Almost anything that is accessible through the web, can be accessed by anyone, as long as that person has the privilege that usually comes in the form of login credentials.
The same goes to data from mobile apps. While putting things on the web is certainly convenient, things can be an issue when misconfiguration happens.
Through cloud technology for example, developers can create new apps, easier than ever before. But by putting the data to the cloud, the apps' data are essentially placed on the web, where anyone can see and access, as long as they know how to do it.
And here, a study by mobile security firm Zimperium, found that tens of thousands of Android and iOS apps have misconfigurations in their cloud infrastructure, and could have allowed hackers to gain access to their users' private data.
The misconfiguration didn't really restrict unauthorized access, as Zimperium has found after running automated analysis on more than 1.3 million Android and iOS apps to detect common cloud misconfigurations that exposed data.
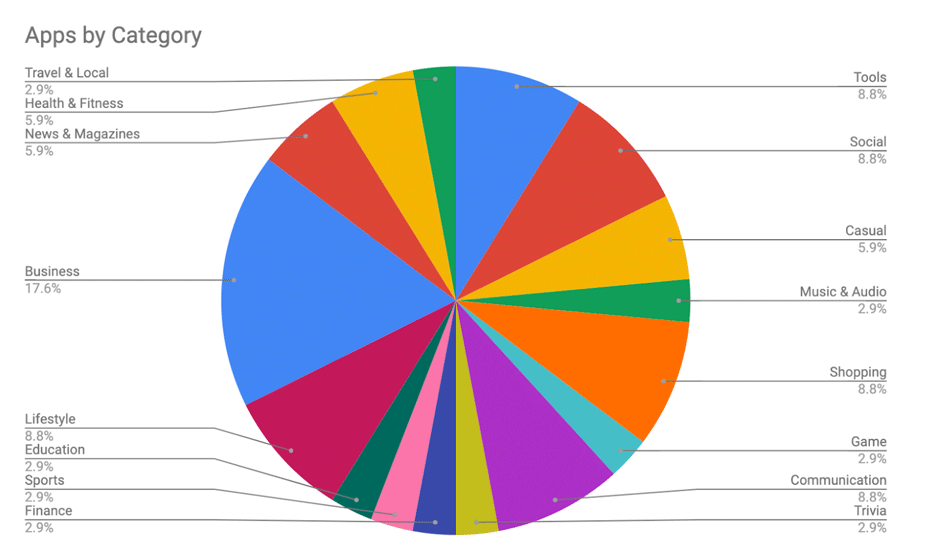
According to the researchers at the company, almost 84,000 Android apps and nearly 47,000 iOS apps are using public cloud services - like AWS by Amazon, Azure by Microsoft, Google Storage and Google Firebase to name a few - in their backend as opposed to running them in their own servers.
For a good thing, running apps on popular cloud services allows a reduced complexity of configuring access to relevant storage container, and allowing the developers to “focus on the important things.”
However, out of those many, "14% of mobile apps that use cloud storage had unsecure configurations and were vulnerable to the risks described in this post," wrote Zimperium on a blog post.
"In apps around the world and in almost every category, our analysis revealed a number of significant issues that exposed PII, enabled fraud and/or exposed IP or internal systems and configurations."
What this means, 11,877 Android apps and 6,608 iOS apps were exposing users' personal information, passwords, and even medical information.
“It's a disturbing trend,” said Shridhar Mittal, Zimperium's CEO, as quoted by Wired that first reported it.
“A lot of these apps have cloud storage that was not configured properly by the developer or whoever set things up and, because of that, data is visible to just about anyone. And most of us have some of these apps right now.”
Following the findings, the researchers at Zimperium started reaching out to a number of the app developers to inform them about this cloud exposure.
But the response was minimal, as many of the apps were still exposing sensitive user data.
This kind of hacking is nothing new for e-commerce sites, or for platforms that run on the cloud.
But in this case, the incident involving the leak in the cloud servers is caused by the developers' failure to properly configure their servers, and is still leaking user data because many of the developers don't seem to be bothered by this fact.
In other words, at this time, it is still raining user data from those cloud providers.
Not only that the data was exposed to the public, as the servers' setting was also read-write, meaning that hackers have the ability to change or even overwrite the data, creating additional potential for fraud and disruption.
“For users, their personally identifying information could be exposed, medical information, test results, phone numbers, even passwords to certain accounts," Mittal said. "And for enterprises this creates risk, too. Attackers could gather information that helps them hack in deeper.”
Because of the scope, the researchers at Zimperium who simply cannot notify the tens of thousands of developers and expect positive feedback, chose to publish their findings to the public.
However, the researchers stopped short from naming the affected mobile apps in their report, because the leak involves sensitive data, including an app from a Fortune 500 company, and apps with millions of users.
Zimperium is one of three mobile security firms that participates in Google's App Defense Alliance initiative, conducting automated app scanning for the company's Google Play store.
According to Mittal, the tools his company used in this research, are the same with what it uses for its App Defense Alliance work.
However, in this case, Zimperium looked only exposures and not for potentially malicious functionality.
By making the findings public, Mittal hopes to raise awareness about mobile cloud misconfigurations, and hopes that the findings can motivate developers to take a closer look at their infrastructure.
