Trickbot, the computer malware that target victims to steal their credentials, is so persistent that it goes from troublesome to intimidating.
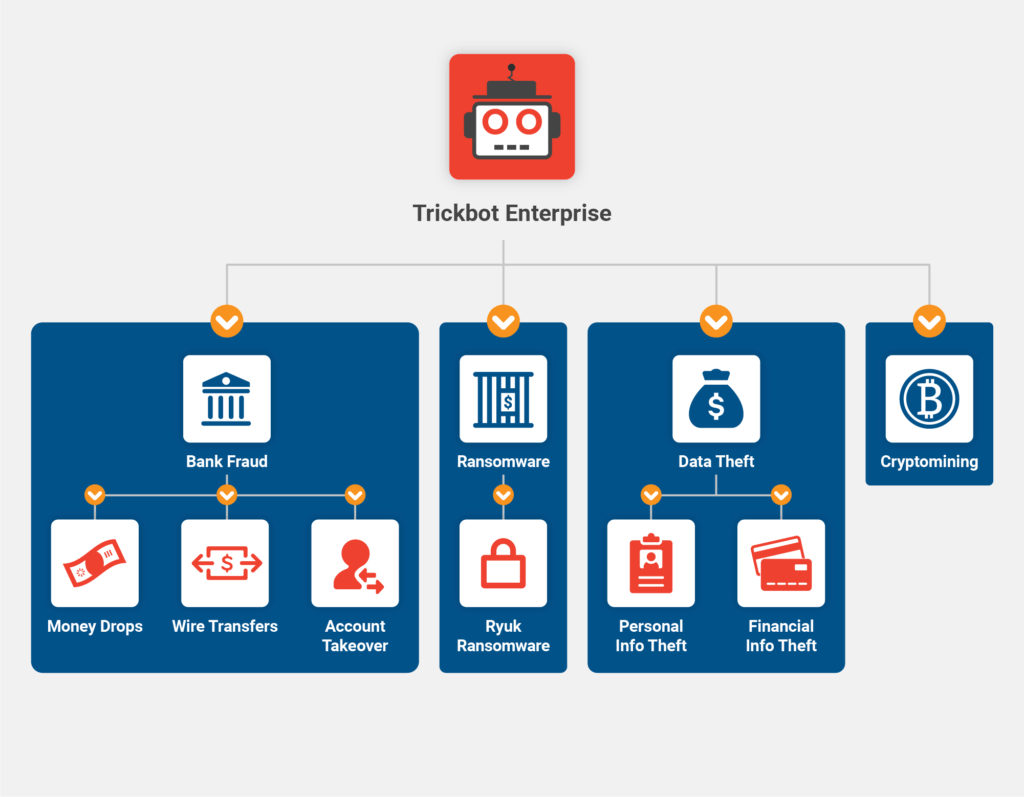
Trickbot is a trojan, capable of infecting victims using Microsoft Windows and some other operating systems. Initially, when it first appeared back in 2016, the malware is intended to steal sensitive information, like banking details and other credentials.
But it seems that the bot has a new trick under its sleeves.
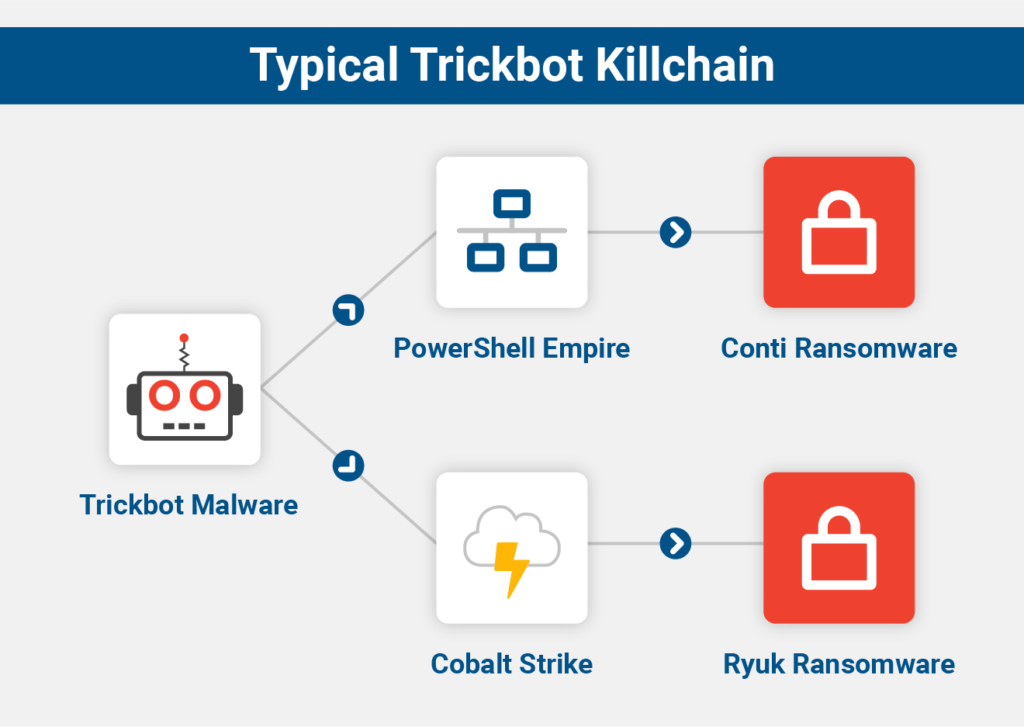
After surviving takedown attempts by Microsoft, a group of cybersecurity companies and even U.S. Cyber Command, the malicious actors behind the malware seems to have extended its abilities by making it modular.
The creators of the malware have enhanced TrickBot with a new technique, making it capable of infecting targets deep down below their operating system, and straight into their firmware.
According to security firms AdvIntel and Eclypsium in a joint report, it was revealed that the previously undisclosed module in the malware can check its victim computers for vulnerabilities that would allow hackers to plant a backdoor into target computers' 'Unified Extensible Firmware Interface'.
Unified Extensible Firmware Interface or UEFI, is responsible for loading a device's operating system when it boots up. In other words, UEFI works down below and beyond the operating system.
Because UEFI runs outside the system's hard drive and on computer chips that reside on the motherboard, TrickBot that can work in this environment means that it can evade most antivirus solutions.
The malware can do what it wants, without having to really worry about detections.
What's more, running on UEFI means that TrickBot can also evade software updates, and even a total format and reinstallation of the computers' operating system. In other words, it may remain persistent, even if the target replaces the hard drive.
Among others, TrickBot can now:
- Remotely brick targets at the firmware level through a typical malware remote connection.
- Bypassing security controls such as BitLocker, ELAM, Windows 10 Virtual Secure Mode, Credential Guard, endpoint protection controls like A/V, EDR, etc..
- Setting up a follow-on attack that targets Intel CSME vulnerabilities, some of which require SPI flash access.
- Reversing ACM or microcode updates that patched CPU vulnerabilities like Spectre, MDS, etc..
"The possibilities are almost limitless," AdvIntel and Eclypsium said
"The group is looking for novel ways to get very advanced persistence on systems, to survive any software updates and get inside the core of the firmware," said Vitali Kremez, a cybersecurity researcher for AdvIntel and the company's CEO. "If they can successfully penetrate a victim machine's firmware, Kremez adds, "the possibilities are endless, from destruction to basically complete system takeover."
Using a technique called the 'TrickBoot', Kremez considered the authors of the malware among only a handful of experienced hackers that aren't state-sponsored, to have experimented UEFI-based attacks in the wild.
Before this, the only malware that is known to have the ability to tamper with UEFI or BIOS firmware were 'LoJax' or 'MosaicRegressor'.
Both are malware strains developed by state-sponsored hacking groups.
The authors behind this persistent and dangerous malware, is believed to be from Russian or China, which are countries where hackers have gained a reputation as some of the most dangerous cybercriminal hackers on the internet.
To combat this kind of malware, it requires new attention to vulnerable computer components that are often ignored.
Both Eclypsium and AdvIntel advise companies to check their PCs' firmware to determine if it's vulnerable. They also need to update their firmware when vendors make new code available, and perhaps most importantly, check their PCs' firmware for tampering as part of their response to any detected TrickBot.
"You do have all of these things in your environment as an enterprise," said Eclypsium cybersecurity researcher Scott Scheferman, "and the likelihood of you getting a TrickBot infection over the next three months is very high. So it's time to really, actually start to pay attention."
