Data is a commodity on the internet, and this is the main reason why people can go to great length to get their hands on them.
This is why security researchers and experts are always on the move to patch and secure whatever hackers can exploit and hack. And in one of the attempts to find exploits, researchers found a vulnerability in Transport Layer Security (TLS) protocol that could potentially allow devastating exploits to happen.
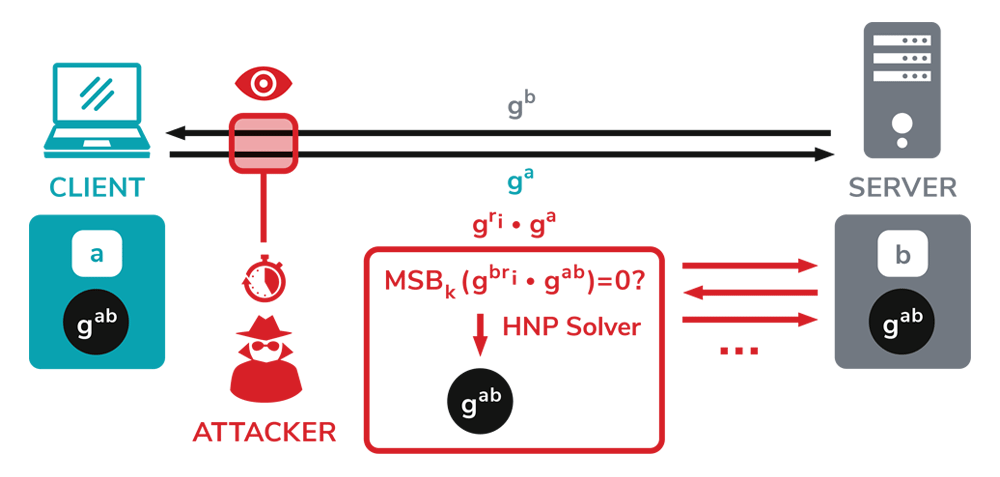
Security researchers found that all servers that use the Diffie-Hellman key exchange and TLS (Transport Layer Security) 1.2 and below are vulnerable to attacks.
DTLS is also impacted. TLS 1.3 however, is considered safe.
Under certain conditions, hackers can break the encryption and read sensitive communications happening inside it.
The researchers call this bug, the "Raccoon Attack".
Fortunately, Raccoon Attack is a server-side attack only, meaning that it cannot be performed on a client, such as browsers. The attack also needs to be executed for each client-server connection in part, and cannot be used to recover the server's private key and decrypt all connections at once.
Despite having the capability to decrypt TLS sessions and read sensitive communications, the researchers said that the Raccoon Attack is extremely hard to execute.
For starters, hackers are required to have certain and extremely conditions to meet.
"The vulnerability is really hard to exploit and relies on very precise timing measurements and on a specific server configuration to be exploitable," researchers said. "[The attacker] needs to be close to the target server to perform high precision timing measurements. He needs the victim connection to use DH(E) and the server to reuse ephemeral keys. And finally, the attacker needs to observe the original connection.
"For a real attacker, this is a lot to ask for," academics said.
In other words, Raccoon Attack is not practical.
This is why in real-world scenarios, hackers would likely use other attack vendors that are more simpler and reliable that this Raccoon Attack.
But still, in comparison to what hackers would have to do to break modern cryptography like AES, the Raccoon Attack does not look complex anymore.
While the attack has been deemed hard to exploit, some have played their parts and released patches. Microsoft (CVE-2020-1596), Mozilla, OpenSSL (CVE-2020-1968), and F5 Networks (CVE-2020-5929) have all released security patches to thwart the attack by addressing the concern with ephemeral key reuse.
And for its part, Mozilla has turned off DH and DHE cipher suites in its Firefox browser. Microsoft on the hand, offers customers advise to disable TLS_DHE.
"Our attack exploits the fact that servers may reuse the secret DH exponent for many sessions, thus forgoing forward secrecy," the researchers concluded.
"In this context, Raccoon teaches a lesson for protocol security: For protocols where some cryptographic secrets can be continuously queried by one of the parties, the attack surface is made broader. The Raccoon attack showed that we should be careful when giving attackers access to such queries."
