
The dark web is a place where Google and others don't exist. It's literally the corners of the web where people are anonymous and anything can happen.
To get into this hidden network, people can use the Tor browser, the software popular for those who dare venture beyond the ordinary. This allows them to do things like browsing, e-commerce, chat and others, all within the dark web.
Unfortunately, bad actors are leveraging this fact.
Scammers know that people accessing the dark web should have something they need that isn't available in the surface web. Because Bitcoin is the most popular currency for transaction in the dark web, the scammers also know exactly that there is a high chance that those dark web Tor users would use their Bitcoins in one way or another.
And here, researchers from cybersecurity firm ESET have discovered a malicious version of the Tor browser.
With this a trojanized version of the official Tor browser package, the bad actors were able to steal more Bitcoin from victims.
The process goes like this:
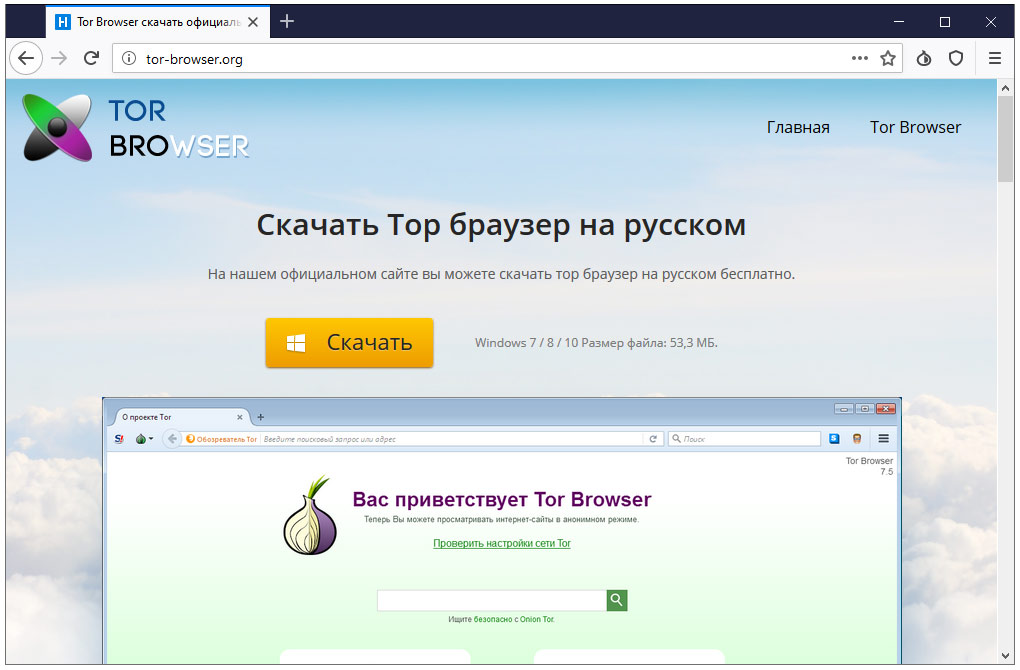
The scammers create two websites. The first website displays a message in Russian claiming that the visitor has an outdated Tor Browser. The message is displayed even if the visitor had the latest Tor Browser version installed.
When the visitors click on the 'Update Tor Browser' button, the visitors will be redirected to a second website, where they can download an installer for the rogue Tor browser.
Explaining about the two websites, ESET on its web page said that:
"The malicious domain torproect[.]org domain is very similar to the real torproject.org; it is just missing one letter. For Russian-speaking victims, the missing letter might raise no suspicion due to the fact that “torproect” looks like a transliteration from the Cyrillic. However, it does not look like criminals relied on typosquatting, because they promoted these two websites on various resources."
These websites, and the malicious Tor browser, were first promoted in online Russian forums somewhere between 2017 and 2018.
When the rogue Tor is installed and opened, it still allows users to use the browser like they normally would. It has exactly the same design and functions, and works the same as the legitimate Tor browser.
There is little to suggest to the user that something might go awry.
However, the rogue intentions of the browser lies in the background.
First of all, all trojanized Tor Browser use the same User-Agent. This acts as a fingerprint, allowing the bad actors to detect and tract their victims when they browse the web.
The scammers improvised this by also changing the xpinstall.signatures.required settings, which disable the digital signature check for installed Tor Browser add-ons. This way, the attackers can modify any add-on and make it load on the browser without any complaint about it failing its digital signature check.
Second, the bad actors modified the HTTPS Everywhere built-in add-on. The modification adds a content script that will be executed on load in the context of every web page the victim is seeing.
This allows the criminals to know what website the victim is currently visiting, and perform specific actions on them.
For example, it can do a form grabbing, scrape, hide or inject content of a visited page, display fake messages, etc..
Third, the fake Tor browser also prevents victims to update to newer versions of Tor. This is because updating will replace the fake Tor with a non-trojanized, legitimate version. To prevent any update attempts, the scammers disabled all kinds of update settings, and even renamed the updater tool from updater.exe to updater.exe0.
And last but not least, the fourth malicious intention is the payload.
When users try to add funds to their Bitcoin wallet or pay for items using the cryptocurrency, the browser would automatically change the target wallet address to the one owned by the scammers.
ESET researchers identified three Bitcoin wallets used in this campaign. At the time of its findings, the wallets in question had received 4.8 BTC, or about $40,000.

The bad actors were promoting the fake Tor browser as the Russian-language version of Tor, and spread their campaigns through messages on various topics, including dark web markets, cryptocurrencies, internet privacy and censorship bypass.
Specifically, some of these messages mention Roskomnadzor, a Russian government entity for censorship in media and telecommunications.
The scammers even claimed that this version of the Tor Browser has an anti-captcha capability.
The scammers also used Pastebin.com accounts to promote their fake Tor website.
By creating a lot of Pastes optimized for search engines, the scammers were able to rank their posts high for keywords like drugs, cryptocurrency, censorship bypass, and the names of Russian politicians.
"The idea behind this is that a potential victim would perform an online search for specific keywords and at some point visit a generated Paste. Each such paste has a header that promotes the fake website," explained the researchers.
Bad actors in using malicious methods to switch out Bitcoin wallet addresses is nothing new. But embedding that functionality directly inside a browser is less common.
The lesson that should be learned here is that, the best way to use a software is to download it from legitimate sources, and keep it up to date.
