The anonymous "compliment" app Sarahah has become a social media popular among teenagers. As a growing trend, its reportedly to have security issues.
The problem happens on the web version of the Sarahah service, and not the mobile application.
Researcher Scott Helme described Sarahah's CSRF (cross-site request forgery) protections as "fairly trivial to bypass." CSRF is a dangerous form of attack that forces an end user to execute unwanted actions on a web application in which they're currently authenticated.
CSRF attacks specifically target state-changing requests. With it, an attacker may trick Sarahah users into executing actions of the attacker's choosing. A successful CSRF attack can force the user to perform state changing requests like transferring funds, changing their email address, and others. Stored XSS attacks can also be used to redirect users to other sites, which may contain malicious content, like viruses and spyware.
In this instance, Helme said that an attacker could exploit CSRF to force an account to favorite specific posts.
Helme discovered a security issues inside Sarahah's security headers. He said that this prevent the site from using the HSTS (HTTP Strict Transport Security) protocol, which is a tool to protect users from cookie hijacking and protocol downgrade attacks.
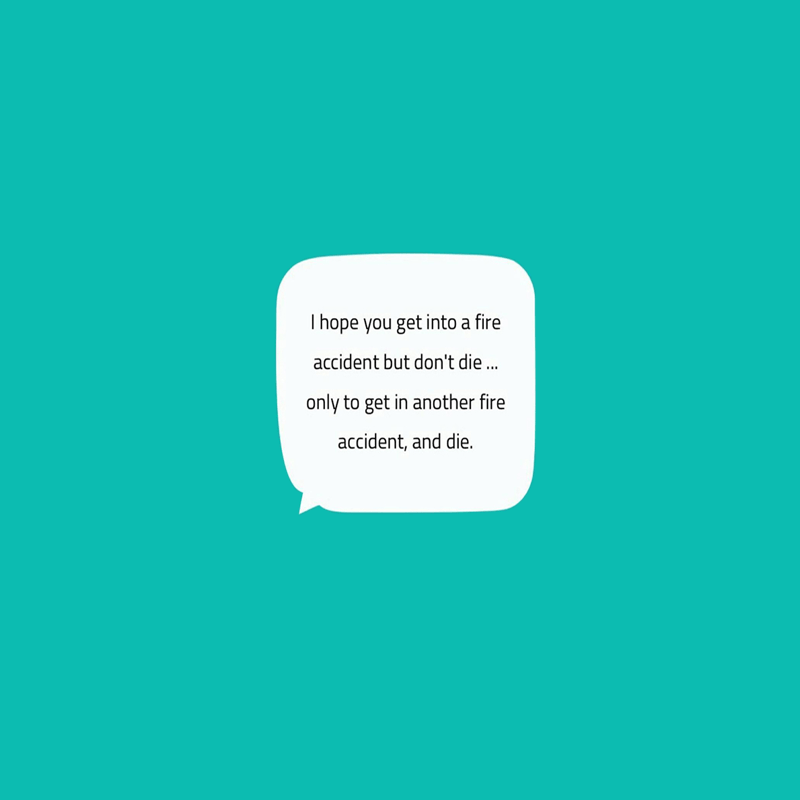
Sarahah has a filtering system, which discards posts depending on the words used. Pointed out by Helme, "I would kill for a cheeseburger right now" would be blocked because of the word kill. However, if a period is placed before “kill,” the post can be shared without issue.
Read: Meet Sarahah, The "Honest" App That Sparks Anonymous Messaging Controversies
A focus of Helme’s research is on how the Sarahah filters content and protects its users. Its biggest rival, Ask.fm, has been known to be a safe haven for online bullies. And here is wise for Sarahah to learn from its mistakes.
What's more, the word "script" is also on Sarahah’s filter. Although this is a way to nullify any XSS attacks, there are many ways to inject JavaScript without using even using the script tag.
Helme also discovered that Sarahah lacks rate limiting. This allows users to send messages at a bulk, thus creating spam. What this means, an online bully could bombard a victim with an infinite number of harassing messages, armed with just a basic script.
To make this worse, Sarahah also lacks a bulk delete function. This would force victims to read, or at least look at every harassing message they receive.
Helme didn't stop just there. He also raised concerns with how the Sarahah handles password resets, and brute-force login attempts.
To reset a password, Sarahah only requires the email address associated with the account. Then Sarahah will auto-generate a new password, and email it to the user. This again isn’t rate-limited. As a result, this would not only fill the victim's inbox, but it would also make it harder for them to log in to their account.
The issue also escalates when after ten login fails, Sarahah locks the account for an apparently-random period of time. By bombarding Sarahah with bad email-and-password combinations, an attacker can essentially prevent a user from gaining access to their account.

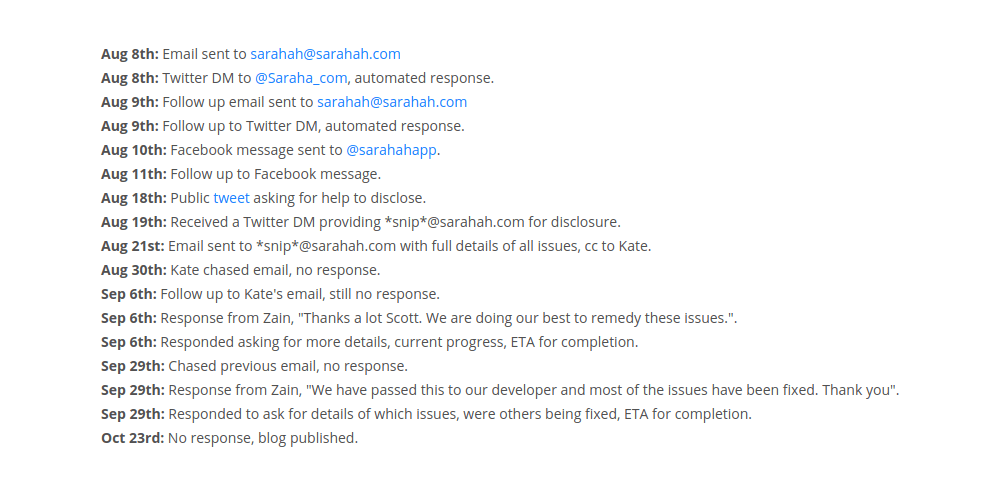
Helme first contacted Sarahah several months ago, in order to inform them about these issues. But with Sarahah haven't patch the problems, Helme disclosed his findings publicly on his blog.
He said that his biggest concern with the site is the lack of professionalism.
"Given what I’ve found and how the vendor responded, I really wouldn’t use the service myself. Sarahah have not done close to enough to prove that they are a responsible service provider worthy of me trusting them with my communications," he said.
"I’d like to see Sarahah provide information on how messages are protected during transmission and storage. A huge range of apps like WhatsApp, Facebook Messenger and Signal have put a massive focus on end-to-end (E2E) encryption and the privacy of their users, what steps are Sarahah taking? Can they read our messages? If they were breached could a hacker read our messages? Their lack of 2FA or 2SV is also an obvious opportunity for them to improve and better protect their users."
A few months ago, the service was caught uploading the entire contacts list of its users for a feature that didn't exist.
