Quantum computing is still under heavy development. But as the technology continues to advance, the need for quantum-resistant cryptography becomes increasingly critical.
Encryptions based on traditional computing system stand no chance against quantum attacks. This makes traditional systems vulnerable to cyberattacks launched by quantum computers.
While quantum attacks have yet to materialize, and that it's expected to take several years, possibly even decades, for quantum computers to really pose severe global risks, certain kinds of encryption are susceptible to an attack called "harvest now, decrypt later" (aka retrospective decryption) in which data that's encrypted today is harvested by threat actors in hopes of decrypting it later when cryptanalysis becomes easier due to technological breakthroughs.
Because of this, Google stressed the importance of taking action preemptively due to the difficulties of implementing new cryptography method across the internet.
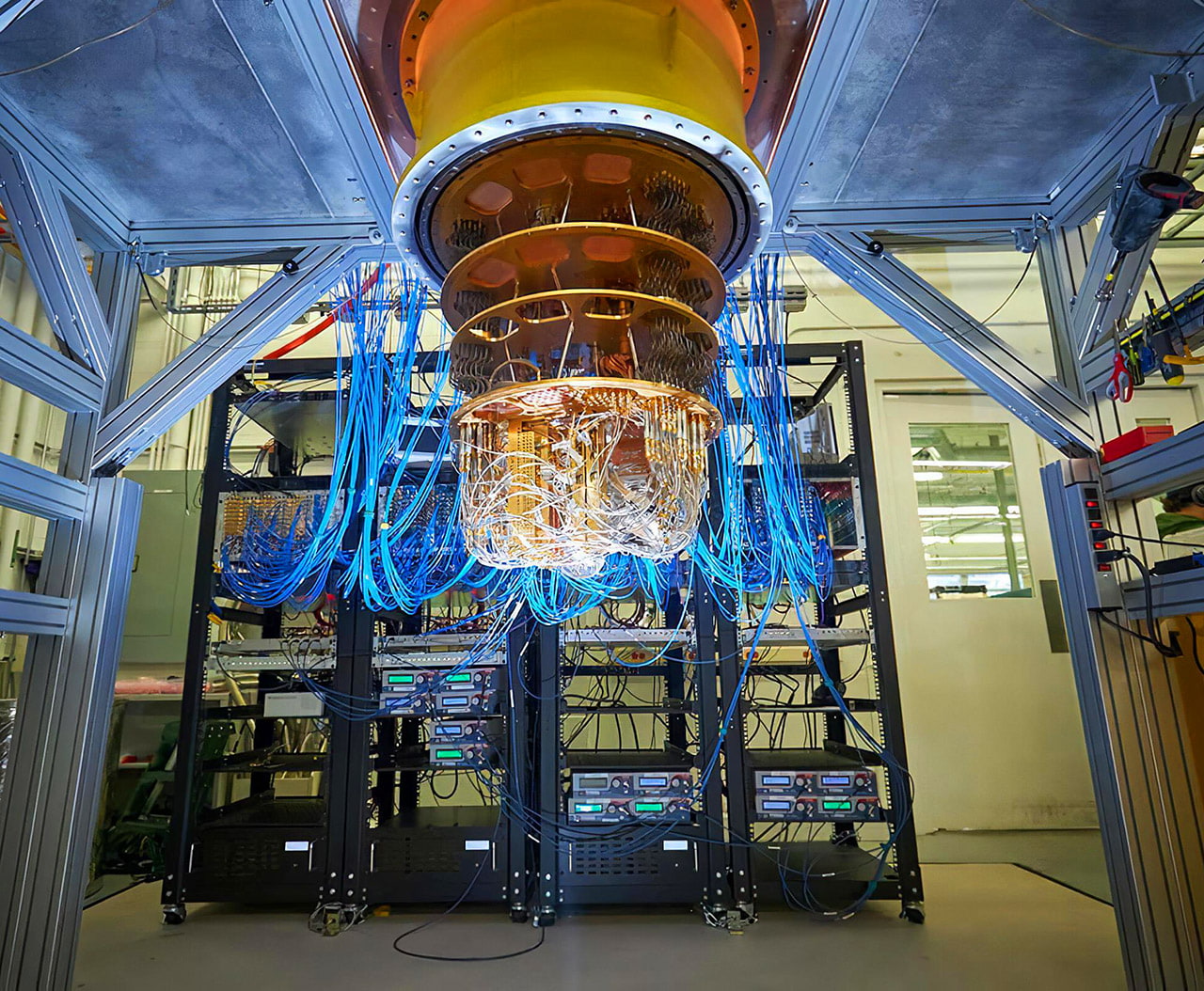
Quantum computers are capable of efficiently performing certain computations in a manner that can trivially defeat existing cryptographic implementations.
In terms of efficiency, quantum computers are still in their early stages of development, and that the technology is expensive and is still unreliable. But the progress of the research suggests that the computer can be much more efficient than traditional computers for certain types of problems.
This is because quantum computers can take advantage of quantum effects such as superposition and entanglement.
Using its unique way working, quantum computers can solve problems and tasks in orders of magnitude faster than traditional computers.
This could lead to major breakthroughs in fields such as cryptography, chemistry, and materials science.
Because of this, Google has partnered with ETH Zurich to develop a hybrid signature scheme using traditional elliptic-curve cryptography and CRYSTALS-Dilithium, a quantum scheme standardized by the U.S. Department of Commerce's National Institute of Standards and Technology (NIST).
By unveiling the first FIDO2 security key implementation designed to withstand quantum-based attacks, Google hopes that its implementation can eventually become standardized and supported by major web browsers.
With the technology, Google announced its plans to add support for the quantum-resistant encryption algorithms in its Chrome browser, starting with version 116.
"Chrome will begin supporting X25519Kyber768 for establishing symmetric secrets in TLS, starting in Chrome 116, and available behind a flag in Chrome 115," said Devon O'Brien said in a blog post.
At this time, the Kyber encryption system has already been adopted by Cloudflare, Amazon Web Services, and IBM.
X25519Kyber768 is a hybrid algorithm that combines the output of X25519, an elliptic curve algorithm widely used for key agreement in TLS, and Kyber-768 to create a strong session key to encrypt TLS connections.
"Hybrid mechanisms such as X25519Kyber768 provide the flexibility to deploy and test new quantum-resistant algorithms while ensuring that connections are still protected by an existing secure algorithm," O'Brien explained.

"In TLS, even though the symmetric encryption algorithms that protect the data in transit are considered safe against quantum cryptanalysis, the way that the symmetric keys are created is not," O'Brien said.
"This means that in Chrome, the sooner we can update TLS to use quantum-resistant session keys, the sooner we can protect user network traffic against future quantum cryptanalysis."
"Bad actors could possibly take advantage of the visibility into these fixes and develop exploits to apply against browser users who haven't yet received the fix," Amy Ressler from the Chrome Security Team said. "That's why we believe it's really important to ship security fixes as soon as possible, to minimize this 'patch gap.'"
The research team emphasized the necessity of a hybrid scheme because at this time, existing quantum-resistant algorithms have exhibited weaknesses.
Kyber itself is an IND-CCA2-secure key encapsulation mechanism (KEM), whose security is based on the hardness of solving the learning-with-errors (LWE) problem over module lattices. Kyber is one of the finalists in the NIST post-quantum cryptography project.
The hybrid, "pre-quantum" security achieves more than 128 bits of security against all known classical and quantum attacks.
The idea is to fit a small enough Dilithium implementation on the hardware-constrained security keys. This was a significant technical feat, achieved through careful optimization.
Google’s implementation meets the expected security key specification and further improvement in signature speed could be achieved through hardware acceleration.
Given that most security keys cannot be upgraded, careful approach is required.
And here, Google’s proof-of-concept source code, which has been made available through the OpenSK project, aims to provide open-source code for hardware security keys. The project in question also includes resources for 3D printing a security key enclosure.
The development comes as Google said it's changing the release cadence of Chrome security updates from bi-weekly to weekly to minimize the attack window and address the growing patch gap problem that allows threat actors more time to weaponize published n-day and zero-day flaws.
Kyber-768 in question is roughly the security equivalent of AES-192.
A more powerful version of Kyber, is Kyber-1024, which aims at security roughly equivalent to AES-256.
