
The web can be pretty scary. Hackers lurk to find weaknesses in systems and people's habits, and Mozilla knows that very well.
As the creator of Firefox, the popular web browser, Mozilla sees itself responsible in protecting its users from hacks. And in its continuous attempt to improve its browser, Mozilla has updated Firefox to version 95, to introduce a security technology that can help prevent zero-day attacks targeting its users.
The technology in question, is called the RLBox.
What it does, is allowing Firefox to take a more granular approach to sandboxing.
This technology allows Firefox to run the codes of websites users visit in a separate section of the browser's memory.
This way, Mozilla hopes that Firefox can contain malicious components, and prevent them from affecting the rest of the system.
In a blog post announcing the feature, Mozilla's engineer Bobby Holley explained the idea behind the technology.
Browsers like Firefox rely on third-party libraries to support different functionalities. These libraries are often written in low-level programming languages, like C, and, unfortunately, introducing vulnerabilities in C code is quite easy.
The problem here is that, traditional sandboxing technology, which isolates website's processes in individual sandboxes, has issues because it is vulnerable to chained attacks.
This is because malware developers can compromise the process first, and then escape the sandbox.
The method also limits the extent to which code can be separated into different sandboxed processes because of the memory overhead that is involved.
Mozilla wants to solve this using RLBox, which aims to protect users from inevitable vulnerabilities in these libraries and supply-chain attacks that exploit these libraries.
RLBox can do this because it has a different sandboxing approach.
Developed in conjunction with the University of California San Diego and the University of Texas, RLBox complements process-based isolation that compiles code as native code via WebAssembly.
Using this method, Firefox can effectively separate compiled pieces of native codes.
RLBox prevents websites users visit from accessing the system's memory outside of the region that have been specified. This should prevent any malicious codes from infecting the system by making some unexpected jumps.
Furthermore, RLBox also allows Firefox to run different pieces of trusted and untrusted code in the same process without them affecting each other.

At its core, the RLBox framework consists of two components.
The first is the sandboxing technique itself. which uses WebAssembly (Wasm). Specifically, RLBox compiles modules to WebAssembly and then compiles Wasm to native code using the fast and portable wasm2c compiler.
Wasm also makes it possible for RLBox to optimize calls into and out of sandboxed code into simple function calls.
And what makes RLBox particularly different than any other sandboxing techniques, is through its theoretical conditions called "zero-cost conditions."
Unlike other sandboxing techniques, RLBox does not require a glue code at the sandbox-application boundary to be secure.
It's the glue code that makes sandboxing error-prone and, in some cases, contributes to large performance overheads.
With RLBox, Mozilla uses the Wasm compiler to eliminate the needs of this glue code.
As a result, things become less complex with less overhead.
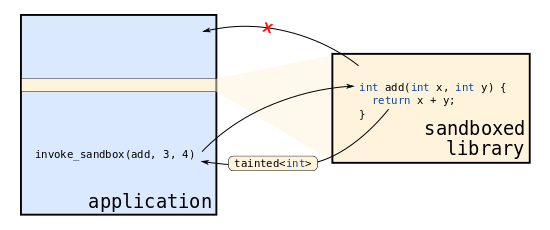
The second key component of RLBox is its tainted type system.
Firefox can prevent data that escapes the sandbox from becoming malicious, by marking all data that escapes by tainting them.
Mozilla's original work on RLBox was published in the proceedings of the USENIX Security Symposium in March 2021.
According to Holley:
RLBox started its life as a standalone project that Mozilla first trialed on macOS and Linux users in 2020.
Seeing the potential of the technology, Mozilla is releasing it across all Firefox platforms, including mobile systems.
As a start, Firefox is supporting RLBox for the browser's Graphite font rendering system, the Hunspell spell checker, and the Ogg multimedia container format. In the next version of the browser, Mozilla plans to add support for the Expat XML parser and Woff2, the font compression technology used in the browser.
"Going forward, we can treat these modules as untrusted code, and — assuming we did it right — even a zero-day vulnerability in any of them should pose no threat to Firefox," Holley said.
Firefox is a full-featured Web browser that offers a list of privacy and security features.
And with RLBox, Holley that acknowledges how the technology can help users, hoped that other browser makers would adopt the open-source technology.
To show how serious Mozilla is with this technology, the company has updated its bug bounty program so that researchers are paid for bypassing the sandbox even if there are no vulnerabilities in the isolated library. This should help Mozilla improve the browser’s security even further.
