Not anymore that espionage involve someone traveling halfway across the world to get behind enemy lines in order to obtain secrets or confidential information without the permission of the holders of the information.
With the internet, a person can thousands of miles away, but can still steal information without having to be in harms way.
And this time, the U.S. Department of Justice announced charges against five Chinese nationals and two Malaysians who ran global hacking operations for at least six years. The federal executive department accused the hackers for hacking computers owned by hundreds of companies and organizations around the world, to steal identities, plant ransomware, and spy on Hong Kong activists.
They are also accused for hacking major gaming companies to steal their secrets, as well as obtaining "gaming artifacts" like tradable in-game items and credits, so they can sell them.
Three of the Chinese suspects operated out of Chengdu 404 Network Technology, a Sichuan-based company that purported offer network security services for other businesses.
Together, the seven hackers were long recognized by cybersecurity experts as the "APT41" hacking organization, identified by their shared tools and techniques.
Also known as 'Barium,' 'Winnti, 'Wicked Panda,' and 'Wicked Spider,' the hacking group is said to be Chinese state-sponsored, and specializes in software supply-chain attacks, stealing source codes of software, stealing identities, as well as valuable information from companies.
The hacking group is also said to run crypto-jacking malware to monetize their efforts.
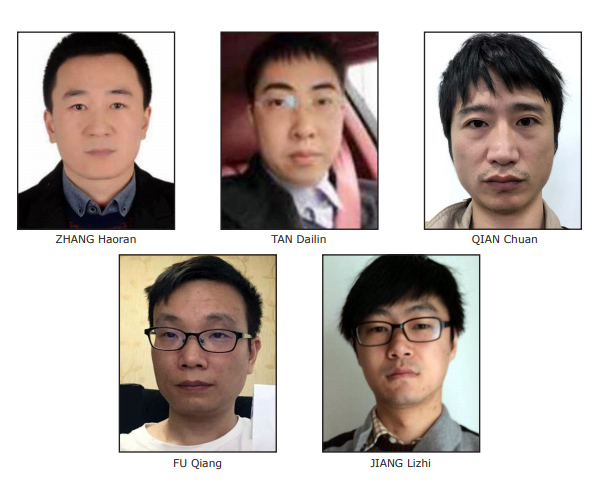
In a press release published by the U.S. Justice Department, it was revealed that two of the five hackers: Zhang Haoran (张浩然) and Tan Dailin (谭戴林), were charged back in August 2019.
The remaining three: Jiang Lizhi (蒋立志), Qian Chuan (钱川) and Fu Qiang (付强), and the two Malaysian co-conspirators: Wong Ong Hua and Ling Yang Ching. were charged in separate indictments in August 2020.
According to court filings, Jiang Lizhi once boasted to a colleague in 2012 that he was protected by China's Ministry of State Security, and said that they were protected if they did not hack domestically.
"Some of these criminal actors believed their association with the PRC provided them free license to hack and steal across the globe," said federal prosecutor Michael Sherwin said in a statement.
The FBI on its web page wrote that:
In 2018, Chengdu 404 deployed a hacking campaign to collect information on people involved in Hong Kong's democracy movement, on a U.S. media company that reported harsh treatment of minority Uighurs in China, and on a Tibetan Buddhist monk.
The charges however, did not indicate any direct political motivations behind the hackers' hacking activities, despite they were able to access some government computer systems in India and Vietnam.
The filings also did not indicate how the information was used.
The seven face a range of charges including computer and wire fraud, identity theft, money laundering, and racketeering.
"The cyber threat is not a problem that any one agency can address by itself," the FBI said.
"In addition to arresting warrants for all of the charged defendants, in September 2020, the U.S. District Court for the District of Columbia issued seizure warrants that resulted in the recent seizure of hundreds of accounts, servers, domain names, and command-and-control (C2) 'dead drop' web pages used by the defendants to conduct their computer intrusion offenses," the Department of Justice said.
When the announcement was made, the five Chinese remain at large but the two Malaysians were arrested by Malaysian authorities in Sitiawan, a region in Manjung District in Malaysia, on September 14, 2020.
The United States is seeking for their extradition.
Zhang and Tan have been charged with 25 counts of computer fraud and money laundering, which carry a maximum sentence of 20 years in prison. Jiang, Qian, and Fu face similar charges with nine counts that carry a maximum sentence of 20 years in prison.
The indictment against Wong and Ling charges the defendants with 23 counts of similar charges. But since they were also involved in false registration of domain names, they are also facing a maximum sentence of 27 years of imprisonment for money laundering.
