No product is perfect, simply because humans that created the product, are not flawless.
The same goes to software. In this case, imperfection in the codes can lead to bugs or vulnerabilities. And according to GitHub's 2020 Octoverse report, it can take an average of over four years for them in open source software to be spotted.
The popular open-source repository said that the reliance of people and companies on open source projects, components, and libraries is more common than ever.
In comparison to 2019, GitHub at this time found that 94% of projects rely on open source components, with close to 700 dependencies on average. Most frequently, open source dependencies are found in JavaScript, as well as Ruby and .NET.
Over the course of 2020, GitHub saw more than 56 million developers on the platform, with over 60 million new repositories being created - and over 1.9 billion contributions added - over the course of the year.
Knowing this, the four years time to identify a bug is certainly an area in the security community that needs to be addressed.
In the report, GitHub said that:
"You would be hard-pressed to find a scenario where your data does not pass through at least one open source component. Many of the services and technology we all rely on, from banking to healthcare, also rely on open source software."
"The artifacts of open source code serve as critical infrastructure for much of the global economy, making the security of open source software mission-critical to the world."
GitHub launched a research into the state of open source security, comparing information gathered from the organization's dependency security features and the six package ecosystems supported on the platform spanning from October 1, 2019, to September 30, 2020, and October 1, 2018, to September 30, 2019.
Only active repositories have been included, not including forks or 'spam' projects. The package ecosystems GitHub analyzed in its research include Composer, Maven, npm, NuGet, PyPi, and RubyGems.
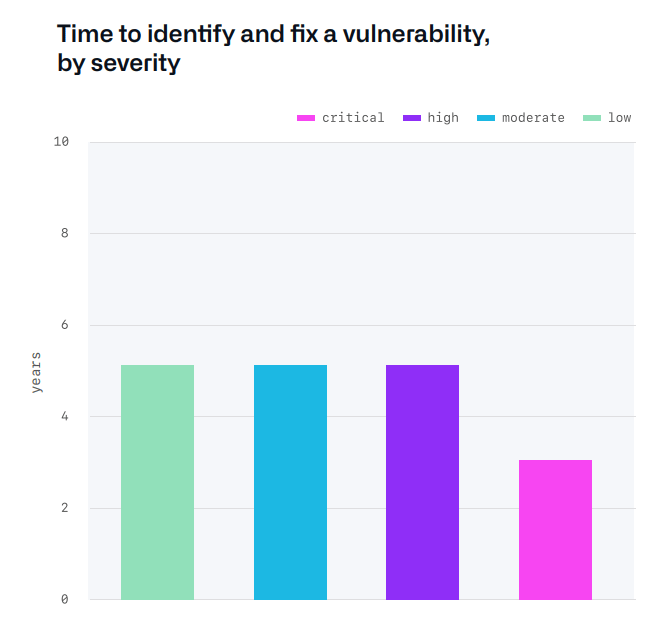
GitHub suggest the the importance of focusing efforts on time to detect, knowing that there are likely a large number of undiscovered vulnerabilities in the open source software available in the market. Here, the community must try to increase the rate of discovery, beyond the rate of bug introduction.
GitHub also said that project developers, maintainers, and users should check their dependencies for vulnerabilities on a regular basis and should consider implementing automated alerts to remedy security issues in a more efficient way.
"Open source is critical infrastructure, and we should all contribute to the security of open source software," the organization added. "Using automated alerting and patching tools to secure software quickly means attack surfaces are evolving, making it harder for attackers to exploit."
It should be noted though, that the majority of bugs in open source software are not malicious.
83% of the CVE alerts issued by GitHub have been caused by mistakes and human error, although malicious actors can still take advantage of them for malicious purposes. In total, 17% of vulnerabilities are considered malicious, but these triggered only account to 0.2% of alerts, as they are most often found in abandoned or rarely-used packages.
The open source community is already playing a key role in the development of software. But because no software is perfect, there can be flaws waiting to be discovered.
Because this fact will continue to exist, the only way to make sure that software has the least amount of bugs, people should find them faster than introducing them.
