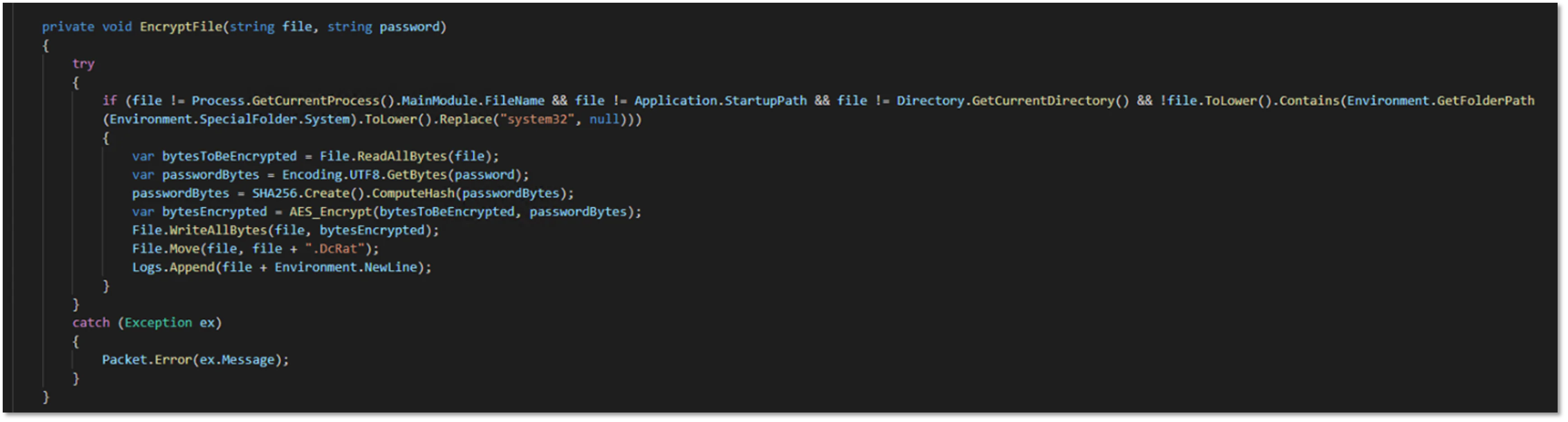
Additionally, DcRAT features a ransomware feature, which is able to target all non-system files and appends the .DcRat filename extension onto the encrypted files.
According to a blog post, the campaign discovered by eSentire has been spreading ZIP files that contain a VBScript loader the victim is tricked into executing manually, thinking they're about to access premium OnlyFans collections.
One sample of the baits, include nude photos of former adult film actress Mia Khalifa.
When the VBScript loader is loaded, it quickly checks the system's operating system, and then creates a 32-bit process.
It then extracts dynwrapx.dll, and registers the DLL file with the Regsvr32.exe command.
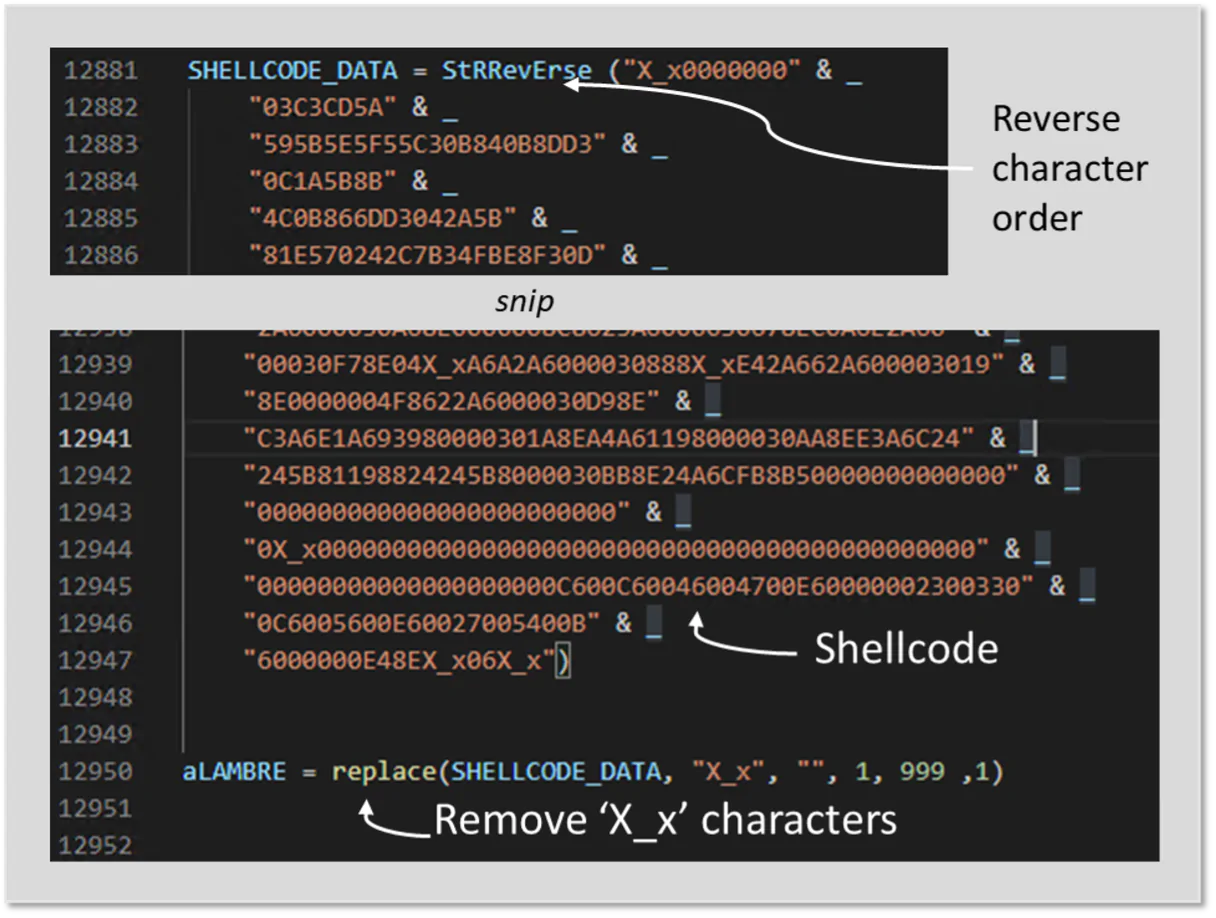
This gives the malware access to DynamicWrapperX, a tool that enables calling functions from the Windows API or other DLL files.
Ultimately, the payload of the malware, named 'BinaryData,' is loaded into memory and injected a legitimate part of the .NET Framework, which makes the malware capable of avoiding antivirus software checks.
This malware campaign shows how far hackers have gone to lure people into believing that what they see is the real thing, when in fact, it is not.
This is the reason why people on the web must always exercise caution when downloading archives or executables from dubious or questionable sources, especially those offering free access to premium/paid content.
Read: Mia Khalifa, The Internet Phenomenon That Far Outlived Her Porn Career
