
Distributed-denial-of-service (DDoS) is one of the most common and irritating cyberattack, and it's common for it to come with ransom demands. Usually sent via email, the attackers ask for payments in cryptocurrencies.
However, such demands are normally delivered after the attack has been launched. Here, internet security company Akamai noticed something unusual after analyzing separate DDoS attacks: buried inside the traffic that was meant to crash the servers are ransom notes.
"It’s actually like a DDoS attack with a phishing attack with an extortion attack all rolled into one," said Chad Seaman, a senior engineer with Akamai's security intelligence response team. "When we saw it we were like, huh, clever bastards."
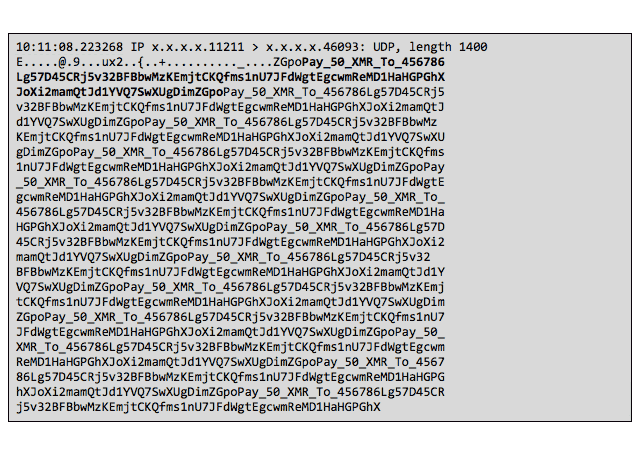
Akamai shared that inside the otherwise indecipherable string of code, the note reads: "Pay_50_XMR_To…," followed by a digital wallet address using a long alphanumeric string.
According to Akamai, the reason is because ransom notes that are sent via email, often go unseen due to spam protections.
Inserting the ransom note inside the DDoS code ensures that the target's security analysis will spot it when they investigate the attack data.
And the cryptocurrency Monero is chosen because it's more difficult to trace. While both Monero and Bitcoin use public ledgers to record and track transations, Monero ledgers hide the sender, recipient and the amount of each transaction.
Monero is more attractive to cyberattackers than a cryptocurrency like Bitcoin because it's more difficult to trace. While both rely on public ledgers for recording and tracking transactions, Monero ledgers hide the sender, recipient, and amount of each transaction.
"This is a first for us,” added Lisa Beegle, a senior manager for security intelligence at Akamai. "We’ve seen dozens upon dozens of extortion requests, but never in the payload itself, so to speak."
This advantage of Monero can allow the attackers to remain anonymous. However, the anonymity of the sender and transactions also prevent the recipient (the attacker) to know who has paid and who hasn't. This fact should discourage victims from ever paying up. Because if they do, there would be no guarantee that the attacker will know.
But in any ways, paying ransom is essentially never a good idea, no matter what method that attacker used. if word got out that someone has paid up, this will encourage more attackers to target it.
