The Tor network is known to be one of the best way to remain anonymous on the web. But it's the Tor's exit node that seems to be the network's big weakness.
In order for a Tor user to browse the web, information is delivered from the source to the destination by bouncing it through multiple nodes. Through each of these nodes that information is decrypted layer by layer to reveal the next node in the circuit to pass the remaining encrypted data.
And when it's about to exit, the information needs to be decrypted to the innermost layer of encryption so the target can understand what's within it. These are the points where data can be read.
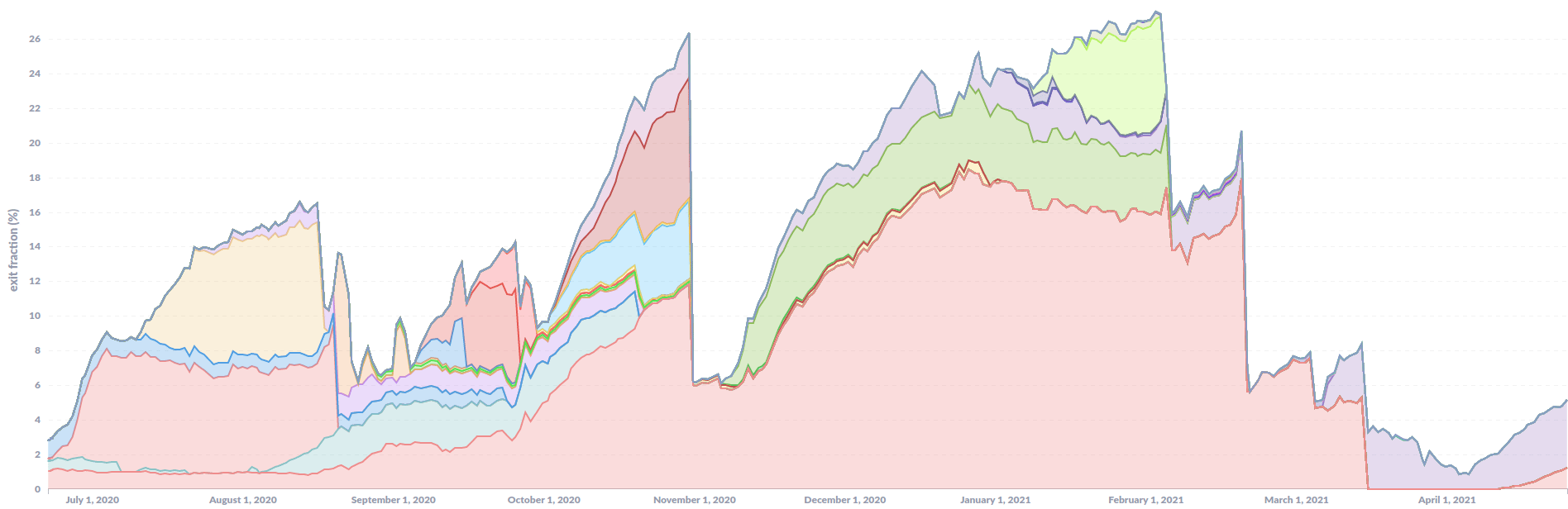
This time, a research found that an unknown threat actor managed to control more than 27% of the entire Tor network exit capacity in early February 2021.
In a Medium blog post, the independent security researcher who goes by the name nusenu, said that it is "largest malicious tor exit fraction I’ve ever observed by a single actor."
The tor network usually consists of less than 1,500 Tor exit relays.
However, in early May 2021, more than 1,000 new unnamed tor exit relays. While should help the growth and speed of the entire Tor network, the new relays apparently came without ContactInfo.
And this raised suspicion because all those relays joined the Tor network within less than 24 hours.
While in most cases, this sudden increase impose little risk for Tor users because they basically get removed right away before gaining any meaningful traction, these nodes were rather persistent.
What's more, the relays were unlike most other relays, as they were not located at one of the usual hosters (OVH, Leasweb, Frantech).
"When I noticed them I thought they are trolling because no one can assume such a large Sybil stays on the network for long, until I got email from them. Someone responded off-list to a short note I wrote to the tor-relays mailing list about this event."
For this reason, nusenu was certain that someone was controlling the exit relays, and that person wasn't happy that his relays were taken down.
After conducting some tracing, including an inverse lookup on the RIPE database, nusenu found the person's email and alleged address being used to register the exit relays.
The main purpose of the attack, according to nusenu, is to carry out "person-in-the-middle" attacks on Tor users.
The entity can do this by manipulating traffic as it flows through the network of exit relays they have control of.
Diving to more details, the attacker performed what's called the SSL stripping method to simply downgrade traffic heading to Bitcoin mixer services from HTTPS to HTTP.
This allows tampering, in which the attacker could replace Bitcoin addresses and redirect transactions to their wallets instead of the user-provided Bitcoin address.
Read: Hacker Hijacked Tor Exit Nodes To Target Users Visiting Cryptocurrency-Related Websites
"If a user visited the HTTP version (i.e. the unencrypted, unauthenticated version) of one of these sites, they would prevent the site from redirecting the user to the HTTPS version (i.e. the encrypted, authenticated version) of the site," the maintainers of Tor Project explained in August 2020.
"If the user didn't notice that they hadn't ended up on the HTTPS version of the site (no lock icon in the browser) and proceeded to send or receive sensitive information, this information could be intercepted by the attacker."
To prevent falling to this kind of attack, websites should always enable HTTPS by default, and deploy .onion sites to avoid exit nodes.
The team at the Tor Project added that at this time, they are working to create a "comprehensive fix" to disable plain HTTP in the Tor Browser.
"The risk of being the target of malicious activity routed through Tor is unique to each organization," the U.S. Cybersecurity Security and Infrastructure Security Agency (CISA) said in an advisory in July 2020.
"An organization should determine its individual risk by assessing the likelihood that a threat actor will target its systems or data and the probability of the threat actor's success given current mitigations and controls."
