Coding requires skills and experience. However, even the most skillful person can make mistakes because after all, we are all humans.
Maxthon (formerly named MyIE2) is a freeware web browser developed by Maxthon Ltd.. According to the company’s website, 670 million users use it as a default browser. This popular browser from Beijing, China, experienced this human error, which resulted in a bug in its Microsoft Windows app.
The vulnerability was caused by an unquoted search path found in the installation phase, resulting in potential abuse by hackers.
Discovered and reported by security firm SafeBreach back in September 2019, the anomaly allowed hackers to install a program into a service that is run by the NT AUTHORITYSYSTEM.
When installing the Maxthon browser on Windows operating system, it creates an executable named MxInstall.exe, which is written to a temporary folder. What it does, is to create the service using the WinAPI CreateServiceW function.
But before it can do that, it calls a sprintf command in order to format the buffer which contains the path of the service executable.
This generates the unquoted search path C:\Program Files (x86)\Maxthon5\Bin\MxService.exe.
The space in Program Files makes Maxthon's CreateServiceW function clueless in realizing whether it’s part of the path or whether it’s an argument. As a result, the service tries to parse it by itself, by first searching and executing Program.exe in users' C: drive, which doesn't exist.
The service does this before it moves to other executables to fire up the actual browser app.
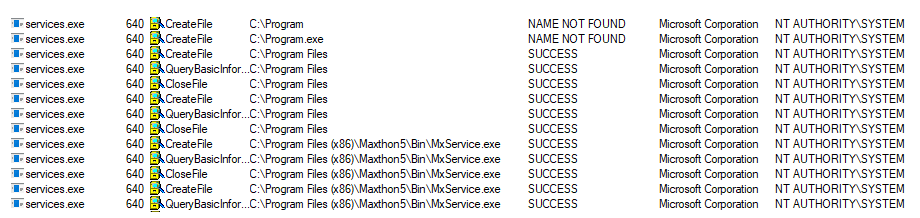
Because of this, hackers can place a dummy executable with that name, and the browser would think it’s harmless.
When executed by the browser, the hackers can have the potential access to the victims' computer, install malicious code, and bypass Windows security to run apps that shouldn't get execution permission otherwise.
Making things worse, this bug persistent. This is because once hackers put their malicious executable file in one of the path mentioned earlier, the service will load the malicious code each time it is restarted.
What's more, the vulnerability can give attackers the ability for making their malicious payloads to be executed by a signed service. This ability might be abused by hackers for different purposes, such as execution and evasion.
"This way the malicious payload might not be detected by security products, because the service process which executes the attacker’s payload is signed, and executes it 'natively'. No suspicious action is required by the attacker. The serviceit just executes the malicious executable once it is started," explained SafeBreach.
SafeBreach said Maxthon for Windows version 5.1.0 to 5.2.7 were affected.
SafeBreach reported this issue to Maxthon on September 3rd, 2019, After confirming the bug in September 17th, Maxthon released an issue CVE-2019-16647 on September 27th.
