When it comes to the web, phone number should be considered personal information.
As many services rely on this data for authentication and other purposes. And if it falls to the wrong hands, many bad things could happen. This happened on Twitter, as the social media revealed an "incident" in how the service handles users' phone numbers.
The company said that it had removed "a large network of fake accounts" responsible for uploading lists of phone numbers and then using Twitter’s own API to match them to individual usernames.
"This data may have inadvertently been used for advertising purposes, specifically in our Tailored Audiences and Partner Audiences advertising system," said Twitter on its help page.
The first problem resides in Tailored Audiences, which is a version of an industry-standard product that allows advertisers to target ads, and in this case, to Twitter users based on the advertiser's own marketing lists (e.g., email addresses or phone numbers they have). Partner Audiences allows advertisers to use Tailored Audiences features to target ads to Twitter users provided by third-party partners.
"When an advertiser uploaded their marketing list, we may have matched people on Twitter to their list based on the email or phone number the Twitter account holder provided for safety and security purposes. This was an error and we apologize," said Twitter.
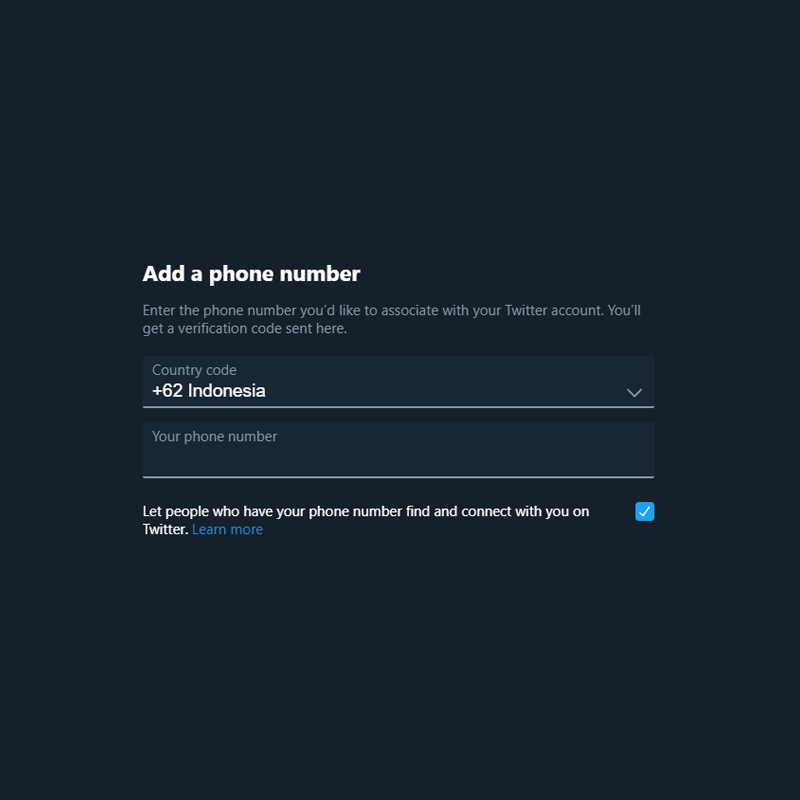
Requiring a phone number is becoming common on social media networks. With this data, they can offer a whole more option, including to find people they already know on the app. To do this, social media needs a dedicated API for the job.
Unfortunately, the APIs used often contain limitations to keep bad actors from exploiting the tools.
In Twitter’s case, this is its second problem. Its API rejects anyone who tries to upload a list of sequential phone numbers - an indication that it’s not a user uploading their contacts. A way around this, is to upload randomized information so the phone numbers wouldn't be sequential strings.
This allowed some people to match phone numbers to usernames for more than 17 million Twitter users, including celebrities and public officials.
According to the Electronic Frontier Foundation (EFF) on its web page, this activity is used to create reverse-lookup tools, in order to match specific users, or their accounts.
So far the problem, said the EFF, the flaw only seems to affect Twitter users who have a phone number associated with their account, and have “phone number discoverability” enabled in their settings.
EFF suggests that:
According to Twitter, the API exploit is believed to have originated from IP addresses in Iran, Israel, and Malaysia.
“It’s possible that some of these IP addresses may have ties to state-sponsored actors,” a spokesperson wrote.
This isn't the first time Twitter has issues handling users' phone numbers. Back in October 2019, the company confessed that it “accidentally” allowed advertisers to targeted ads at some users using their email addresses and phone numbers, which they provided only for two-factor authentication.
This is why Twitter started enrolling its 2FA program without requiring a phone number. What’s more, the company also started providing an option to disable SMS-based 2FA.
