
Keyboard apps are incredibly useful tools on smartphones and tablets. But there are challenges.
For Chinese, typing using the logographic language is more difficult than typing alphabetic languages, where each letter can be represented by one key. This happens because there are tens of thousands of characters in Chinese in total.
While the exact number of characters in Chinese is difficult to determine precisely due to various factors such as historical usage, regional variations, and the ongoing creation of new characters, estimates typically range from around 50,000 to 100,000 characters in total.
For everyday reading and writing, knowledge of approximately 3,000 to 5,000 characters is considered sufficient for functional literacy.
This number is still way too big for a single keyboard.
But thanks to technology, developers have made typing in Chinese possible.
Through modern Chinese input methods and dictionaries, which also rely on a smaller subset of characters for practical use, the most popular method is through the “Input Method Editor” (IME), which offer a variety of approaches to inputting Chinese characters, including via handwriting, voice, and optical character recognition.
And the most popular IME method, being used by some 76% of mainland Chinese keyboard users, is the pinyin method, which is based on the pinyin romanization of Chinese characters.
This is where researchers found a big issue.
Keyboard apps using IME that offer pinyin input are popular because they have accommodate the challenge of allowing users to type Chinese characters quickly and easily.
While many keyboard apps operate locally, solely within a user’s device, IME-based keyboard apps often have cloud features which enhance their functionality.
This is a huge advantage.
By allowing the keyboards to connect to the clouds, they can remove the complexities of predicting which characters a user may want to type next.
But this is also a huge disadvantage because the cloud-based feature means that the apps must send whatever users typed to the internet.
While the content of what users type is traveling from their device to the cloud, it is additionally vulnerable to network attackers if not properly secured, things are more concerning than that.
An investigation by Citizen Lab found significant security vulnerabilities across popular Chinese keyboard apps, affecting potentially billions of users.
The bug, identified in cloud-based pinyin keyboard apps, is found on keyboards apps from 9 vendors.
They include: Baidu, Honor, Huawei, iFlytek, OPPO, Samsung, Tencent, Vivo, and Xiaomi.
"Our analysis revealed critical vulnerabilities in keyboard apps from eight out of the nine vendors — all but Huawei — in which we could exploit that vulnerability to completely reveal the contents of users’ keystrokes in transit," the researchers said on their post.
The bug allows malicious actors to hack into devices and user accounts, by intercepting user data transmitted between devices and the cloud.
By intercepting the keystrokes while they are in transit, hackers could compromise sensitive information, ranging from text messages to financial details.
The implications of these studies are profound, since the bug could have impacted hundreds of millions of users, particularly given the widespread adoption of Honor, OPPO, and Xiaomi smartphones in China and its neighboring countries.
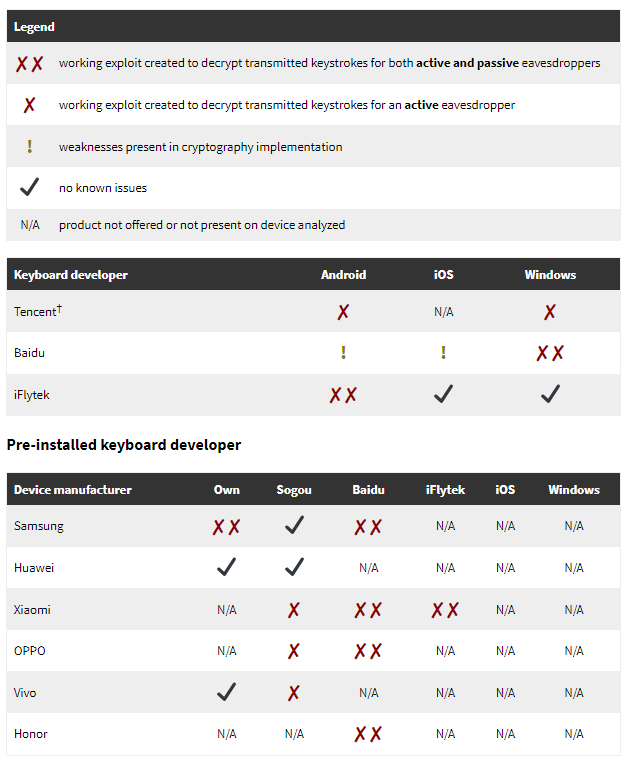
When Citizen Lab promptly notified all affected vendors of the vulnerabilities, all responded by patching their respective keyboard apps.
Tencent and Honor failed to address the issues by the specified deadline.
"Given the scope of these vulnerabilities, the sensitivity of what users type on their devices, the ease with which these vulnerabilities may have been discovered, and that the Five Eyes have previously exploited similar vulnerabilities in Chinese apps for surveillance, it is possible that such users' keystrokes may have also been under mass surveillance," the researchers concluded.
As for Apple and Google, neither of their keyboard apps transmit keystrokes to cloud servers for cloud-based communications, which should make it impossible to analyze the keyboards for the security of the feature.
"However, we observed that none of the mobile devices that we analyzed included Google’s keyboard, Gboard, preinstalled, either," the researchers claim.
