The internet is made from many programming languages, working in tandem, creating a network that consists of many other networks.
And Java is among the most popular programming languages in the world due to the fact that it is so platform independence.
This makes Java compatible with most types of computers from PCs running Windows to Mac computers, to Unix or Linux computers, as well as mainframe computers, mobile devices, IoT devices, and more
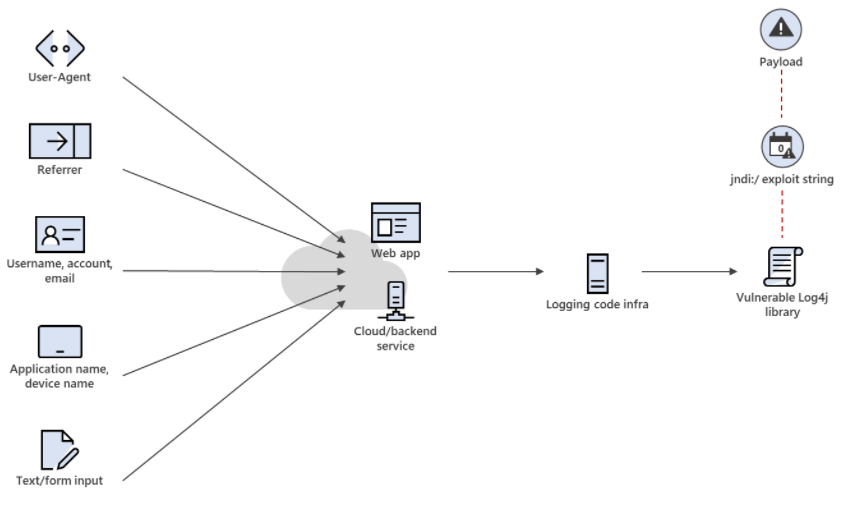
This time, a bug called 'Log4j' was found, and it made the internet scrambled for a fix.
The vulnerability first became publicly known when a security researcher shared a proof-of-concept exploit of the bug on Twitter through a then-deleted tweet.
The bug is then tracked as CVE-2021-44228, classed as severe with CVSS score of 10, the highest possible severity rating.

The Log4j is a logging tool meant for developers.
The tool however has a bug, and this bug was first found on Minecraft, which is Microsoft's. But several security vendors and threat researchers noted that Log4j 2 is not only used on Minecraft, as it is used by most Java-powered apps, including those developed and used by major cloud services, applications and PC games, Amazon AWS, Apple's iCloud, Baidu, Cloudflare, ElasticSearch, LinkedIn, QQ, Tencent, Tesla, Twitter and many more.
In its advisory, as of Log4j 2.0.15 (released on December 6th), the vulnerable configurations have been disabled by default.
Apache has detailed the flaw on its Log4j2 vulnerabilities page, and credited Chen Zhaojun from Alibaba Cloud Security Team.
Minecraft has published an advisory that said the company had addressed the Log4j 2 vulnerability, but urged players and Minecraft server hosts to take additional steps to protect themselves.
CERT NZ (New Zealand’s national Computer Emergency Response Team) has issued its own security advisory warning concerning the issue.
Additionally, the Cybersecurity and Infrastructure Security Agency (CISA) has also released an advisory to encourage users and administrators to apply the appropriate mitigations.
Even NSA has something to say about it.
"The log4j vulnerability is a significant threat for exploitation due to the widespread inclusion in software frameworks, even NSA’s GHIDRA," tweeted NSA cybersecurity director Rob Joyce, referring to an NSA open-source software project.
Security company Cloudflare determined the log4j bug was "so bad" that CEO Matthew Prince said the company is rolling out protections to all Cloudflare users by default. "But, no matter what we are able to do, we will not be able to fully protect against all exploits of #Log4J because there are so many ways things can get logged," Prince tweeted.
"Critical to patch your Log4J systems," he said.
When the news first came out, Cloudflare on its blog post said that no cases have been found on its system.
Microsoft has also released its own response, Cisco released its advisory, and so did the Swiss government in an advisory.
It is said that Log4j, which is also referred to as the Log4Shell bug, rivals Heartbleed in its severity.
Not only because of the potential damage it holds, as the bug is also relatively easy to exploit.
The bug was first reported by Alibaba Cloud's security team to Apache on November 24.
It is also revealed that CVE-2021-44228 impacts default configurations of multiple Apache frameworks, including Apache Struts2, Apache Solr, Apache Druid, Apache Flink, and others.
After the first proof-of-concept exploit was published on GitHub yesterday, threat actors began scanning the internet for systems using older versions of Log4j.
Malicious actors are trying to exploit as many as they can, before those systems can patch the bug.
Among others affected, cases include hackers planting malware on systems powered by older versions of the Log4j
On Monday, Check Point reported that Log4Shell’s new, malignant offspring can now be exploited “either over HTTP or HTTPS (the encrypted version of browsing),” they said.
While the patch has been released, malicious actors have "mutated" the flaw, and managed to create some that slip past the new protections.
Because of the enormous attack surface it poses, some security experts are calling Log4Shell the biggest cybersecurity issue in 2021.
Further reading: The 'Log4j' Bug, And How It Affects Software From Minecraft To Apple And Beyond
