
There was a time when securing an online account using username-password combination was enough. But long gone are those days.
Tech companies have urged people to use multi-factor authentication (MFA). This way, users can be granted access only after successfully presenting two or more pieces of evidence to an authentication mechanism: knowledge, possession, and inherence.
But according to Alex Weinert, Director of Identity Security at Microsoft. MFA methods like one-time codes sent through SMS and voice calls aren't at all secured.
This is why he urges people to abandon the methods, and instead use newer forms of MFA technologies, like app-based authenticators and security keys.
Back in 2019 in a blog post, Weinert has explained why "password doesn't matter.
This time in another blog post, Weinert said that "[SMS and voice-based MFA] mechanisms are based on publicly switched telephone networks (PSTN), and I believe they’re the least secure of the MFA methods available today."
It's time time to move on from publicly switched networks for authentication - https://t.co/ZVVtTl16is
— Alex Weinert (@Alex_T_Weinert) November 10, 2020
In 2019, Weinert said that users who enabled MFA ended up blocking around 99.9% of automated attacks against their Microsoft accounts. But in 2020, he said that if users have to choose between multiple MFA solutions, they should stay away from telephone-based MFA.
The issue comes from the state of the telephone network that isn't built with security in mind.
Weinert said that both SMS and voice calls are transmitted in cleartext, meaning that hackers can easily intercept the data. This can be done using methods and tools like software-defined-radios, FEMTO cells, or SS7 intercept services.
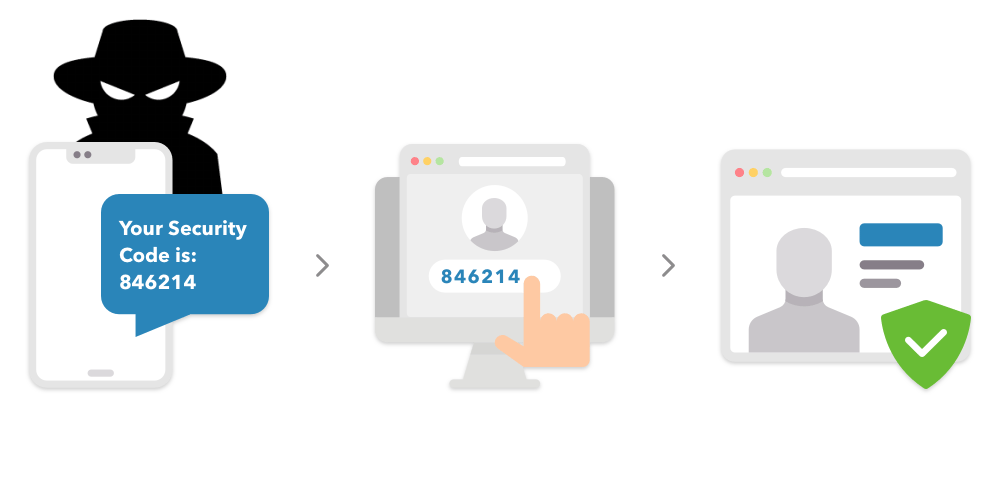
He added that SMS-based one-time codes are also phishable via open source and readily-available phishing tools like Modlishka, CredSniper, or Evilginx.
What's more, the MFA methods are prone for social engineering attacks, where phone network employees can be tricked into transferring phone numbers to a threat actor's SIM card, in a strategy known as SIM swapping, where hackers pose as the legitimate owner of a SIM, allowing the hackers to receive MFA one-time codes on behalf of their victims.
"Sadly, customer support agents are vulnerable to charm, coercion, bribery, or extortion," said Weinert.
One famous example of this kind of hack, happened when founder and CEO of Twitter Jack Dorsey had his account hacked.
And making things worse, phone networks are also exposed to changing regulations, downtimes, and performance issues, all of which impact the availability of the MFA mechanism.
Weinert believes that the issues "will only widen" in the future
This can be a problem in a world where people are increasingly reliant on MFA to secure their accounts.
Because SMS and voice-based MFA methods have the weakest security, the methods are naturally becoming hackers' primary target due to its large adoption.
Weinert urges people to not use SMS and voice-based MFA methods, and instead enable a stronger MFA mechanism for their accounts.
But if users want the very best in the industry, they should use hardware security keys as their second authentication method, which Weinert ranked as the best MFA solution.
Further reading: 99.9% Of Compromised Microsoft Accounts Didn't Use Multi-Factor Authentication
