There are millions of websites and web applications out there on the web, and many of them are hacked once or a few times during their lifetime.
As a result of this, usernames and passwords for over 15 billion accounts, including network administrator accounts, bank accounts and streaming services are being traded online in underground forums or pasted to the open web.
That according to researchers from cybersecurity firm Digital Shadows.
Coming from 100,000-plus discrete breaches, that number is up 300% since 2018.
It's also roughly more than three times the population of the internet.
To come up with that number, the researchers spent 18 months analyzing how hackers gained access to and use stolen account details for their own benefits. In their report, the researchers have also detailed how account takeover has never been easier or cheaper for cybercriminals.
The report said that:
- 5 billion of those are “unique”, without any repeated credential pairs.
- Most credentials belong to consumers, and cybercriminals give away many for free; those that are sold go for an average of $15.43.
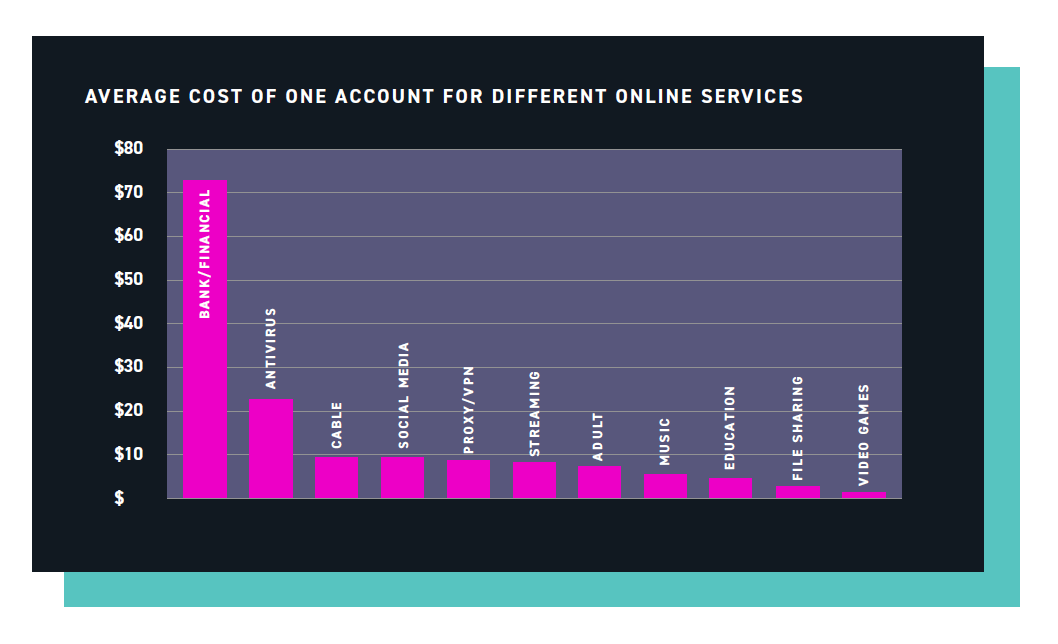
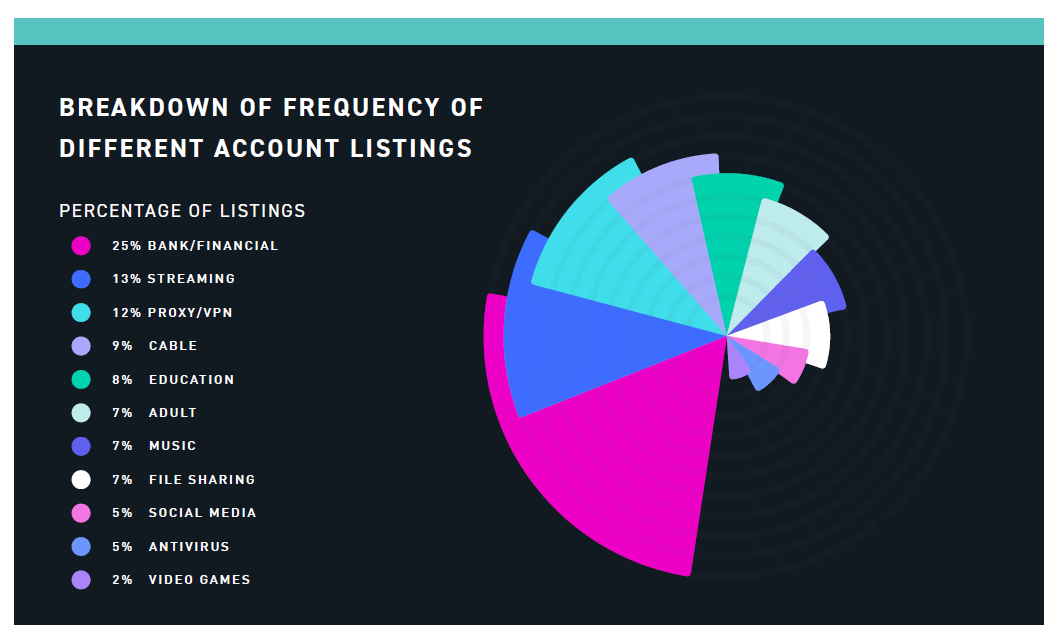
- 25% of all the accounts for sale, are bank and related to financial data. They sell for an average of $70.91 apiece.
- The second most expensive accounts for sale, are related to accesses to antivirus programs. They sell at around $21.67 each.
- Accounts for media streaming, social media, file sharing, virtual private networks (VPNs), and adult-content sites all trade for $10.
- Access to organizations’ key systems is for sale at premium price and through auction. They are sold to the highest bidder, to up to $140,000 (with an average of $3,139).
- Email addresses with "invoice" and "invoices" were the most commonly advertised.
Methods of attacks, according to the researchers, include: using brute-force cracking tools and account checkers, ATO “as-a-service”, sentry MBA as the most popular credential stuffing tool, and the OpenBullet tool as one of the most popular in 2020 having being used in 35% of the cases.
Many breached accounts are shared multiple times. What this means, users must have been unaware of what has happened.
The researchers warned that the reason why so many compromised account credentials are available for sale online - be they administrator passwords, bank details or a login for social media networks – is because people are using weak passwords which can easily be cracked with the aforementioned tools.
"These attacks are typically automated login attempts that use a predetermined list of access credentials—often, combinations of usernames or email addresses and plaintext passwords—sourced from previous data breaches or leaks," said Alex Guirakhoo, the leader of the research team at Digital Shadows.
"Credential stuffing tools are inexpensive to purchase and use, even offering some level of automation to make gaining account access a trivial task," he added.
In order to prevent hackers from compromising accounts, the researchers suggested that users use unique password for each service, use password manager, and apply multi-factor authentication for an extra layer of protection.
But still, with more than 15 billion accounts already compromised, it's highly possible that anyone could be among them.
"If you suspect your account has been compromised, you should immediately change your passwords - and for any other services where you have used the same password - and check for any fraudulent activity. This is where unique passwords come in handy," said Guirakhoo.
