A database is an organized collection of structured information. On the web, they are often connected to one or more servers via a high-speed channel, so they can be used in large volume transaction processing environments.
And this time, about 235 million social media users from Instagram, TikTok, and YouTube were exposed due to a database being online without any password protection.
The entries inside the database were compiled by a technique called web scraping. It involves a company that gathers data from the web through an automated manner.
Many social media networks prohibit web scraping practices, and it seemed that there are entities who still practice this method for their own benefit.
The scraped data had four major datasets with details of millions of users from the aforementioned platforms.
In a report, Bob Diachenko, the lead researcher for security firm Comparitech, found three identical copies of the database on August 1.
Diachenko who previously uncovered a database containing scraped information of 267 million Facebook users in 2019, said that the data belonged to a now-defunct company called Deep Social.
Deep Social went out of business in 2018 after Facebook reportedly banned it from its marketing API and threatened legal action.
When Diachenko and his team reached out to the company, their request was forwarded to the Hong-Kong-based firm Social Data.
Social Data was founded in 2019, according to Hong Kong business directories. Its website says it “helps your business to find Influencers and get in-depth insights into demographic and psychographic data of influencers and their audience throughout different types of social media on the web.”
Acknowledging the breach, the company quickly worked to close the access to the database. However, Social Data denied having any links with Deep Social.
In a statement, Social Data’s spokesperson said that all the data collected to populate the database was public, meaning that it wasn’t collected suspiciously:
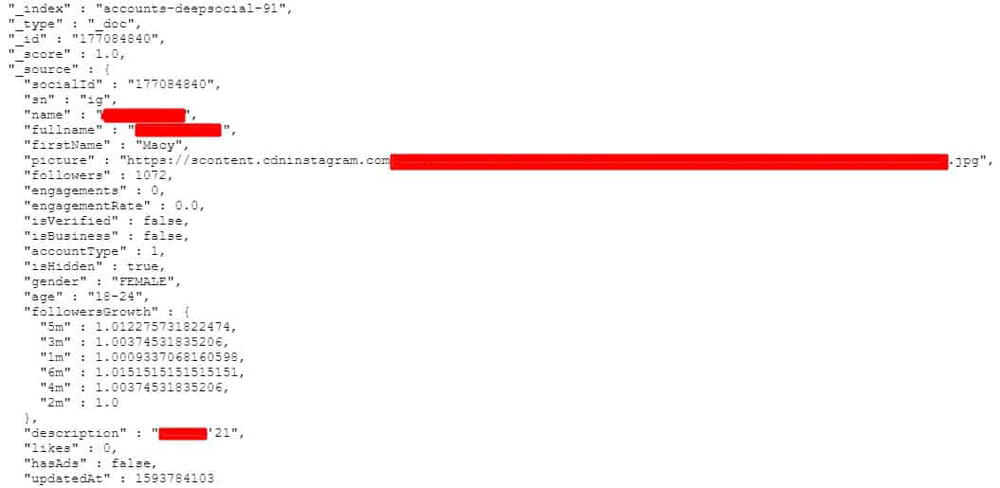
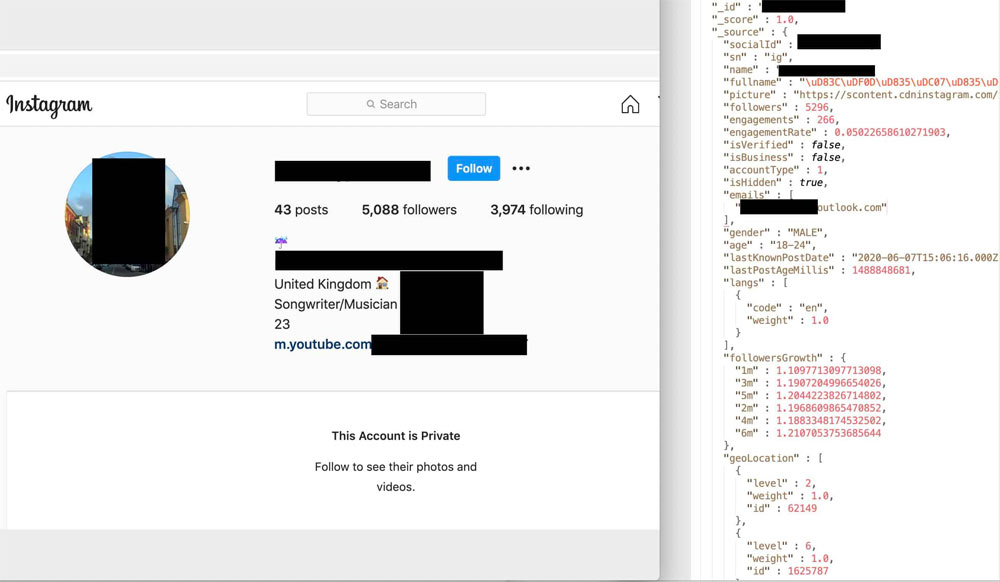
Here is a breakdown of the data contained in the database leak:
- Profile name.
- Full real name.
- Profile photo.
- Account description.
- Whether the profile belongs to a business or has advertisements.
- Statistics about follower engagement, including:
- Number of followers.
- Engagement rate.
- Follower growth rate.
- Audience gender.
- Audience age.
- Audience location.
- Likes.
- Last post timestamp.
- Age.
- Gender.
