
Modern browsers are built with capabilities and features that should meet the requirements of most users. But some may find this insufficient.
This is why creators of most modern and popular browsers allow users to customize, or enhance the capabilities of their browsers by installing plugins, or extensions, or add-ons. Through these, users can equip their browsers with the necessities they need to browse the web to their likings.
However, given that browser extensions have deep integrity with the browser they are installed on, some can exploit its weaknesses and become malicious.
And in this case, two Firefox add-ons were found to have misused the Proxy API to impede downloading of updates to the browser.
According to Mozilla, the malicious extensions in question, are 'Bypass' and 'Bypass XM'.
The two malicious Firefox add-ons that were installed by 455,000 users, "interfered with Firefox in a way that prevented users who had installed them from downloading updates, accessing updated blocklists, and updating remotely configured content," said Mozilla's in a blog post.
This happened because the two extensions abused the Proxy API, which is used to proxy web requests.
Abusing this API allowed the authors of the extensions to control the manner Firefox browser connects to the internet effectively.
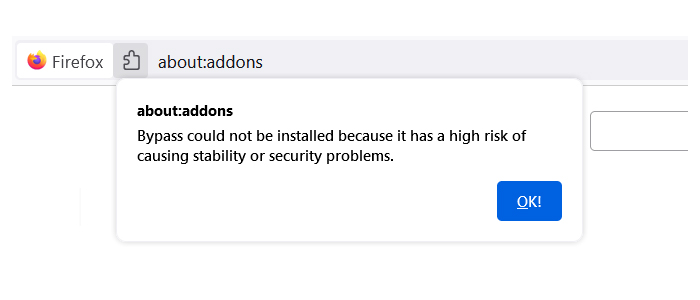
To prevent more users getting their Firefox browser infected by this malicious extensions, Mozilla said that it is blocking the extensions from being installed by other users, and said that it is pausing on approvals of all new add-ons that use the Proxy API until fixes are broadly available.
Developers of add-ons that require the use of this proxy API, are required to start including a strict_min_version key in their manifest.json files targeting Firefox browser versions 91.1 or above.
And for those users who have installed either or both extensions, they are urged to remove them immediately.
They can do this by heading the 'Add-ons' section and explicitly searching for "Bypass" (ID: 7c3a8b88-4dc9-4487-b7f9-736b5f38b957) or "Bypass XM" (ID: d61552ef-e2a6-4fb5-bf67-8990f0014957).
The presence of either or both of these entries indicates that the browser is affected.
After removing the extensions, Mozilla urges affected users to update their Firefox browser.
Users should also consider refreshing Firefox and resetting all add-ons, advised Mozilla, or start from scratch by downloading and installing a new copy of Firefox.
For users of the two troubling extensions, the California-based non-profit said that it has deployed a system add-on named "Proxy Failover."
"Starting with Firefox 91.1, Firefox now includes changes to fall back to direct connections when Firefox makes an important request (such as those for updates) via a proxy configuration that fails. Ensuring these requests are completed successfully helps us deliver the latest important updates and protections to our users," said Mozilla.
"We also deployed a system add-on named 'Proxy Failover' (ID: [email protected]) with additional mitigations that has been shipped to both current and older Firefox versions."
"Add-ons are a powerful way to extend and customize Firefox. At Mozilla, we are committed not only to supporting WebExtensions APIs, but also ensuring the safety and reliability of the ecosystem for the long term," said Mozilla.
"We take user security very seriously at Mozilla. Our add-on submission process includes automated and manual reviews that we continue to evolve and improve in order to protect Firefox users.
It should be noted that Mozilla didn't share if the two add-ons were doing anything else malicious in the background, but reports suggest that they likely were using a reverse proxy to bypass paywalled sites.
