
Antivirus solutions are meant to be placed at the forefront to protect users from any potential digital harm. But what would happen if that solution is flawed?
As experienced by Czech antivirus maker Avast, the company was forced to take a drastic measure by disabling a major component of its antivirus product after a Google security researcher found a dangerous vulnerability that put all of the its product's users at risk.
The security flaw was found in Avast's JavaScript engine, a component of the Avast antivirus that analyzes JavaScript code for malware before allowing it to execute in browsers or email clients.
Tavis Ormandy, a security researcher at Google said that:
"Any vulnerabilities in this process are critical, and easily accessible to remote attackers."
With the flaw, hackers can simply send targets with a malicious a JavaScript file or a Windows Script Host file via email, or tricking a user into accessing a specially crafted file with malicious code.
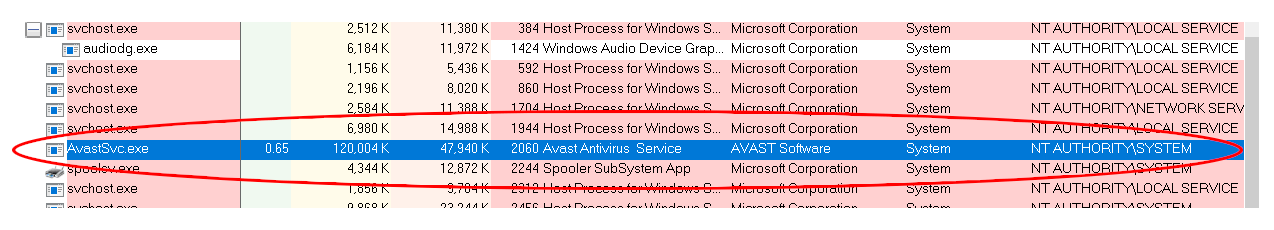
Ormandy explained just how serious the security flaw is, saying that most antivirus software has system level access. What this means, when Avast downloads and scans the files and runs them in its custom engine, the malicious operation of the files could be executed on victims' machine, also with system-level access.
In other words, the bug could allow hackers to install malware on Avast users' device, or do more sinister operations.
After Ormandy notified Avast for about two weeks, the company said that it had yet to patch the bug.
The company decided to instead disable its antivirus' JavaScript scanning feature until a patch is ready.
The Czech company explained in a statement about its decision:
"On March 9, he released a tool to greatly simplify vulnerability analysis in the emulator."
"We have fixed this by disabling the emulator, to ensure our hundreds of millions of users are protected from any attacks. This won't affect the functionality of our AV product, which is based on multiple security layers."
Because Avast couldn't patch the issue as fast as it comes to light, the company decided to just disable the feature to ensure that no users would fall as victims.
Ormandy discovered the Avast antivirus bug using a tool he developed in 2017 that allows him to port Windows DLL files to Linux. Ormandy also released another tool called 'Avast Antivirus JavaScript Interpreter' that he used to analyze the antivirus for the bug.
