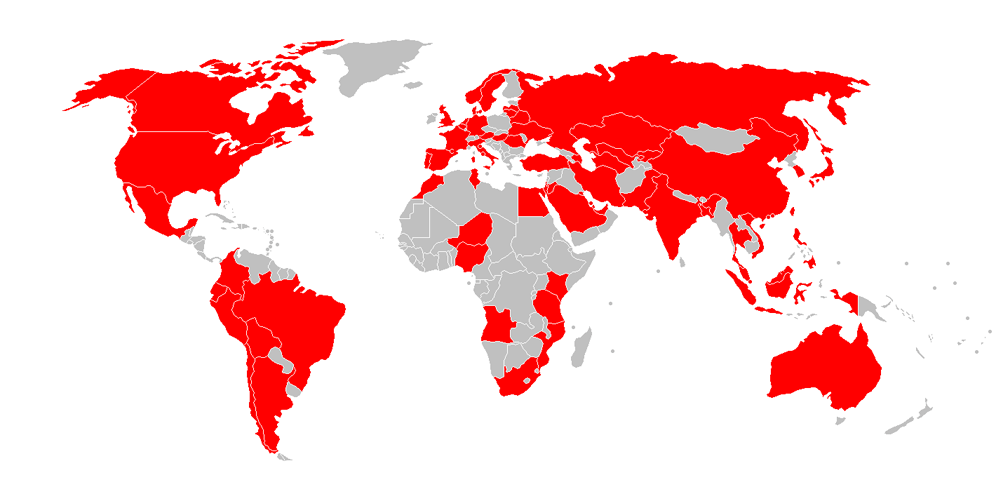
WannaCry is a ransomware program, also known as WannaCrypt, WanaCrypt0r 2.0, Wanna Decryptor and others similar. Targeting systems using Microsoft Windows, it has launched a massive cyber-attack, infecting hundreds of thousands of computers in more than a hundred countries.
It began its attack on Friday, infecting computers worldwide through email attachments. After infecting one computer, it infected all others in a local area network (LAN). The ransomware encrypts the infected computer's hard disk drive, then attempts to gain access so it can further spread on random computers connected to the internet via TCP port 445.
As a ransomware, WannaCry demands its victims ransom payments in bitcoins, ranging from $300 to $600.
Within days, WannaCry has infected systems from various companies as well as governments' entities.
They include: FedEx, National Health Service hospitals in the UK, Nissan Motor Manufacturing UK in Tyne and Wear, Renault, Russia's Ministry of Internal Affairs, Russian Railways and MegaFon, Romania's Ministry of Foreign Affairs, Telenor Hungary, German railway company Deutsche Bahn, Telefónica and several other large companies in Spain, several parts of the European Union, Brazil's São Paulo Court of Justice and Vivo, China's PetroChina and Public Security Bureaus, India's Andhra Pradesh Police, Indonesia's Dharmais and Harapan Kita hospital, and many others.
WannaCry is believed to have been developed using EternalBlue exploit, initially created by the NSA to attack computers using Microsoft Windows. EternalBlue was first released to public by a hacker group that goes with the name The Shadow Brokers on 14 April 2017, along with other tools.
Although there are patches to remove the vulnerabilities for supported systems, many fell as victims because many users haven't updated their systems yet. Users using older versions of Windows were also vulnerable because Microsoft lacks support for legacy products.
To deal with the unsupported Windows systems, Microsoft made updates to all versions of Windows, including Windows XP, Windows Server 2003 and Windows 8.
Days later, Marcus Hutchins was hailed as an "accidental hero" after he managed to intercept the spread of the malicious software. After discovering the "kill switch", the blogger was then reported to be working with the government’s National Cyber Security to help prevent future wave of attacks.
One year after the attack, a survey by Checkpoint revealed that only 3 percent of companies are prepared.
