Apple's iOS is long touted as a more secure platform and mobile operating system than Android. But that doesn't mean it's flawless.
Apple is quick in patching bugs whenever it sees them, especially during the rough iOS 13 launch. But there is one persisting bug that has yet to go away. According to a security consultant part of the Proton community, iOS 13.31 or later have an unpatched security bug that prevents virtual private networks (VPNs) from encrypting all traffic.
While Apple can easily integrate VPN certificate to create a VPN tunnel, and can protect users while it is on, it's the connections made before activating the VPN that is affected by this bug.
In other words, only the connections made after the VPN is activated is protected, and not the ones before as they remain outside the VPN's secure tunnel.
The bug in question that can lead to some internet connection bypassing VPN encryption, is putting users at risks in exposing their data or have their IP addresses leaked, despite that reassuring little VPN icon on the screen.
This VPN bypass vulnerability was made public by ProtonVPN to ensure users and other VPN providers are made aware of the issue.
According to ProtonVPN in a blog post:
The bug is due to Apple's iOS not terminating all existing Internet connections when the user connects to a VPN, and not having iOS to automatically reconnect all existing connections to the destination servers after the VPN tunnel is established.
"Most connections are short-lived and will eventually be re-established through the VPN tunnel on their own," ProtonVPN explains. "However, some are long-lasting and can remain open for minutes to hours outside the VPN tunnel."
During the time the connections are outside of the VPN secure communication channels, any data transferred to the internet can lead to serious consequences.
"The problem,” ProtonVPN said, “could impact any app or service, such as instant messaging applications or web beacons."
For instance, user data could be exposed to third parties if the connections are not encrypted themselves, and IP address leaks could potentially reveal the users' location and expose them and destination servers to attacks.
Even though users should only see traffic being exchanged between their devices, local IP addresses, and the VPN's servers, other IP addresses will also show up.
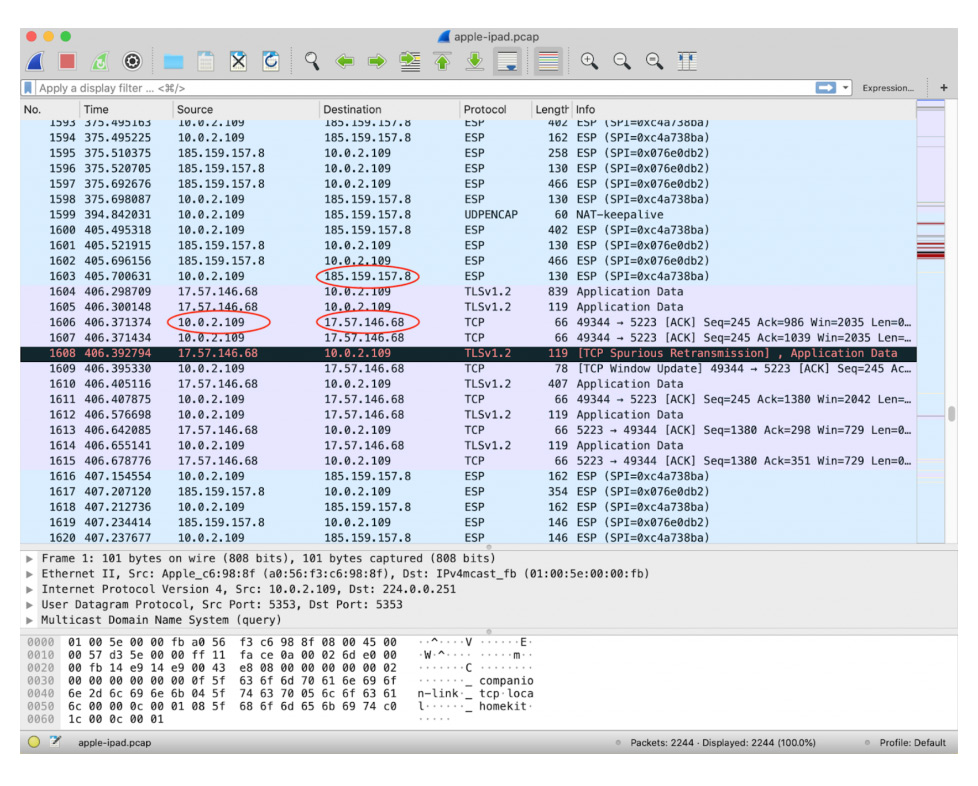
In an example screenshot above provided by ProtonVPN, showed that Apple server IPs can also be disclosed because of previously opened connections not being terminated before the VPN connects.
While ProtonVPN said that Apple's push notification feature is a good example of a process using connections to Apple servers that won't be closed automatically, this particular VPN bypass bug can affect any service or app running on the user's iOS device.
"Those at highest risk because of this security flaw are people in countries where surveillance and civil rights abuses are common," ProtonVPN said, adding that "neither ProtonVPN nor any other VPN service can provide a workaround for this issue because iOS does not permit a VPN app to kill existing network connections."
Most worryingly, ProtonVPN explained that it first discovered the bug in iOS 13.3.1 and told Apple - who later acknowledged it - but has since failed to provide any subsequent fix, even after the release of iOS 13.4 two months later.
Apple recommends users to use Always-on VPN to mitigate this problem. However, since this method uses device management, it cannot be used to mitigate the vulnerability for third-party VPN apps.
As a workaround, ProtonVPN recommends users of third-party VPN to connect to a VPN server, turn on Airplane Mode to kill all existing connections, and then turn off Airplane Mode to allow the VPN to reconnect, and having all connections to run inside the VPN tunnel
The mitigation isn't entirely reliable, said ProtonVPN, so iPhone and iPad owners who rely on VPNs should be careful until Apple puts a proper fix.
