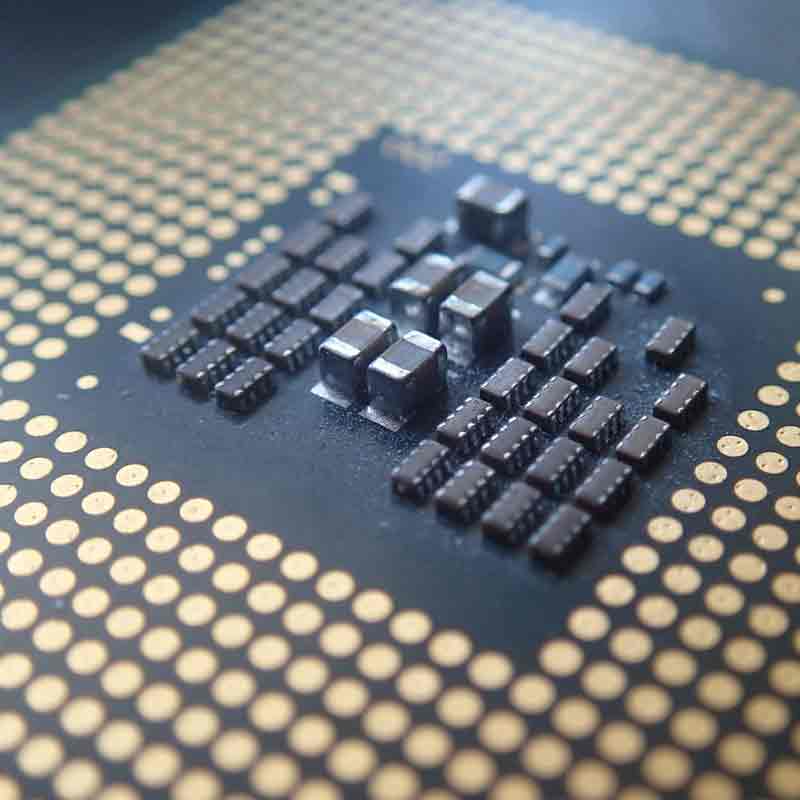
Intel said that it,Google Project Zero and Microsoft have jointly discovered another variant of a chip-based exploit.
The first variant which was revealed earlier in 2018, is the so-called Spectre and Meltdown exploits which pose vulnerability in chips used in hundreds of millions of computers and mobile devices. The newer variant discovered by Intel and others, is called "Variant 4."
It uses something called "Speculative Store Bypass," which could allow users' processor to load sensitive data to potentially insecure spaces. This is because the flaw uses "speculative execution, a feature common to most modern processor architectures, to potentially expose certain kinds of data through a side channel," said Intel on its statement.
The exploit that can be run through web browsers via runtimes like JavaScript, "could allow an attacker to read older memory values in a CPU’s stack or other memory locations."
Below is a video from Red Hat Videos explaining Speculative Store Bypass:
According to Intel, the company has never seen this exploit being used in the wild.
The company classifies Variant 4 as a medium risk because many of the exploits it uses in web browsers were fixed in the original set of patches, according to a blog post from the company.
Intel's executive vice president of security, Leslie Culbertson, said in a post that Intel has delivered microcode updates to cover Variant 4 to system manufacturers and software vendors. The update also includes a fix for Variant 3a (Rogue System Register Read), discovered by ARM in January.
She said that Intel doesn't expect the patch to affect computer performance at all, although she acknowledged that performance on the company's test system dropped at about 2-8 percent.
The fix from Intel is designed to be off by default, according to the company, and it'll be up to vendors to enable it.
Spectre and Meltdown have haunted companies like Intel, ARM and AMD, since they were first discovered. The flaw affected their produced chips, from computers to laptops and even mobile devices.
The vulnerabilities, which could allow attackers to read sensitive information on users' CPU, affected hundreds of millions of chips. While companies like Intel, Apple and Microsoft have issued updates to patch the flaws, the fixes haven't always worked as intended, sometimes causing computer problems.
The main reason is because some users are just too lazy to implement patches. One example was the WannaCry ransomware attack that took advantage of Windows computers whose owners never/rarely implemented a Microsoft update.
Before Variant 4, Spectre Next Generation (Spectre NG) was found. It had 8 variants which require their own patches in order to fix.
