Malvertising is the practice of delivering malicious online advertisements that are either disruptive or intrusive. And on Google Chrome, many extensions were doing this.
In a report by security researcher Jamila Kaya and Cisco's Duo Security team, they have identified a group of Chrome web browser extensions that were active over at least eight months.
The rogue extensions were part of a larger malware operation that has been active for at least two years, with the team also believing that the group who orchestrated this operation might have been active since the early 2010s.
During that time period, the extensions redirected millions of users to malicious sites, including to affiliate links or a GDPR announcement site in an apparent attempt to misdirect investigations and appear legitimate.
Users were redirected in such a way so that the malicious ads appear ordinary, but remain intrusive.
In their two-months long investigation, the researchers found more than 500 of these extension.
According to Jamila Kaya and Jacob Rickerd from Duo:
The malicious code injected by the extensions can be activated under certain conditions.
When the conditions meet, the extensions can redirect users to specific sites, with some would be an affiliate link on legitimate site, or something malicious, such as a malware download site or a web page solely created for phishing.
Kaya discovered the malicious extensions during her routine threat hunting, in which she gathers visiting data to malicious sites that had a common URL pattern.

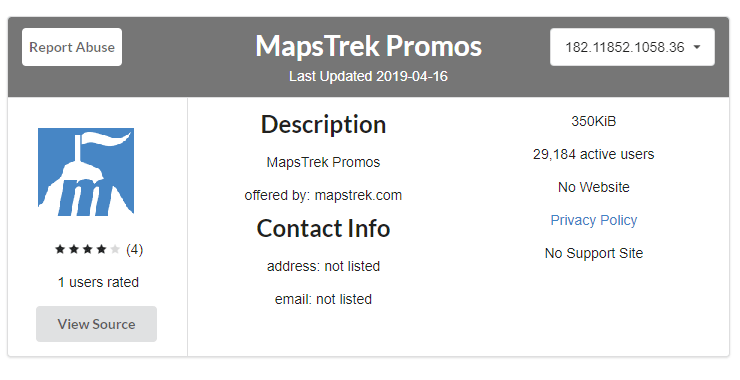
Kaya discovered that the rogue extensions had little information about their true purpose, and all shared much the same source code.
However, their function names were replaced in order to appear different enough to pass through Google’s automated duplicate detection system.
This way, the developers of the extensions can publish a large volume of the rogue extensions which do the exact same thing, if not similar.
"Individually, I identified more than a dozen extensions that shared a pattern. Upon contacting Duo, we were able to quickly fingerprint them using 'CRXcavator' database and discover the entire network," she said.
After reaching Google, the tech giant conducted its own investigation. Here, Google found even more extensions that shared the same pattern. Google quickly made all those rogue extensions disabled by default, and marking them as malware so users who have installed them would be prompted to immediately uninstall them.
Google also removed the 500+ Chrome rogue extensions from its official Web Store.
