Databases accessible on the web is nothing new. It's in fact made on purpose, in order for easy access and convenience.
The biggest problem about databases on the web is when they aren't properly secured, meaning that anyone with an internet connection and the knowledge can find them.
In the modern days of the internet, hacking and cyber crime are nothing new. They are mostly individuals or groups that seek profit and intelligence data.
And this time, a new kind of cyber attack is different. Called 'Meow', it's goal is to hunt down databases that are accessible on the web without security, by deploying database-seeking bots.
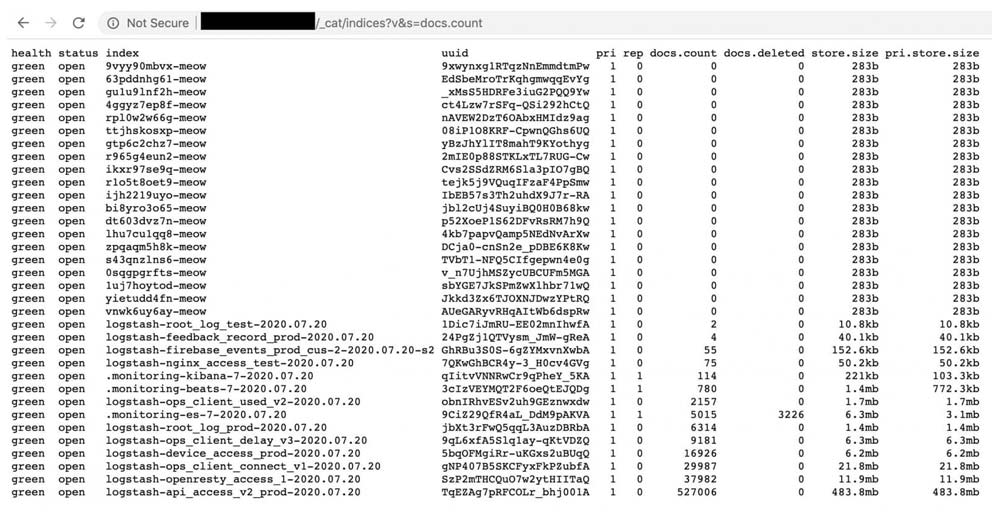
When the bots that are deployed find unsecured databases that run on the Elasticsearch, Redis or MongoDB, the bots will automatically overwrite all of the data, renaming the entry with the word "meow", effectively destroying the contents of the database.
New Elasticsearch bot attack does not contain any ransom or threats, just 'meow' with a random set of numbers. It is quite fast and search&destroy new clusters pretty effectively pic.twitter.com/F8Ke3CI64i
— Bob Diachenko (@MayhemDayOne) July 20, 2020
First discovered by Comparitech head researcher Bob Diachenko, Meow is characterized as being fast and effective in seeking out new targets that have failed to secure access properly.
The first database that was destroyed by Meow, was owned by the UFO VPN that claimed not to keep any logs. Also discovered by Diachenko, the database was initially secured in July only to become exposed again five days later.
And the Meow cyberattack wiped the service out after it was moved to an unsecured database.
Diachenko said that the attacks appear to be an automated script that "overwrites or destroys the data completely."
When Comparitech published its report, Meow managed to compromised more than 4,000 databases, half of which were running Elasticsearch.
It was then reported that Meow can also wipe databases running on Cassandra, CouchDB, Redis, Hadoop, Jenkins, Apache ZooKeeper, as well as on network-attached storage devices.
While attacks on misconfigured databases are not a rare occurrence, some researchers debate whether the mastermind behind the Meow attacks are trying to ‘educate’ administrators to keep their databases secured.
When first observed, researchers starting thinking that the work could have originated from vigilantes trying to give database owners a hard lesson they will never forget.
The reason is because the hackers aren't piggybacking the effectiveness of this campaign, nor extract any data for their own financial benefit.
Meow simply seeks out unsecured databases, to then obliterate them without any message, afterword or explanation.
The hacker launching the campaign does nothing to identify themselves, and seems to want nothing from their hacks.
“I think that … malicious actors behind the attacks do it just for fun, because they can, and because it is really simple to do,” said Diachenko.
